Discord.io was a widely used third-party platform that allowed communities to generate custom invite links for Discord servers. It was not operated by Discord, but it sat close enough to the ecosystem that hundreds of thousands of users trusted it with account access and identity data.
In mid-August 2023, attackers breached Discord.io’s infrastructure, stole its entire user database of roughly 760,000 accounts, and immediately advertised the data for sale on a major cybercrime forum. Within hours of confirming the breach, Discord.io shut down all operations indefinitely, refunded paid subscriptions, and warned users that both non-sensitive and potentially sensitive data had been exposed.
Discord itself was not breached. Its systems remained secure, and the company publicly clarified that Discord.io was a completely separate service that did not receive user data from Discord.
First time seeing this?
🔑 What happened
In mid-August 2023, attackers compromised Discord.io, a third-party Discord invite-link platform, and exfiltrated its entire user database of roughly 760,000 accounts. The breach became public after the stolen data was advertised for sale on a cybercrime forum, with sample records shared to verify authenticity.
Discord.io confirmed the data originated from its production systems and shut down all services within hours. Premium subscriptions were canceled or refunded, and users were advised to assume their data had been exposed. The company acknowledged a code-level security failure and announced plans for a full rebuild.
As of 2026, Discord.io has not resumed operations. The breach remains the final confirmed operational event for the service.
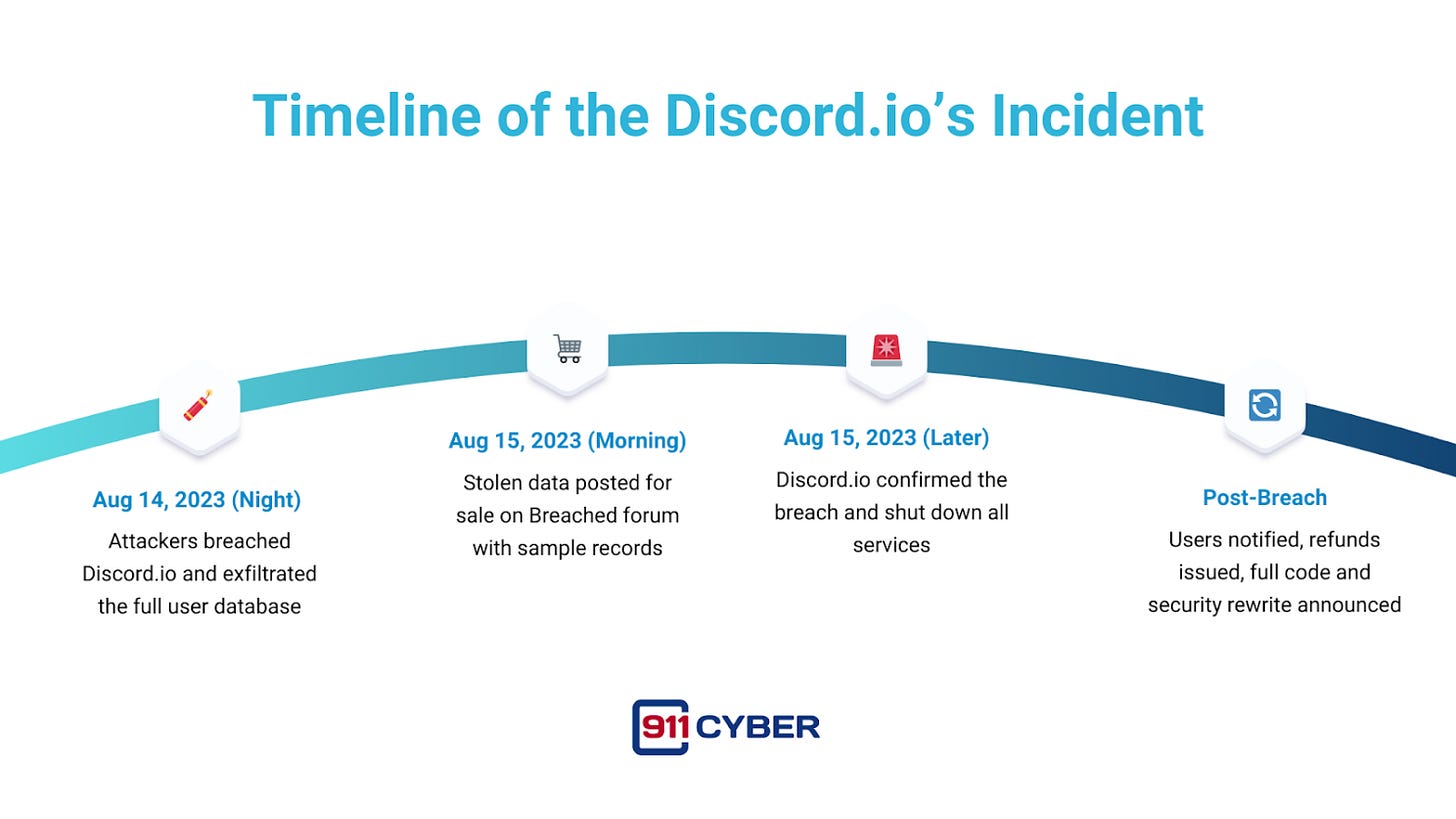
🕳️ How the Breach Unfolded
In mid-August 2023, Discord.io experienced a rapid and decisive security incident that unfolded over less than 24 hours. Attackers exploited a suspected code vulnerability to access and exfiltrate the platform’s database, with the breach becoming public the following morning when stolen records were offered for sale on a cybercrime forum.
Within hours, Discord.io verified the authenticity of the data, shut down all services, and announced an indefinite suspension of operations, triggering user notifications, refunds, and plans for a full code and security overhaul.
🎭 Threat Actor Behavior
The attacker publicly identified as “Akhirah,” acting alone rather than as part of a known ransomware or extortion group.
Instead of issuing a standard ransom demand, the hacker listed the database for sale while framing the breach as partially ideological. Akhirah claimed hostility toward Discord’s broader community and accused Discord.io of enabling illicit server content. In interviews, the hacker stated they preferred Discord.io address these issues rather than simply pay for silence.
At the time of disclosure, the attacker claimed the database had not yet been sold and invited Discord.io’s owner to negotiate. No evidence has emerged tying the breach to a larger organized cybercrime group.
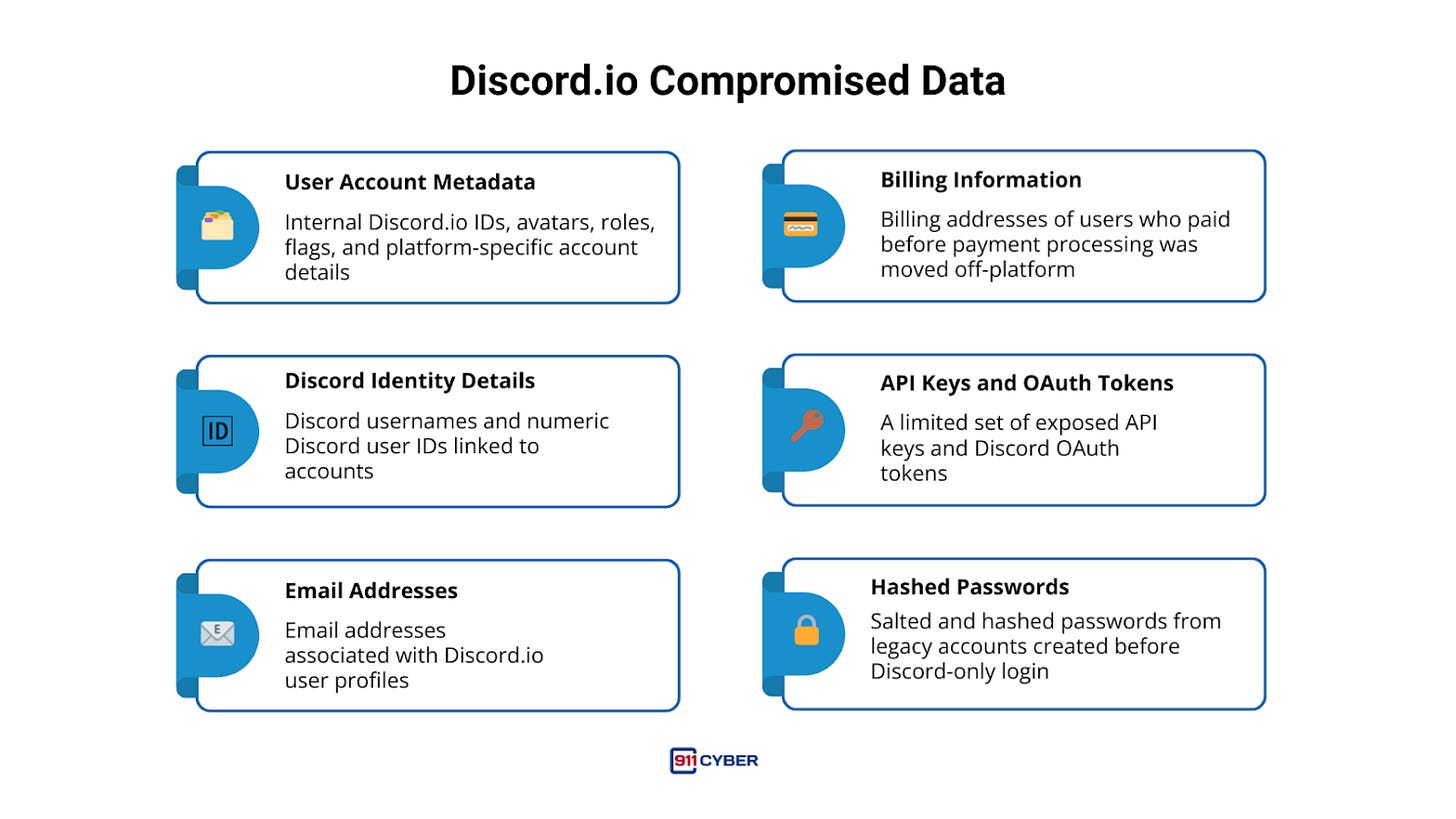
🗂️ What Data Was Exposed
The stolen Discord.io database was extensive and detailed, combining public identifiers with sensitive account metadata.
🚨 Impact on Users
For affected users, the immediate danger was not direct financial theft but secondary abuse.
Security researchers warned that exposed email addresses would likely be reused in phishing campaigns, password-reset scams, and Discord impersonation attempts. Linking Discord usernames and IDs to real email accounts made targeted social engineering significantly easier.
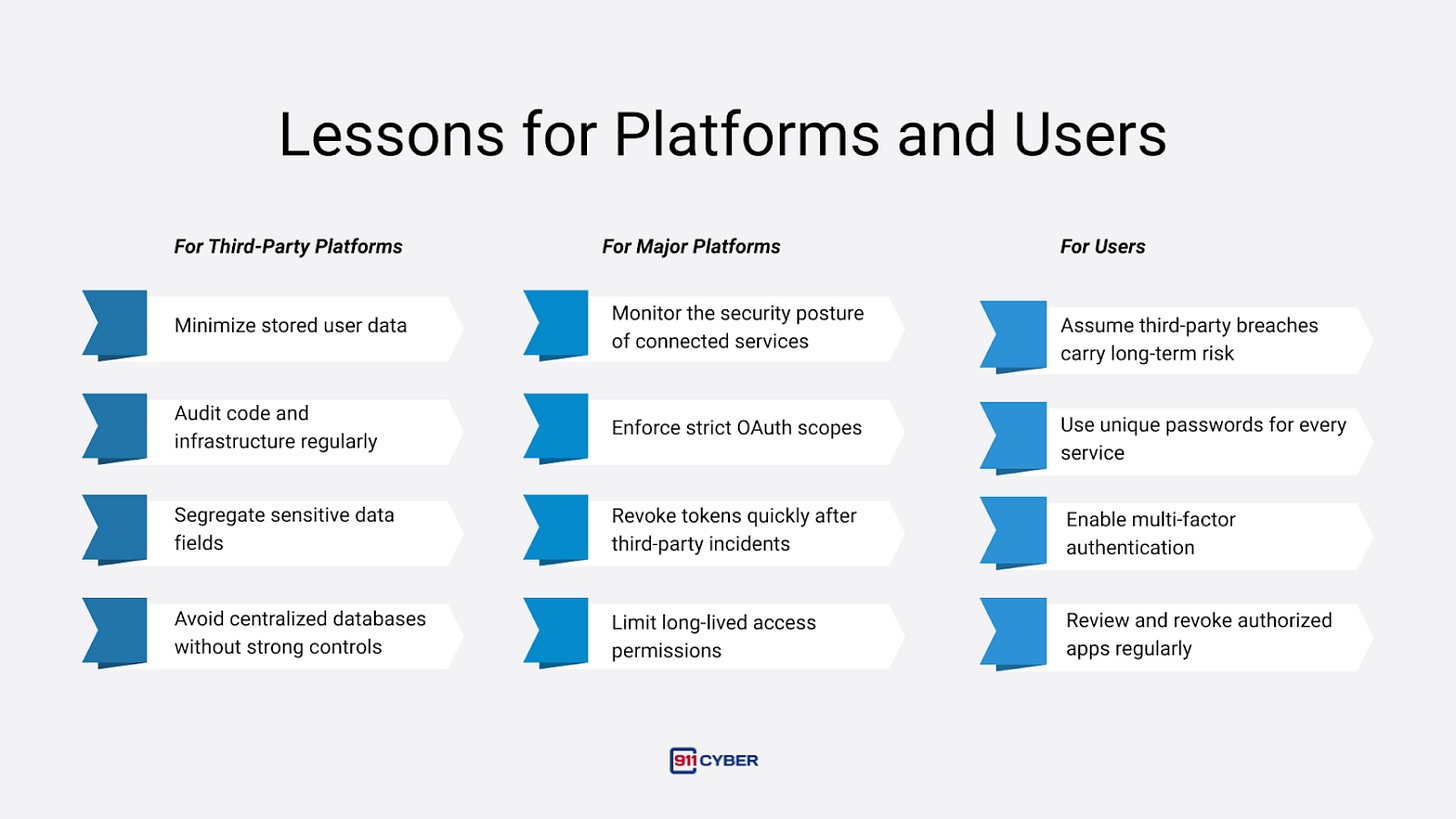
Discord took defensive action by revoking all OAuth tokens associated with Discord.io, cutting off any remaining access between the breached service and Discord accounts. Users were urged to reset passwords and enable multi-factor authentication.
As of early 2026, no widespread Discord account takeovers have been publicly confirmed, but the long-term exposure risk remains.
🛡️ Broader Impact on Discord
Discord itself avoided technical compromise, but the incident created confusion and reputational noise. Many users initially believed Discord had been hacked, forcing the company to publicly clarify the separation.
The breach highlighted a structural risk in large platform ecosystems. Third-party tools, bots, and invite services often hold sensitive permissions while operating outside the platform’s direct security controls. Even when the core platform remains secure, an adjacent failure can undermine user trust.
Following the incident, many Discord communities became more cautious about third-party integrations and OAuth authorizations.
🏢 Company Response
Discord.io’s response was swift and severe.
The service shut down entirely, acknowledged a security failure tied to vulnerable code, refunded recent subscribers, and promised a complete rewrite of its platform and security practices. Administrators also invited the attacker to make contact, stating that no prior negotiation had taken place.
Discord, for its part, revoked tokens, issued user guidance, and reiterated that it does not share data with third-party services like Discord.io.
⚖️ Legal and Regulatory Fallout
As of early 2026, no public lawsuits or regulatory penalties have been reported specifically in connection with the Discord.io breach. There have been no confirmed class-action filings or enforcement actions tied to this incident.
While privacy obligations such as GDPR notification may have applied, no announced fines or investigations have surfaced. The legal impact seems to have been muted compared to the scale of the exposure.
🔄 Updates Through 2026
The stolen Discord.io data has not appeared in major public breach dumps since the initial sale listing. However, security analysts continue to assume the database circulates privately within underground markets.
Discord.io remains offline or in a prolonged redevelopment state. The incident has faded from headlines, but the exposed data likely remains usable for phishing and identity abuse years later.
📘 Lessons for Platforms and Users
✅ Final Takeaway
The Discord.io breach is a textbook example of ecosystem risk. A third-party service fell, but hundreds of thousands of users and a global platform felt the consequences.
No credit cards were stolen. No core systems were breached. Yet the exposure of identity data, emails, and access tokens created lasting danger.
The lesson is simple and uncomfortable. Security is only as strong as the weakest service you trust, and once data leaves the vault, it never truly disappears.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2025 911Cyber . All Rights Reserved.
Follow 911Cyber on: