23andMe is one of the most widely used consumer DNA testing platforms in the world. Millions of people trusted it with something deeply personal, their genetic identity.
In 2023, that trust was quietly broken.
Over several months, attackers accessed and extracted data linked to approximately 6.9 million users, nearly half of 23andMe’s customer base. The breach happened through credential stuffing and feature abuse, turning a genealogy tool into a large-scale data scraping operation.
First time seeing this?
🧬 What happened
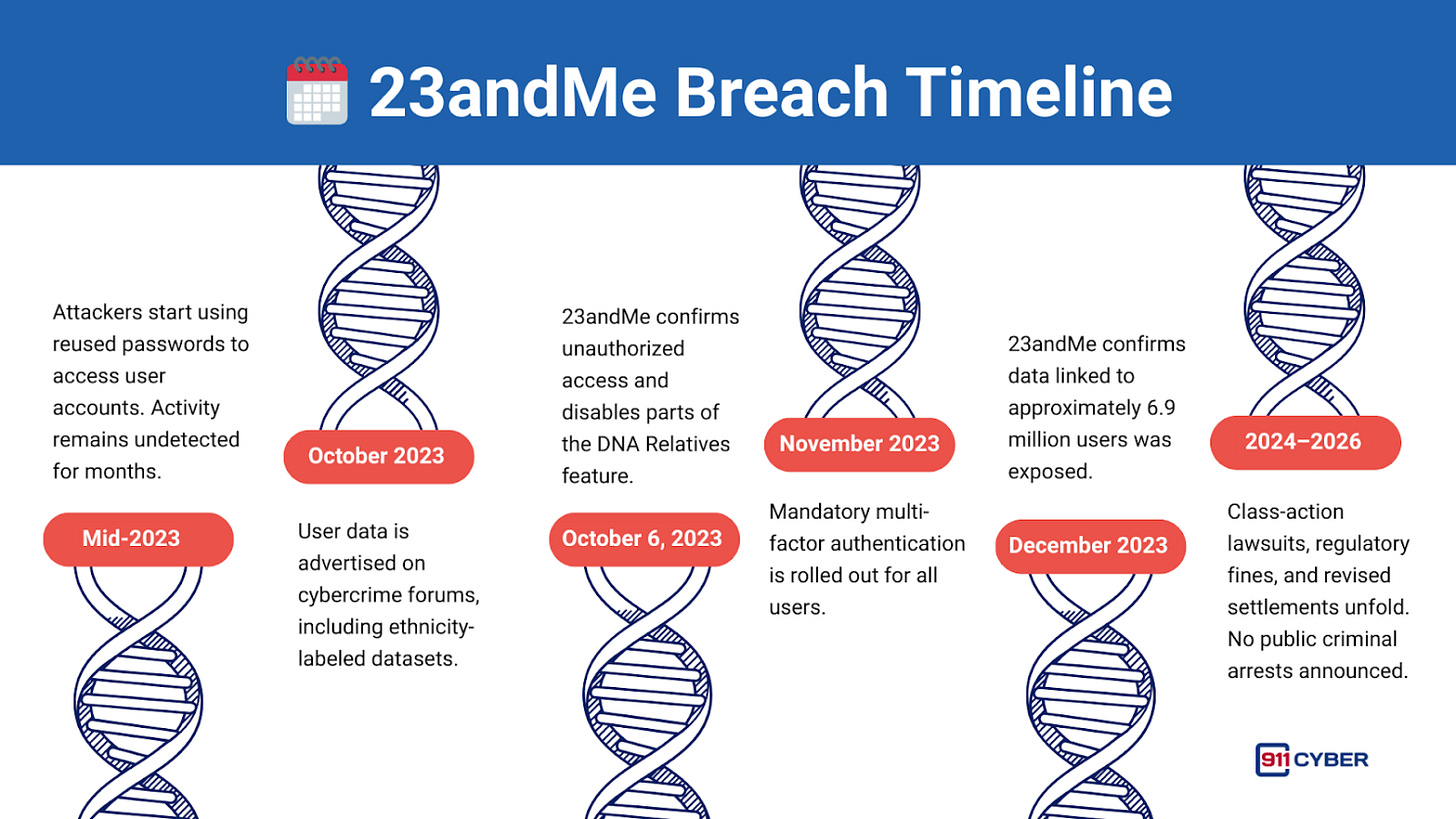
Attackers used login credentials stolen from other breaches to access about 14,000 23andMe accounts where users had reused passwords.
Once inside, they exploited the DNA Relatives feature, which allows users to view genetic matches and shared profile data. From a single compromised account, attackers could access hundreds of connected profiles, many belonging to people who were never hacked directly.
A small number of stolen passwords triggered a massive chain reaction.
🌊 How the Breach Unfolded
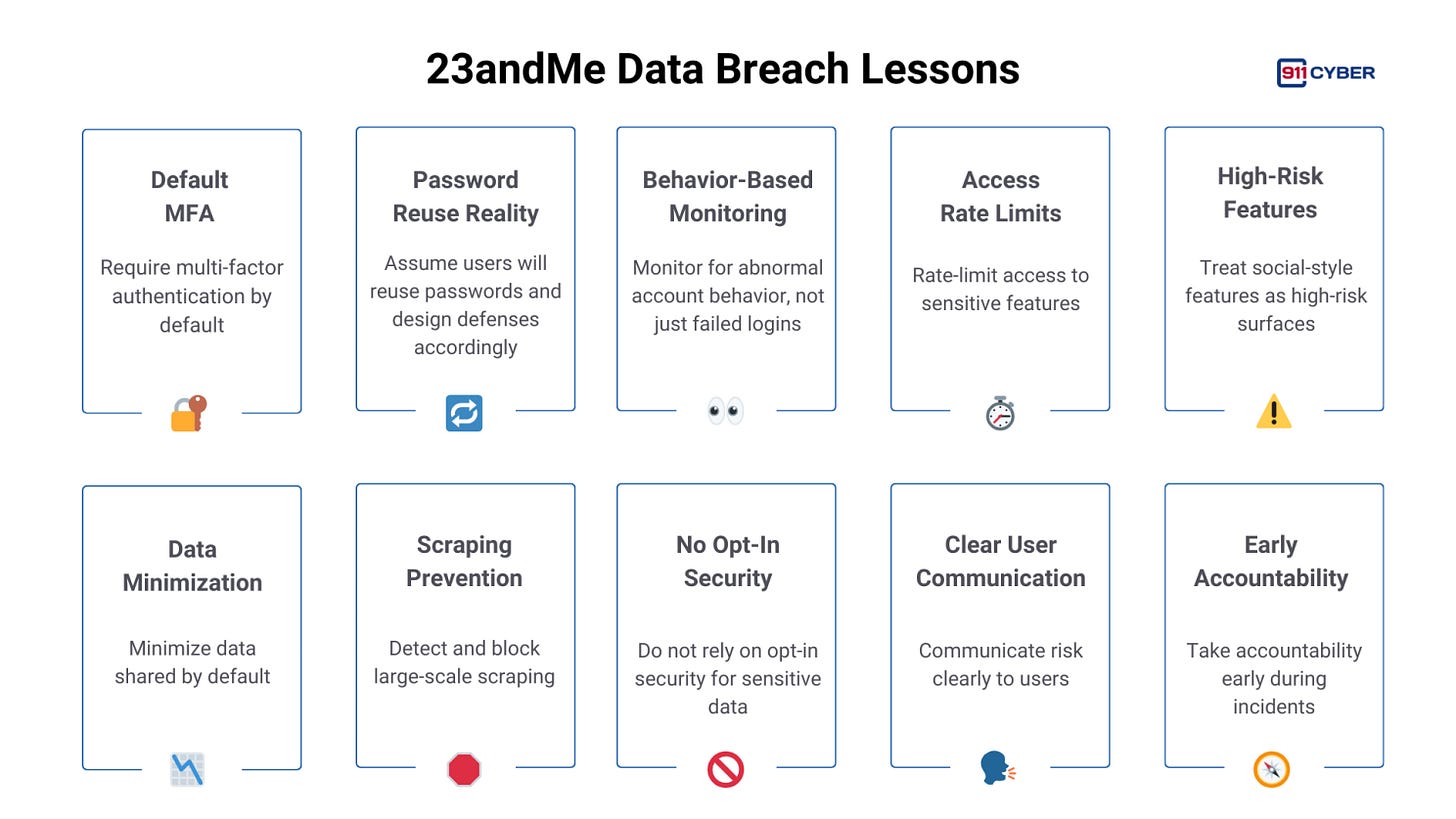
This was not a single event. It was a slow, distributed campaign that blended into normal user behavior. Login attempts were spread out over time. Data access looked legitimate. There were no strong rate limits or alerts to flag mass profile viewing.
Because attackers used valid accounts and built-in features, the activity went undetected for months.
🎭 Threat Actor Behavior
The breach became public when a threat actor using the alias “Golem” began selling stolen 23andMe data on BreachForums in October 2023.
What alarmed investigators was how the data was packaged.
Datasets were labeled by ethnicity, including roughly 1 million Ashkenazi Jewish profiles and 100,000 users of Chinese descent. Some listings even claimed to include celebrities and wealthy individuals.
While the motive appeared financial, the nature of the data raised fears of harassment, discrimination, and extremist misuse, especially amid rising global antisemitism at the time.
📊 What Data Was Exposed
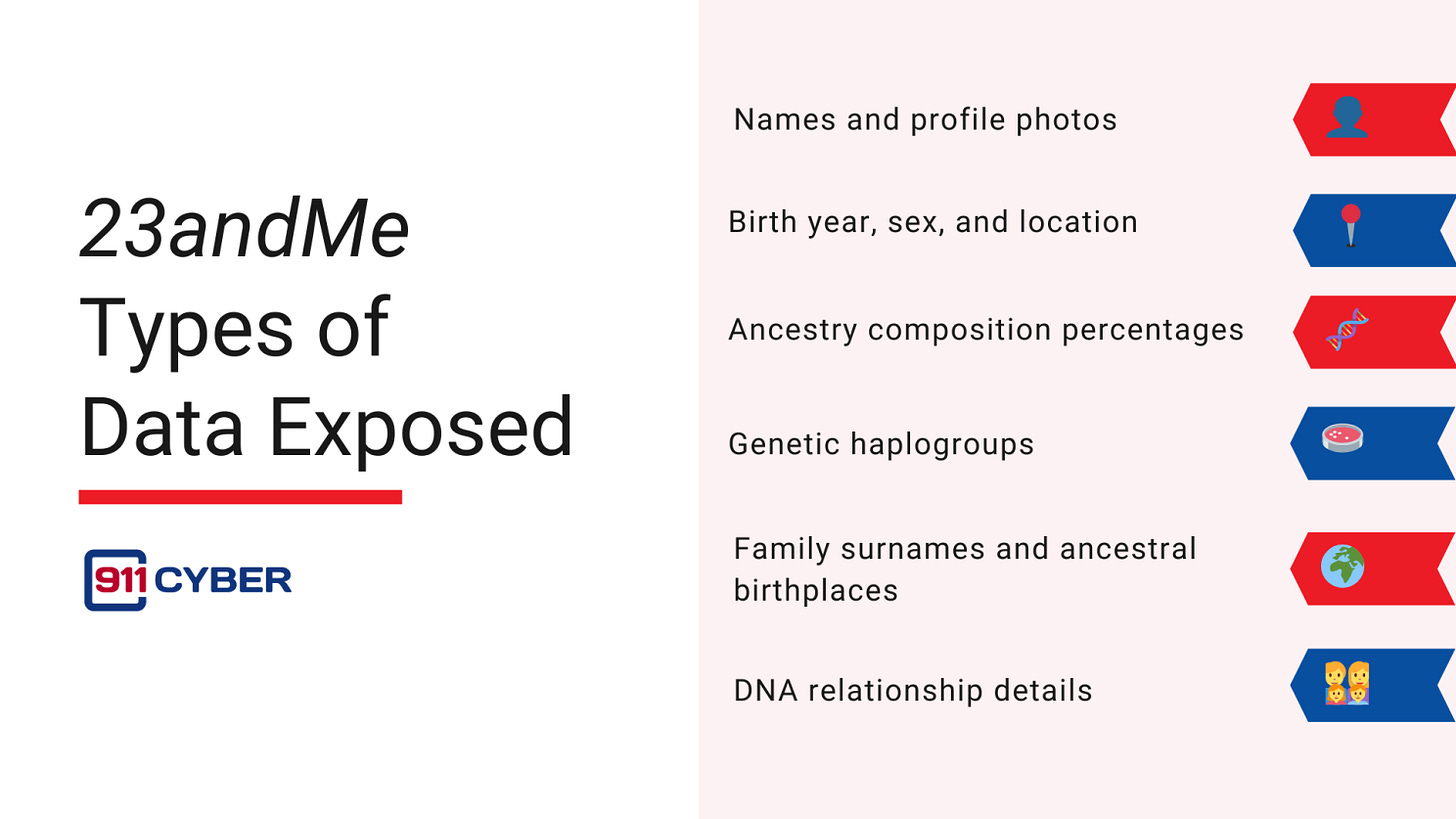
No raw DNA files were leaked. But the exposed data was still highly sensitive.
This information links people directly to their heritage and relatives, details that cannot be changed once exposed.
🚨 Impact on Users
The breach affected users worldwide, but its impact was uneven.
Ethnic communities, particularly Jewish and Chinese users, faced heightened risk due to the way their data was grouped and sold. Lawmakers warned the data could be used to identify and target individuals based on heritage.
Unlike financial breaches, this exposure was permanent. As mentioned earlier, genetic identity cannot be reset.
🛠️ 23andMe’s response
23andMe disabled parts of DNA Relatives, forced global password resets, and eventually made multi-factor authentication mandatory.
The company faced criticism for initially emphasizing user password reuse and later for updating its terms to limit lawsuits. Regulators in multiple countries concluded that basic security controls should have been in place earlier.
⚖️ Legal and Regulatory Fallout
The incident triggered significant legal and regulatory action.
In the U.S., multiple class-action lawsuits were filed beginning in October 2023, alleging negligence and failure to protect sensitive genetic data. A separate lawsuit filed in January 2024 focused on Ashkenazi Jewish and Chinese users, citing discriminatory harm from ethnicity-labeled data sales.
In September 2024, 23andMe agreed to a $30 million settlement to resolve the consolidated litigation.
Regulators also intervened. U.S. state attorneys general launched investigations, and members of Congress demanded answers, warning that genetic data cannot be changed like passwords.
Internationally, privacy regulators in Canada and the UK conducted a joint investigation, concluding that 23andMe failed to take basic security steps. The UK regulator issued a £2.3 million fine, reinforcing that genetic data requires heightened protection.
🔄 Updates as of 2026
Legal and financial developments continued into 2025 and early 2026.
In the United States, court filings in early 2026 reflect an expanded proposed settlement of up to $50 million, replacing earlier figures. This revised settlement is intended to cover a broader pool of affected users and provide extended privacy and identity monitoring services. Final court approval is pending.
In Canada, a separate class-action settlement valued at approximately CAD $4.49 million has been proposed to resolve claims brought by Canadian customers affected by the breach.
Corporate consequences also followed. In March 2025, 23andMe filed for Chapter 11 bankruptcy protection, citing financial pressure tied to litigation, regulatory penalties, and declining consumer trust. During the court-supervised restructuring process, multiple U.S. states raised objections regarding the handling and potential transfer of genetic data, emphasizing that such data should not be sold or transferred without explicit user consent.
Later in 2025, 23andMe’s assets were acquired through a court-approved process by an entity linked to the company’s co-founder, with public commitments made to maintain existing privacy protections.
As of early 2026, no public arrests or criminal charges have been announced against the individual or group responsible for the original credential-stuffing attack.
🧠 Lessons for Every Consumer Platform
🎬 Closing
This case underscores the importance of proactive security design, continuous monitoring, and strong authentication for any platform handling sensitive personal data. These measures are no longer optional. They are foundational.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: