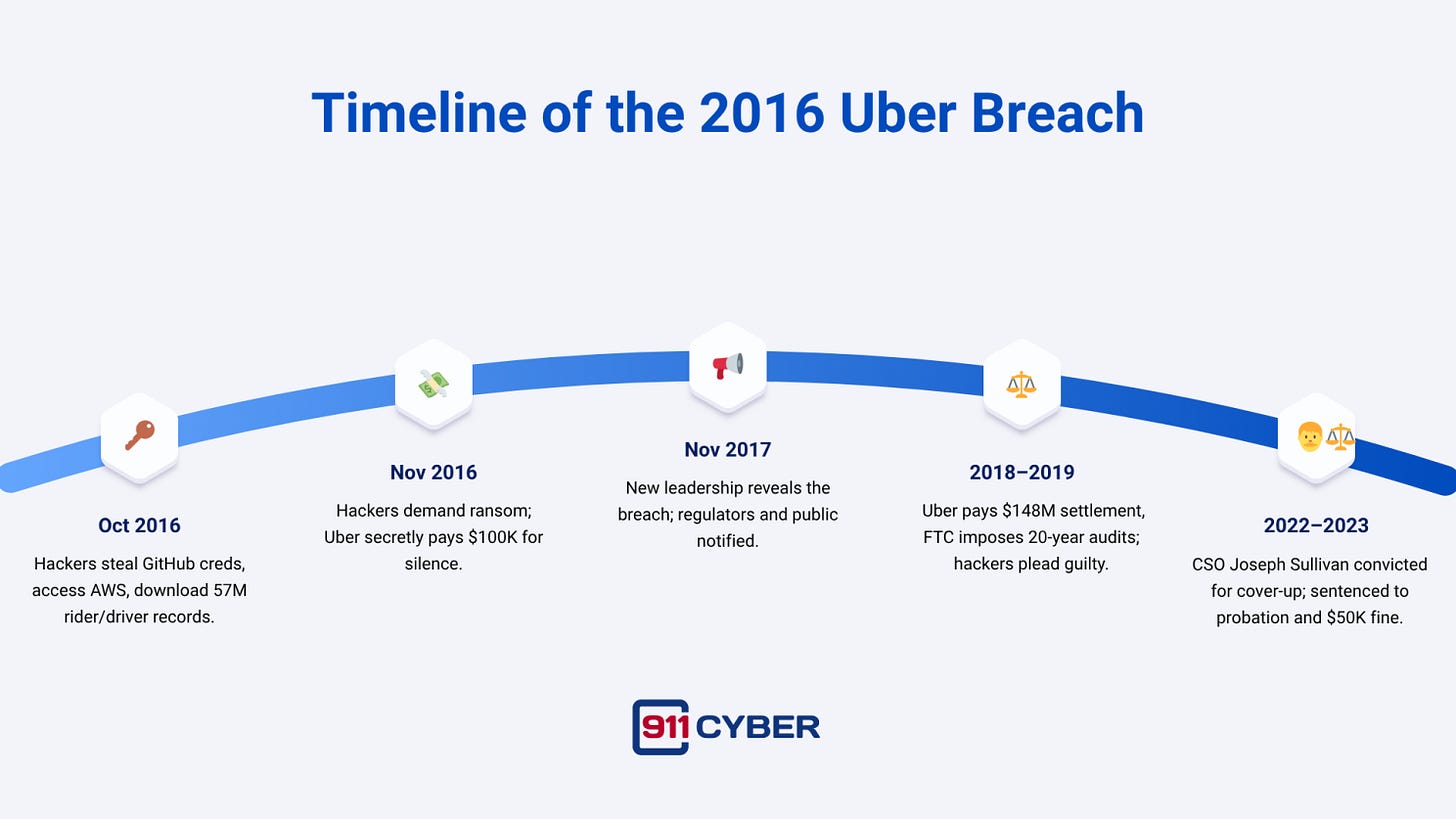
In October 2016, Uber suffered a massive data breach that compromised 57 million rider and driver accounts worldwide. The attack exposed not only personal data but also critical weaknesses in Uber’s cloud security practices. Instead of notifying regulators and users, Uber’s leadership attempted to keep the incident secret. Hackers were paid $100,000 in Bitcoin under the guise of a bug bounty program, and they signed nondisclosure agreements claiming the data had been deleted.
For more than a year the breach remained hidden, until new CEO Dara Khosrowshahi disclosed it publicly in November 2017. The revelation set off one of the most consequential cybersecurity scandals in recent history, involving criminal prosecutions, sweeping regulatory settlements, and long-term changes to how companies respond to breaches.
First time seeing this?
How the Breach Happened
The attackers targeted Uber’s software development ecosystem. Using stolen GitHub credentials, they discovered an exposed AWS access key embedded in Uber’s code. With that single key, they accessed Uber’s Amazon S3 cloud storage where user data was kept. Security experts later criticized Uber for leaving sensitive data unencrypted and storing credentials in plaintext, practices that made the breach both possible and devastating.
By mid-November 2016, Uber’s security team confirmed the theft. Hackers contacted CSO Joseph Sullivan and demanded money. Sullivan approved the payout through Uber’s bug bounty program to disguise the ransom as a legitimate payment to “researchers.” The deal included nondisclosure agreements, but Uber’s own investigators admitted the data had already been copied in full.
What Data Was Taken
Although Uber later claimed no fraud arose from the stolen records, regulators emphasized that the company had left personal identifiers unprotected and hidden the incident for more than a year.
The Hackers Behind the Breach
The attackers were identified in early 2017 as Brandon Charles Glover of Florida and Vasile Mereacre of Toronto. Both men admitted to conspiring to extort Uber and another company by stealing AWS credentials. They delivered a sample of the stolen Uber data as proof and demanded payment for deleting the rest.
In October 2019, both pleaded guilty to federal charges. Glover received eight months of home confinement, and Mereacre received a similar sentence. Their relatively light penalties reflected cooperation with authorities and their early guilty pleas.
Uber’s Response and the Cover-Up
Internally, Uber’s leadership took immediate technical steps to secure cloud keys, reset employee passwords, and disable compromised accounts. But rather than alert regulators or users, CSO Joseph Sullivan and others prioritized secrecy. Internal communications later revealed Sullivan telling his team that “we can’t let this get out.”
This strategy backfired. When Dara Khosrowshahi became CEO in 2017, he uncovered the concealed breach and immediately disclosed it. Sullivan was terminated, and Uber began cooperating with authorities. Khosrowshahi described the cover-up as a betrayal of trust, pledging reforms to rebuild Uber’s credibility.
Timeline
Legal and Regulatory Fallout
The breach triggered sweeping regulatory action.
United States: In September 2018, Uber agreed to a $148 million settlement with attorneys general from all 50 states and D.C., the largest privacy settlement of its kind at the time. The Federal Trade Commission extended oversight through a 20-year privacy and security program with independent audits. In July 2022, the Department of Justice reached a non-prosecution agreement with Uber, acknowledging the concealment but crediting the company’s later cooperation.
International: The UK Information Commissioner’s Office fined Uber £385,000, while the Dutch Data Protection Authority imposed a €600,000 penalty. France’s CNIL added a €400,000 fine in 2019. Each authority cited the delayed disclosure and inadequate data protections.
Criminal Trials: Sullivan’s prosecution was historic. Convicted in October 2022 of obstruction of justice and misprision of felony, he became the first corporate security executive held personally liable for concealing a breach. In May 2023, he was sentenced to three years of probation and fined $50,000. A federal appeals court upheld the conviction in March 2025, cementing the precedent that executives can be criminally accountable for hiding cyber incidents.
Lessons Learned
The Uber 2016 breach exposed 57 million records and became notorious not only for the data stolen but for the attempted cover-up. It remains a landmark case that highlights critical lessons in credential security, encryption, transparency, and executive accountability.
Final Takeaway
The Uber 2016 breach is remembered not just for the data stolen but for the attempt to hide it. The decision to treat an extortion demand as a bug bounty reshaped legal and regulatory expectations around disclosure. Today, the case is cited as a cautionary example in boardrooms and classrooms alike. Its legacy is clear: concealing a breach costs more than admitting one, and transparency is now a fundamental principle of corporate cybersecurity.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: