In late September 2025, parents at nurseries operated by Kido International woke to a parents worst nightmare. Images, names and home addresses for children who attend the group’s London sites were posted on the dark web and attackers demanded payment. A criminal crew calling itself Radiant published profiles for 10 children as proof and threatened to publish many more unless Kido paid. The incident prompted a police and regulator response and left thousands of families scrambling for practical steps to protect their children and themselves.
First time seeing this?
What Was the Kido Incident
A data theft and extortion campaign targeted Kido International’s UK operations in the week of 25 to 26 September 2025. Attackers identifying as the Radiant group claim to have stolen profile data for roughly 8,000 children who attend Kido nurseries in Greater London and posted sample records on a dark web leak site to pressure the company. Kido runs 18 UK sites, 17 in London and one in Windsor, and it has locations overseas including India, China and the United States. The breach appears to be focused on the UK estate.
Key facts
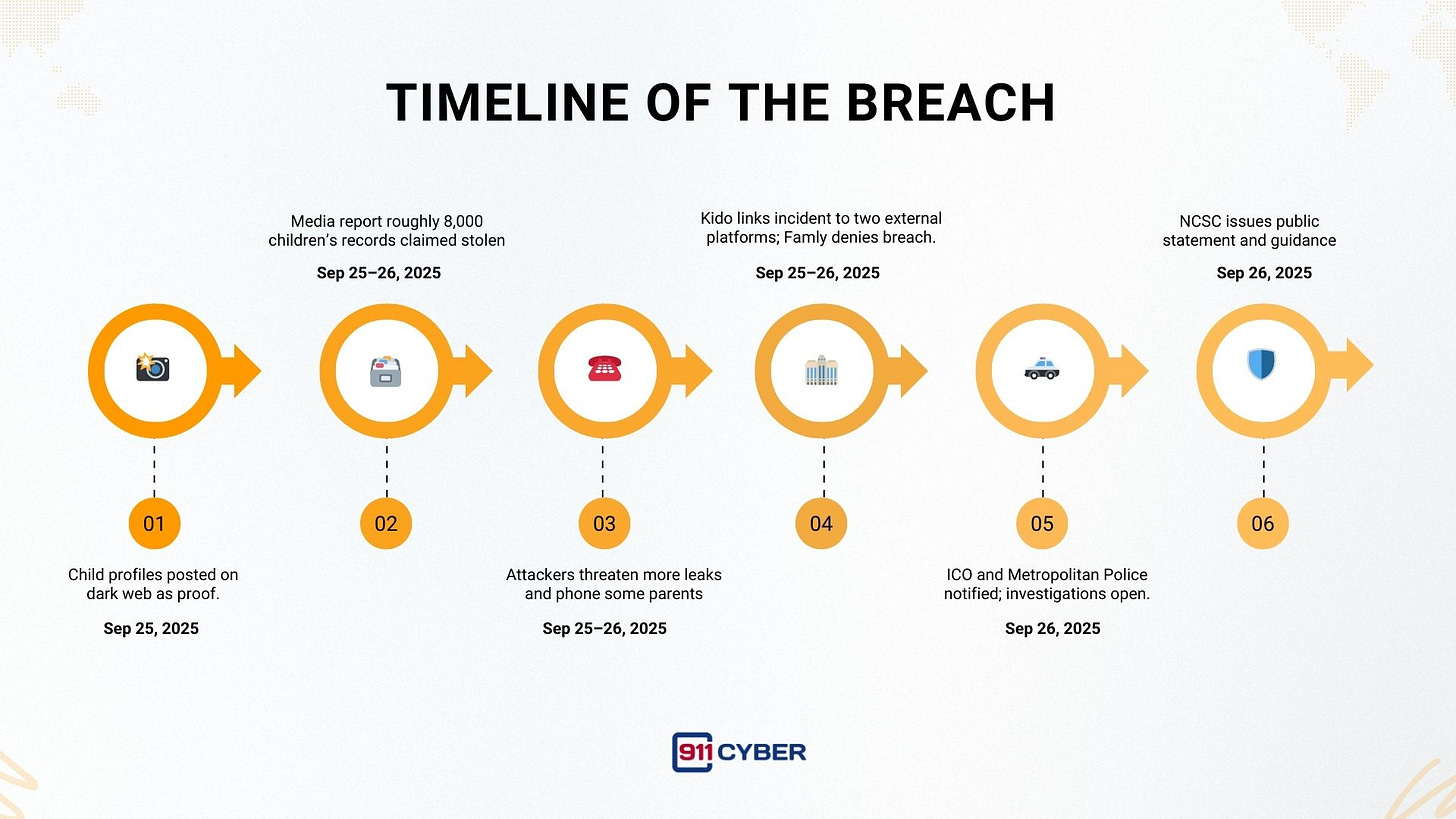
Disclosures began: 25 to 26 September 2025.
Attacker: A newly emerged group calling itself Radiant. The group publicly posted 10 child profiles and threatened further releases.
Estimated scope: Media reporting cites roughly 8,000 children’s records taken from Kido’s UK sites.
Stolen items claimed: Child names, dates of birth, profile photos, home addresses and parents contact information. Attackers also claim to hold safeguarding notes, medical and accident reports, medication logs and billing records.
Organisations notified: Metropolitan Police Cyber Crime Unit, the Information Commissioner’s Office and Ofsted. The UK National Cyber Security Centre described the attack as deeply distressing.
Vendor context: Kido told investigators the compromise involved two external software platforms used by the nurseries. Reporting highlights Famly, a common childcare portal for photos and daily reports. Famly has stated that it found no breach on its own infrastructure, which suggests the compromise occurred on Kido’s side or via tenant credentials rather than via a failure of Famly’s core systems.
How the Attack Worked
The incident was data theft used for extortion. The attackers published sample child profiles on a dark web leak site and demanded payment from Kido.
The group that posted the samples identified itself as Radiant and published ten child profiles as proof.
Public reporting and Kido’s statements place the disclosure in the week of 25 to 26 September 2025 and say the company’s UK operations were affected. Reports estimate roughly 8,000 children’s records were taken from Kido’s London nurseries.
Kido has told investigators that the compromise involved two external software platforms used by the nurseries. One vendor named in reporting is Famly. Famly has stated that it found no breach of its own infrastructure. Those vendor and company statements are publicly recorded.
News outlets reported that the attackers used pressure tactics beyond the leak site, including phoning some parents to encourage them to press Kido to pay.
What Was Stolen
Names, photos and home addresses are durable personal identifiers that cannot be changed like a password. Safeguarding notes and medical records add privacy and safety risk because they reveal vulnerabilities that could be abused for targeted harassment, doxxing or social engineering.
Who Did It
A group calling itself Radiant claimed responsibility. Reporting describes Radiant as a nascent ransomware and extortion group that sought publicity for this incident and used a dark web leak site to pressure Kido. Some members of the group referred to the intrusion as an unauthorised penetration test for which they expected compensation.
There is no authoritative public attribution to a nation state or to a previously known criminal syndicate at the time of reporting.
Timeline
Legal and Regulatory Outcomes to 2025
Notifications and investigations: Kido reported the incident to the ICO and the Metropolitan Police. Ofsted was informed. The ICO will assess whether to pursue enforcement action or fines under UK data protection law based on the company’s security posture and incident response.
Civil risk: News reports indicated that affected families were being encouraged to consider legal action against Kido. Group litigation or class actions are possible depending on regulator findings and the confirmed scope of impact.
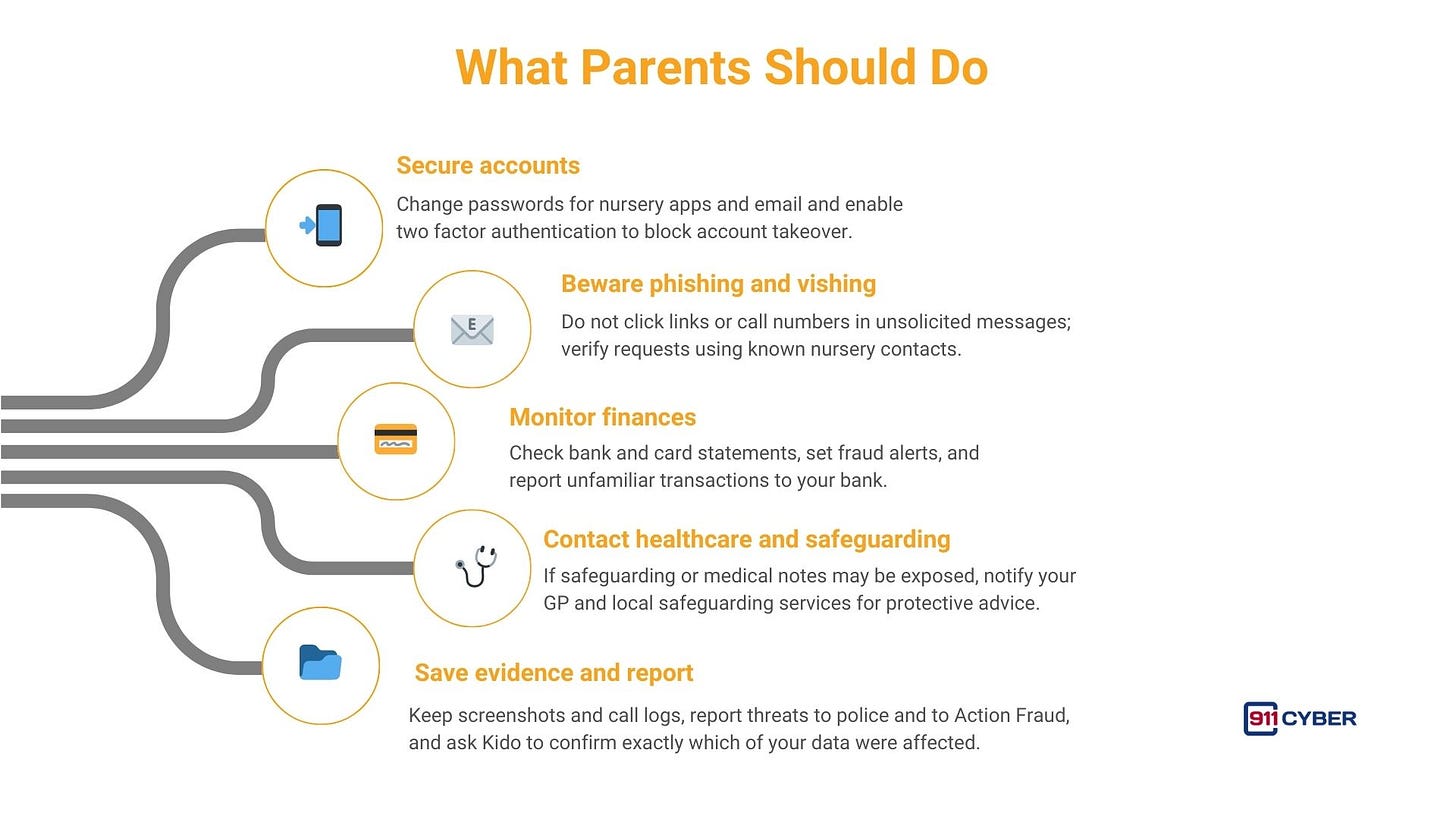
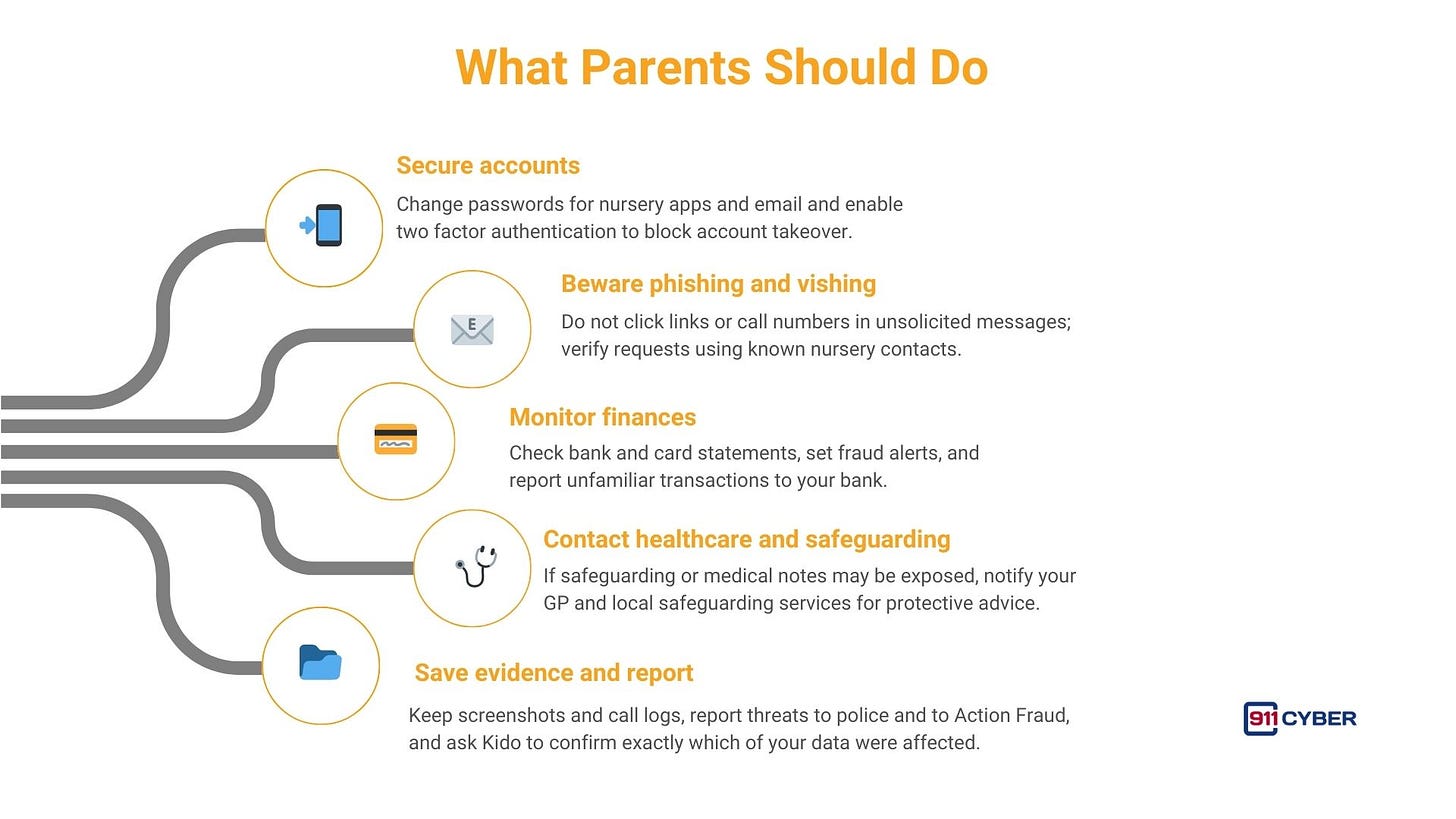
What Parents and Carers Should Do
Final Takeaway
The Kido incident is a sobering reminder that personal and sensitive records for the most vulnerable are attractive to extortionists because of the immediate emotional leverage they provide. The breach demonstrates how vendor-linked data and tenant-side controls can be exploited. There is no quick fix for exposed identities, so prevention, fast detection and clear compassionate communication to affected families are the lasting defenses.
Regulators and police are investigating. Affected families should prioritise account security, remain vigilant for scams and insist on clear updates from Kido and the authorities while legal and forensic processes continue.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: