The Medibank Ransomware Attack (Australia, 2022)
In October 2022, Australians woke up to headlines that one of the country’s biggest health insurers, Medibank, had been hacked. At first it sounded like a routine cyber incident. Within days, it became clear that this was something far more serious.
Personal details and deeply private health information for about 9.7 million people were now in the hands of a criminal gang willing to leak it to the world. This was not just another name and email breach. It was a data hostage situation built on diagnoses, treatment codes, and health claim histories.
The attackers later published files under labels like “naughty list” and “good list”, with subfolders such as “abortions” and “mental health”, deliberately designed to shame people and create maximum public pressure.
The Medibank incident became a defining case in Australia’s cyber history, raising urgent questions about credential security, data retention, and how far governments should go in sanctioning foreign hackers.
First time seeing this?
⚙️ How the Attack Worked
Later investigations by the privacy regulator reconstructed a classic but devastating intrusion chain.
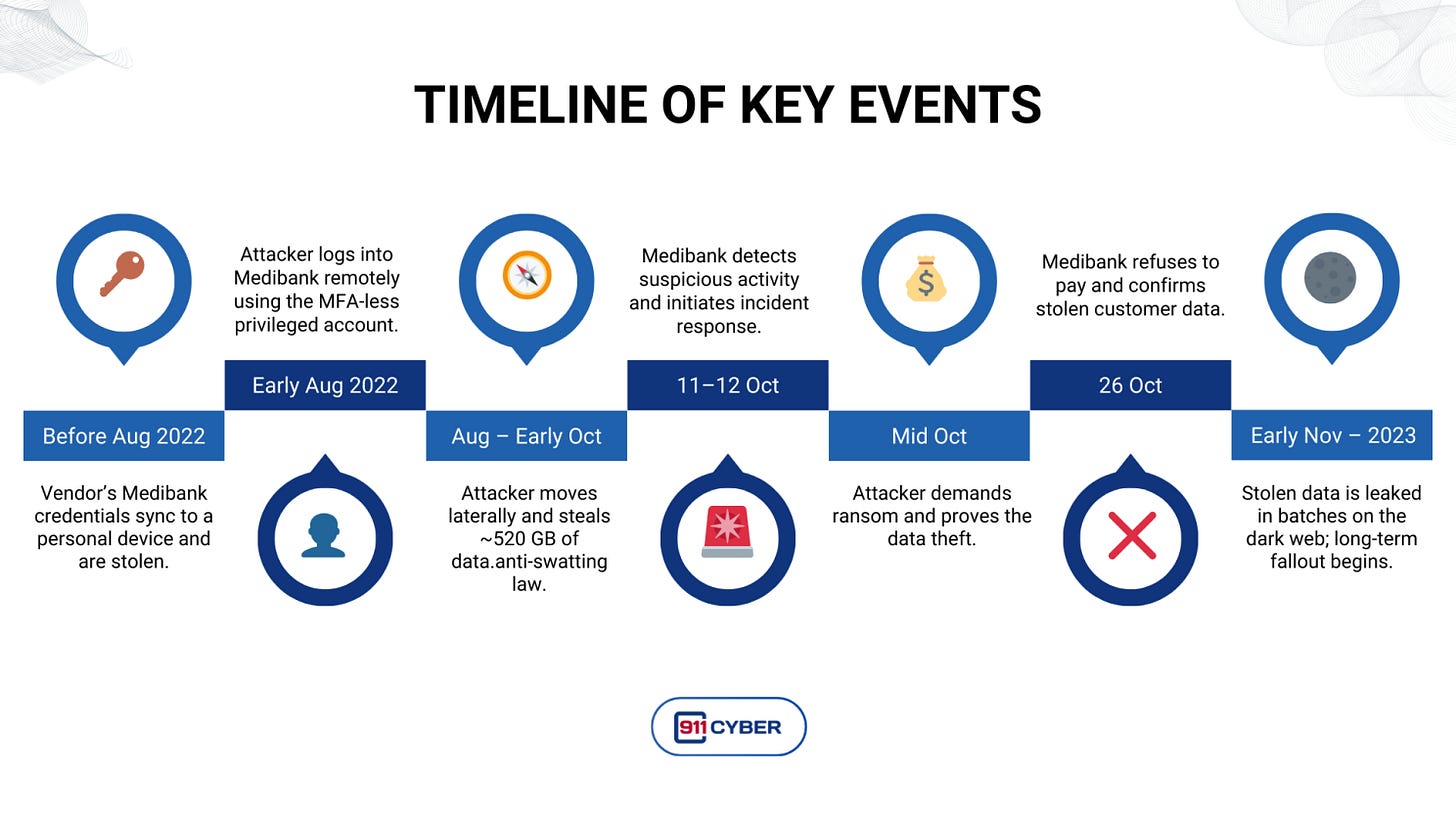
1. A vendor credential that escaped the perimeter
Before August 2022, an employee of a third party IT provider working for Medibank saved their Medibank access credentials into a browser profile on a work computer. That browser profile synced to a personal device outside the corporate environment. Attackers then obtained those credentials from outside the organisation.
2. Privileged access without multi factor authentication
Using the stolen credentials, the attacker remotely accessed Medibank’s network from early August 2022. The account had privileged access but was not protected with multi factor authentication. The regulator now alleges that this lack of MFA on a high privilege remote account was a key failure.
3. Weeks of quiet lateral movement
Once inside, the intruder moved laterally through Medibank’s systems over several weeks. They enumerated databases, explored storage, and identified where customer and claims data lived. By October, they had located large datasets and exfiltrated around 520 GB of information out of Medibank’s environment.
4. Detection, then a grim realisation
Medibank detected suspicious activity around 11 to 12 October 2022. The company brought in CrowdStrike and other incident response partners and took systems offline to contain the intrusion. Initially, Medibank believed no customer data had been removed. That view changed quickly once the attackers started contacting the company directly and proving what they had stolen.
Technically, the attack was less about a sophisticated exploit and more about:
Credential theft at a vendor
No enforced MFA on privileged remote access
Inadequate monitoring while the attacker explored the network
It was the kind of path that threat models warn about, but in a high volume, outsourced environment, small cracks can remain invisible until someone walks straight through them.
🗓️ Timeline: August 2022 to Early 2023
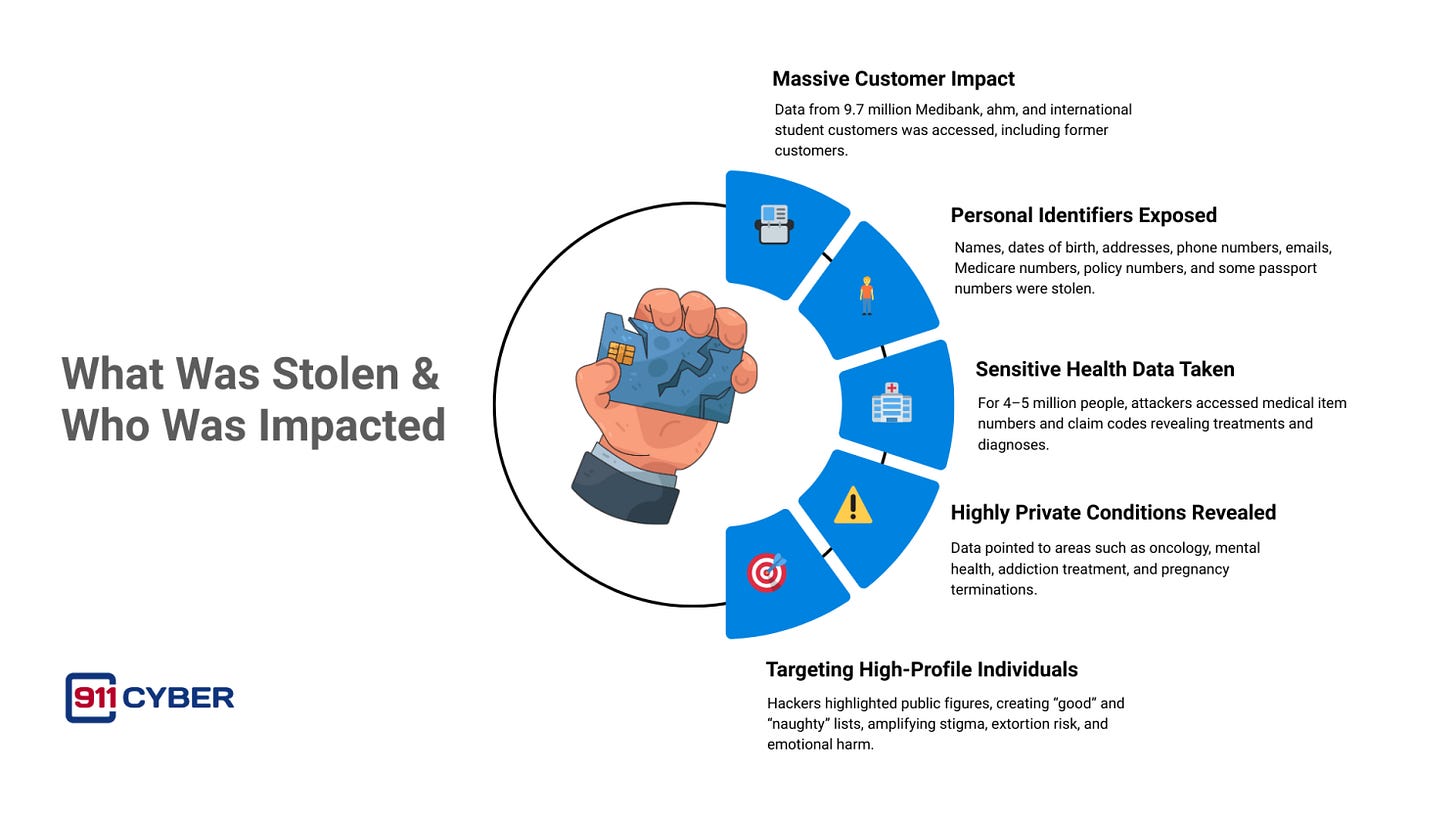
🌍 What Was Stolen and Who Was Impacted
The scope of data stolen was enormous in both volume and sensitivity.
The attackers accessed data across Medibank, its budget brand ahm, and international student health products, affecting roughly 9.7 million current and former customers.
Two broad categories of data were involved.
1. Personal Identifiers For millions of people, the breach exposed standard identity information, including:
Full names
Dates of birth
Home addresses
Phone numbers
Email addresses
Medicare card numbers
Policy numbers
Some passport numbers
2. Sensitive Health and Claims Data For around 4 to 5 million people, the attackers accessed parts of health claims data, including:
Medical item numbers
Claim codes that point to diagnoses, procedures, or treatments
These codes can reveal:
Oncology treatments
Mental health care
Addiction treatment
Pregnancy terminations and related services
3. High profile and high risk groups The dataset included records for high profile individuals and public figures. The attackers highlighted some of these in their leaks, claiming to have a “naughty list” of people with issues such as drug or alcohol problems and a “good list” of those with less stigmatised conditions.
Unlike some other breaches, payment card data was not taken. However, the combination of identity information and health claims created a perfect storm for identity theft, targeted phishing, extortion, and emotional harm.
🧠 Unmasking the Attacker
For many months, the Medibank attackers were known only by online handles and their association with a dark web leak site.
Investigators suspected links to Russia based ransomware operations, possibly connected to the REvil ecosystem, based on language used in communications and technical overlaps in infrastructure.
In January 2024, the Australian government went public.
Officials named Aleksandr Gennadievich Ermakov, a Russian national, as responsible for the Medibank attack. Authorities stated that Ermakov was linked to the REvil ransomware syndicate, which is known for multiple high profile extortion operations.
Australia used its new cyber sanctions powers to:
Impose financial sanctions on Ermakov
Restrict his ability to travel and access assets under Australian jurisdiction
Sanction entities that provided infrastructure used in the attack
This was the first time Australia had used cyber sanctions in response to a specific cyber incident.
Because Ermakov is believed to reside in Russia, an arrest or extradition is unlikely in the short term. The sanctions serve to:
Publicly identify the attacker
Limit his ability to operate internationally
Signal that Australia is willing to use diplomatic and economic tools against cybercriminals
The Medibank case thus sits at the intersection of traditional ransomware activity and international cyber policy.
🏢 Medibank Response
Medibank’s incident response unfolded in stages.
Immediate technical response Once suspicious activity was detected in October 2022, Medibank:
Took systems offline and restricted access
Engaged CrowdStrike and other specialist firms to investigate
Worked to identify the source and scope of the intrusion
Initially the company believed that no data had been exfiltrated. This position shifted as the attacker provided samples and later published the stolen data.
Customer and stakeholder management As the scale of the breach became clear, Medibank:
Notified affected customers and the public
Coordinated with regulators, law enforcement, and government agencies
Implemented support measures for impacted individuals, including guidance on identity protection and fraud risks
The company also began a broader uplift of its cyber security controls, with increased investment in monitoring, access control, and governance.
Reputational and business impact In the first month after the attack, Medibank lost more than twelve thousand customers and experienced a slowdown in new customer growth. While market share later started to recover, the brand took a significant reputational hit.
The CEO faced intense public scrutiny for:
The initial security weaknesses, including lack of MFA
The decision not to pay the ransom even as deeply sensitive data was being leaked
Medibank maintained that refusing to pay was the right long term decision, arguing there was no guarantee the data would ever be deleted and that paying would motivate further attacks.
🎯 Government and Public Reaction
The Medibank incident landed in a political landscape already shaken by the Optus breach a month earlier.
Key elements of the government and public response included:
Strong public statements condemning the attackers and acknowledging the harm done to individuals
Guidance to media outlets urging them not to republish sensitive medical details from the leaked datasets in order to reduce secondary harm
Close coordination between federal and state agencies to help affected individuals manage identity risks
The Medibank case also reinforced emerging policy themes:
The need for stronger safeguards over critical and sensitive data
The importance of data minimisation and shorter retention periods
The value of having cyber sanctions and international cooperation tools available to respond to offshore attackers
Medibank became a reference point in public debates about how organisations should balance ransom decisions, victim support, and national security considerations.
⚖️ Legal and Regulatory Fallout
The legal and regulatory consequences of the Medibank breach have been extensive and are still unfolding.
OAIC investigation and Federal Court action
In October 2022, the Office of the Australian Information Commissioner (OAIC) opened a formal investigation into Medibank’s handling of personal and health information.
On 5 June 2024, OAIC filed civil penalty proceedings in the Federal Court. The Commissioner alleges that Medibank seriously interfered with the privacy of about 9.7 million people by failing to take reasonable steps to protect their data, including not enforcing multi factor authentication and not limiting access appropriately.
Under the Privacy Act settings at the time, the court can impose up to 2.22 million Australian dollars per contravention. Treating each individual or group as a separate contravention produces a theoretical maximum in the trillions of dollars, although any real penalty will be far lower and proportionate but still potentially very significant.
APRA oversight
APRA, the prudential regulator, reviewed Medibank’s risk management, governance, and incident response.
The regulator required improvements to cyber controls, risk frameworks, and oversight of technology and data security.
Class actions and representative complaints Multiple legal actions have been brought on behalf of affected customers:
A group proceeding in the Supreme Court of Victoria alleges that Medibank failed to adequately secure personal and health information, allowing hackers to exfiltrate and publish it online.
Law firms have made representative complaints to OAIC seeking compensation for Medibank and ahm members, arguing that the insurer breached its Privacy Act obligations.
The privilege battles As part of these actions, plaintiffs sought internal incident response and forensic reports produced by Deloitte, CrowdStrike, and CyberCX.
Medibank argued that many of these documents were protected by legal professional privilege.
In 2025, the Federal Court handed down mixed rulings, requiring Medibank to hand over some materials while upholding privilege for others.
These decisions highlighted how difficult it can be to maintain privilege where reports serve multiple purposes, such as legal advice, regulatory reporting, and public communications. The outcomes in Medibank will influence how Australian organisations structure their incident response and documentation in future breaches.
🧩 Aftermath and Legacy: 2023 to 2025
The Medibank attack has had a long tail that extends beyond the immediate incident.
1. A national example of health data risk
The case is now frequently cited in discussions about:
The unique sensitivity of health information
The compounded risk when health data is linked with identity documents
The need to treat such data as a toxic asset rather than a convenient archive
2. A push toward data minimisation
Regulators and privacy advocates have used Medibank as a case study in why organisations should not retain data indefinitely.
Many of the victims were former customers whose data was still stored.
Post incident guidance has focused on deleting or de identifying information when it is no longer strictly required.
3. Stronger expectations for vendor access control
Boards and executives now pay closer attention to:
How vendor accounts are controlled and audited
Where credentials may be stored or synced
Whether MFA is enforced on all remote and privileged accounts
4. Clarifying ransom and leak strategies
The highly public nature of the Medibank extortion attempt has driven more organisations to:
Articulate a clear policy position on paying ransom
Prepare communication and victim support strategies for partial or full data leaks
Integrate law enforcement engagement into their plans from the outset
5. Legal benchmarks for privacy and cyber due diligence The Federal Court and OAIC proceedings will help define what counts as “reasonable steps” to protect data in a large, complex organisation that handles sensitive information. Outcomes in these cases are expected to set important expectations for industries beyond health insurance.
🛡️ How This Could Have Been Prevented
🕊️ Final Takeaway
The Medibank ransomware attack was not just about systems going offline or data being copied. It was about the weaponisation of the most private details of people’s lives.
One compromised vendor credential, a lack of multi factor authentication, and weak monitoring gave an attacker weeks of free movement inside a major health insurer. The result was a breach that exposed nearly 9.7 million people to identity fraud, public shame, and long term anxiety about how their information might be used.
Yet the incident also accelerated change. It pushed regulators, boards, and governments to confront the reality that health and identity data are not ordinary assets. They are deeply personal and must be protected accordingly.
Medibank serves as a stark reminder that cybersecurity is not only about technology. It is about trust, dignity, and the duty of care owed to every person whose data an organisation holds.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: