Coupang is often described as Korea’s Amazon.
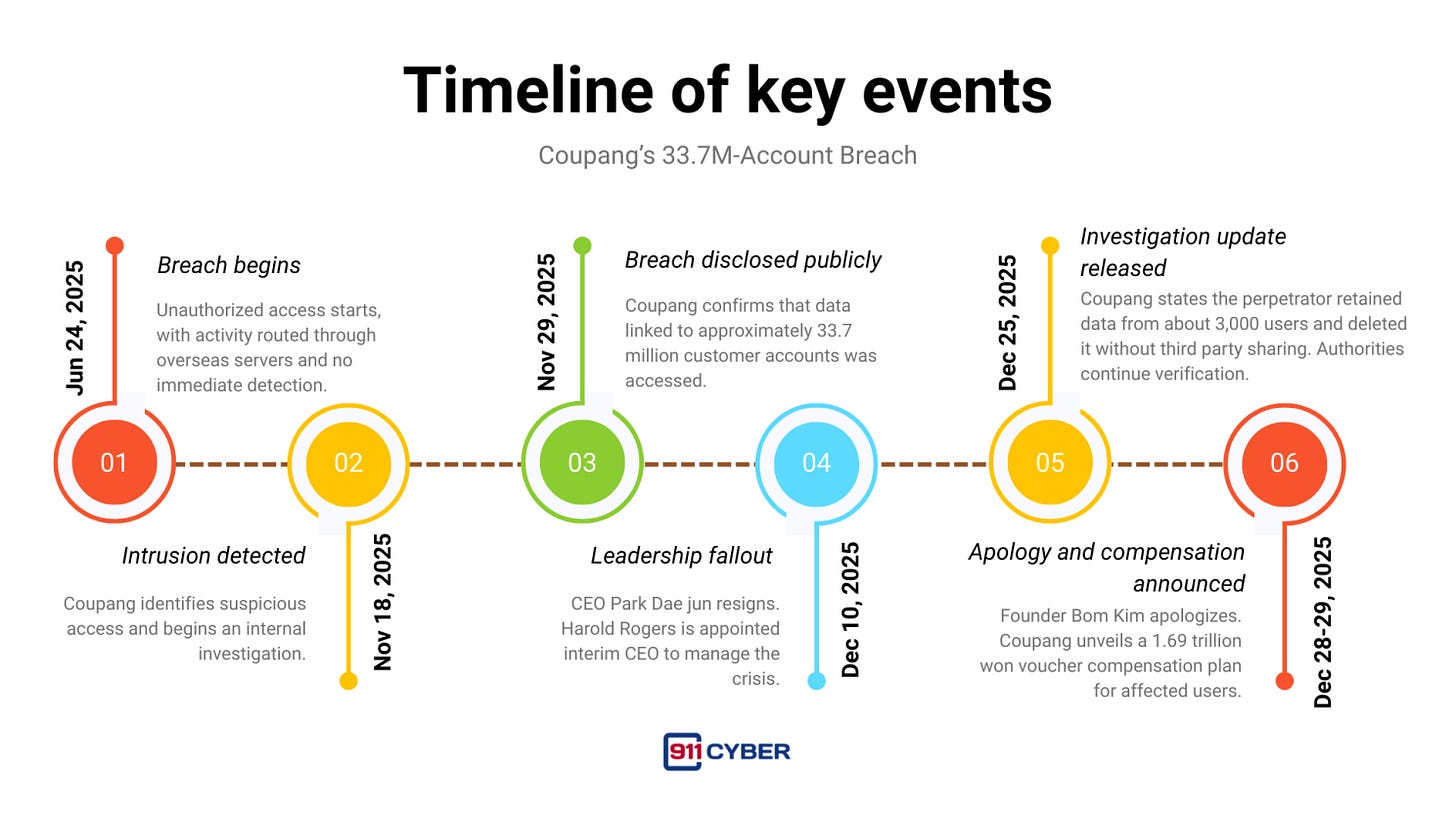
In late 2025, Coupang disclosed that personal information linked to approximately 33.7 million customer accounts had been accessed in a data breach. Investigators believe the intrusion began as early as June 24, 2025 and remained undetected until November 18, 2025.
What makes this incident stand apart from many retail breaches is how it happened. This was not password cracking. It was not malware deployed across devices. It was not a single exposed server. It was an authentication failure so severe that one stolen secret could be used to impersonate users at scale.
First time seeing this?
🔐 What happened
South Korean authorities described the intrusion as an abuse of authentication vulnerabilities. Reporting around the investigation indicates that a private encryption or signing key was stolen and used to generate or validate access tokens that appeared legitimate.
With this key, the attacker could access customer data without needing individual passwords.
Coupang stated that the incident involved unauthorized access to personal data such as names, contact details, shipping addresses, and parts of order history. The company maintained that payment information and login credentials were not affected.
🧩 How the breach likely unfolded
Based on public reporting and investigative disclosures, the breach followed a classic master key pattern.
A sensitive internal authentication secret was obtained.
The attacker abused authentication logic so that access requests appeared valid to security systems.
The activity was routed through overseas infrastructure and continued for months without detection.
Because the access looked legitimate, traditional perimeter defenses were ineffective. This highlights a critical weakness many modern organizations face. When authentication itself is compromised, detection must rely on behavioral analysis, rate limiting, and anomaly detection, not just login success or failure.
🧑⚖️ Attribution and recovered evidence
Reuters reported that a former Chinese employee of Coupang was under investigation in connection with the breach, citing Yonhap. Coupang later issued a detailed public update describing a perpetrator who claimed to have acted alone and stated that customer data was never transferred to third parties. Authorities publicly cautioned that some of the company’s claims were still under verification.
The investigation reached a turning point in mid December 2025 with the recovery of physical evidence. According to investigators, the former employee admitted to using a MacBook Air during the breach and then attempting to destroy evidence after the incident became public. The laptop was deliberately smashed, placed in a weighted canvas bag, and dumped into a river in an attempt to prevent recovery.
A specialized diving team was deployed to retrieve the submerged device. Despite severe physical damage and prolonged water exposure, forensic experts from Mandiant, Palo Alto Networks, and Ernst and Young successfully extracted and inventoried its contents.
Their analysis supported a critical claim. While access was made to approximately 33.7 million customer accounts, data was retained from only about 3,000 users. Investigators reported that this retained data was deleted after the breach became public and found no evidence of third party sharing or sale.
Authorities emphasized that verification remains ongoing, but the recovered laptop became a central piece of evidence in establishing attribution, technical method, and post breach behavior. Regardless of the final legal outcome, the incident stands as a textbook insider risk case, centered on privileged access, weak key management, and failures in offboarding and monitoring.
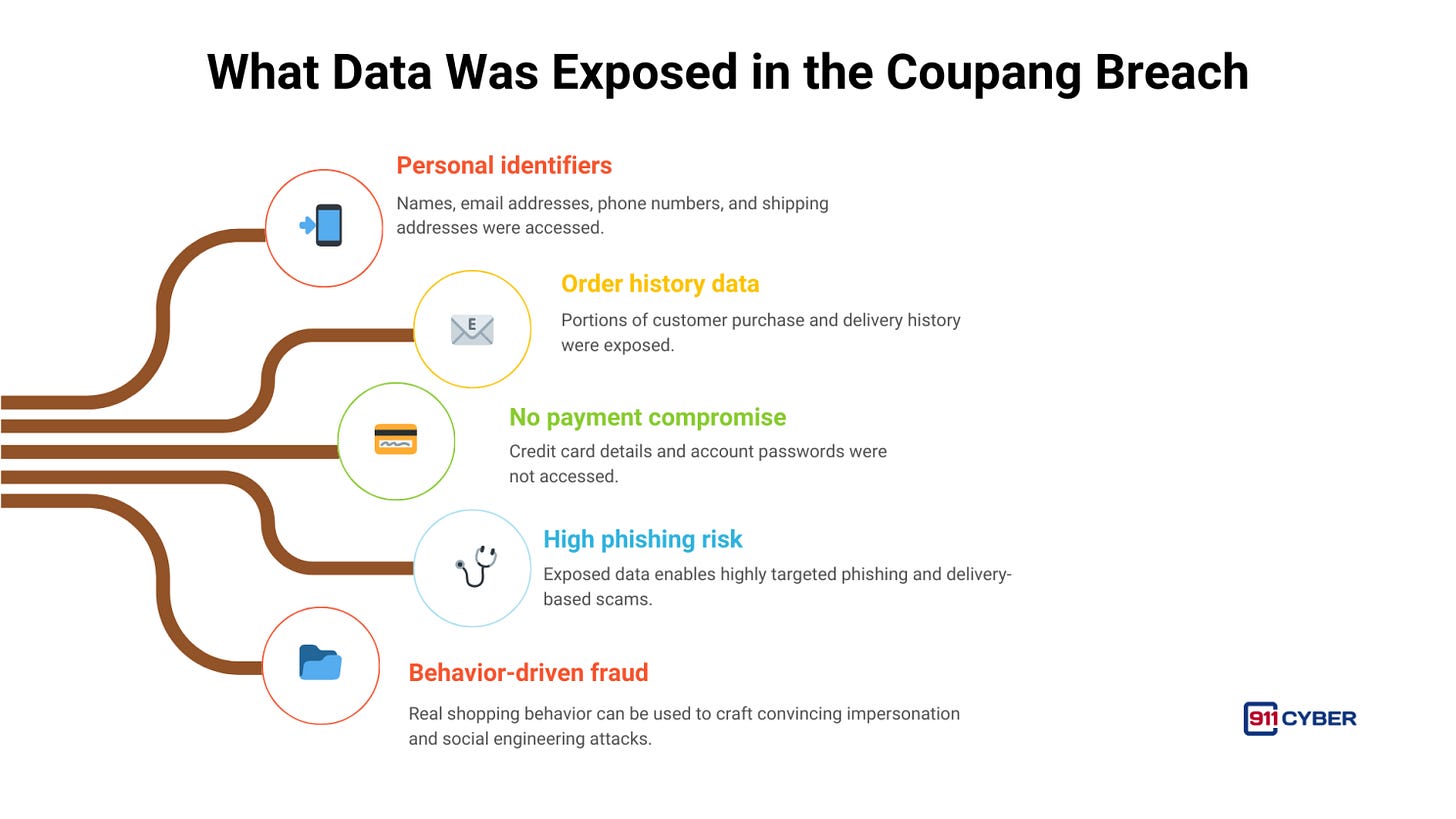
📂 What data was exposed
The breach did not come to light through internal detection systems. According to reporting and company disclosures, it was revealed after the suspect contacted Coupang directly to demand money, effectively attempting extortion. This outreach is what alerted Coupang’s security team and triggered the investigation. Without that demand, unauthorized access may have continued unnoticed.
Coupang later stated that the accessed data included names, email addresses, phone numbers, shipping addresses, and portions of order history. Payment details and account passwords were not exposed.
Even without financial data, this combination is highly valuable to cybercriminals. It enables targeted phishing, delivery scams, impersonation, and identity driven social engineering, especially when attackers can tailor messages using real shopping behavior.
🗓️ Timeline of key events
To understand the full impact of the Coupang breach, it helps to look at how the incident unfolded over time. The timeline below shows the gap between initial unauthorized access, public disclosure, leadership fallout, and the actions taken after the breach became known.
🚨 Impact on users
The breach triggered widespread concern because it exposed the most personal layer of e-commerce. Home addresses, phone numbers, delivery locations, and purchase behavior.
Authorities warned of heightened phishing and scam activity tied to the incident.
Even without payment data, large scale exposure of identity and delivery context enables convincing fraud scenarios such as fake missed delivery messages, account verification lures, compensation scams, and impersonation of Coupang support teams.
These are just a few of the ways secondary harm can unfold.
🛡️ Coupang’s response
Coupang engaged external incident response firms and issued multiple public updates. On December 25, the company claimed the suspect deleted retained data and did not transmit it to third parties. Officials cautioned that this conclusion was still under review.
The breach became a leadership crisis. The CEO resigned. An interim CEO was appointed. The founder later apologized publicly.
Coupang also announced one of the largest breach related compensation programs to date. Each affected user would receive 50,000 won in vouchers, totaling 1.69 trillion won. Lawmakers criticized the approach, arguing that vouchers for Coupang services effectively recycled compensation back into the company’s ecosystem.
⚖️ Regulatory and legal fallout
South Korea launched a formal inquiry into whether Coupang violated personal information protection laws.
President Lee Jae myung publicly called for tougher penalties and noted that fines could exceed 1 trillion won depending on investigative findings and revenue calculations.
Separately, the breach triggered investor scrutiny and legal action in the United States, adding further financial and reputational pressure.
🧠 Lessons for every consumer platform
This incident underscores how modern data breaches often stem from fundamental security failures rather than advanced exploits. The Coupang case highlights several non-negotiable principles that every consumer platform must treat as baseline requirements, not optional controls.
✅ Closing
Coupang’s breach wasn’t just large. It was structurally instructive.
When authentication itself becomes forgeable, the platform stops being a store and becomes an identity surface. And at Coupang’s scale, that identity surface touches most of a country.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: