Weee! is a U.S.-based online grocery platform known for delivering Asian and Hispanic foods to customers across 48 states. By 2022, the company was valued at more than $4 billion and had built a loyal customer base that trusted it not only with payment details, but with precise information about where they lived and how deliveries should reach them.
In early 2023, that trust was compromised.
Hackers stole approximately one year’s worth of Weee! customer order data, impacting an estimated 1.1 million customer accounts and 11.3 million individual orders. While no payment information was taken, the exposed data included names, addresses, email addresses, phone numbers, and highly sensitive delivery instructions such as apartment gate codes and drop-off notes.
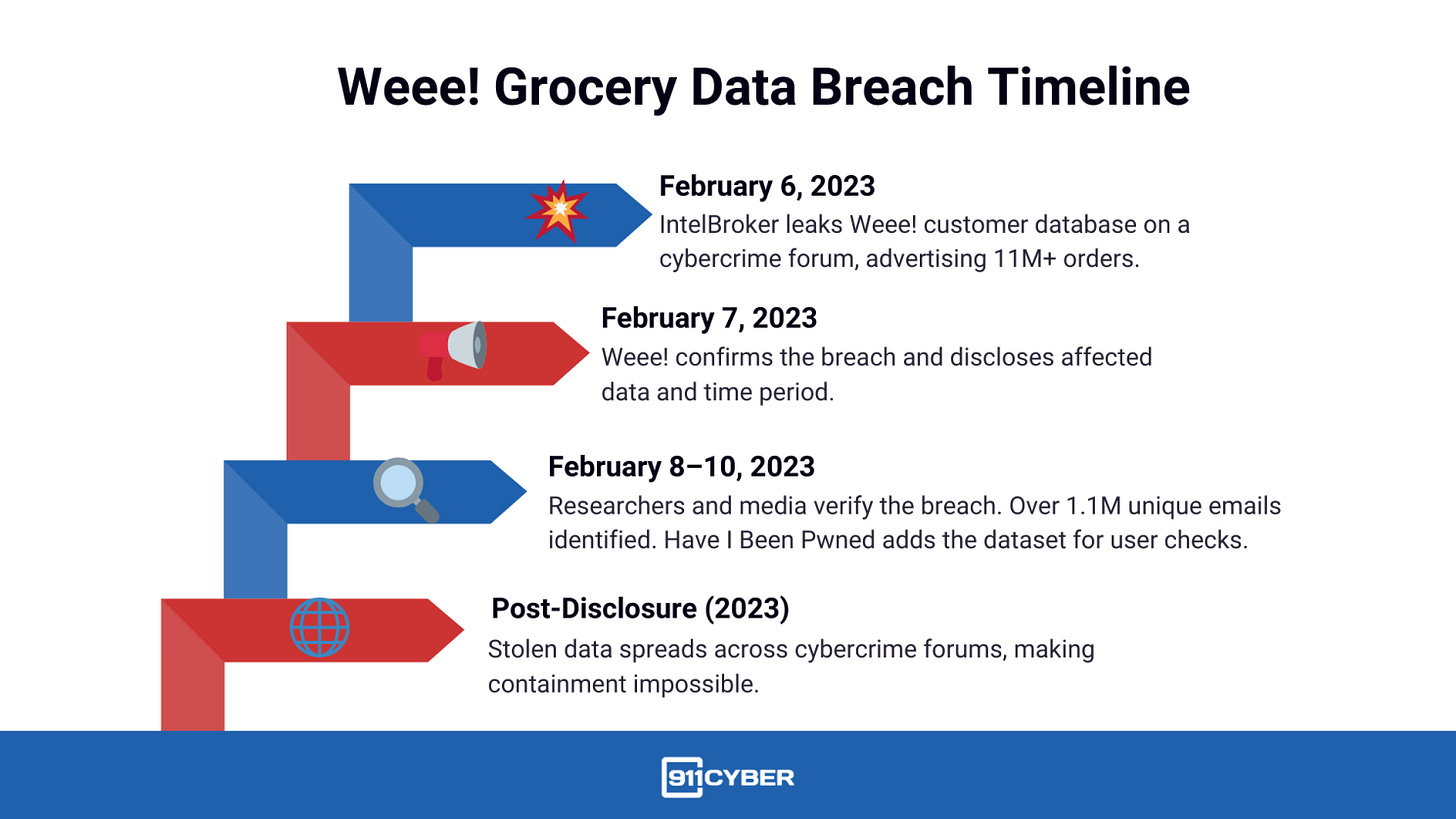
The breach came to light in February 2023, not because Weee! detected an intrusion, but because a hacker publicly leaked the data on a cybercrime forum.
First time seeing this?
🔑 What happened
The breach surfaced when a threat actor posted Weee!’s customer database on an underground hacking forum. The leaked dataset covered orders placed between July 12, 2021 and July 12, 2022, giving attackers access to a full year of customer activity.
Weee! confirmed that the compromised data did not include credit card numbers or banking details, as payments were handled by third-party processors. However, the exposed information still painted an intimate picture of customers’ identities, locations, and daily routines.
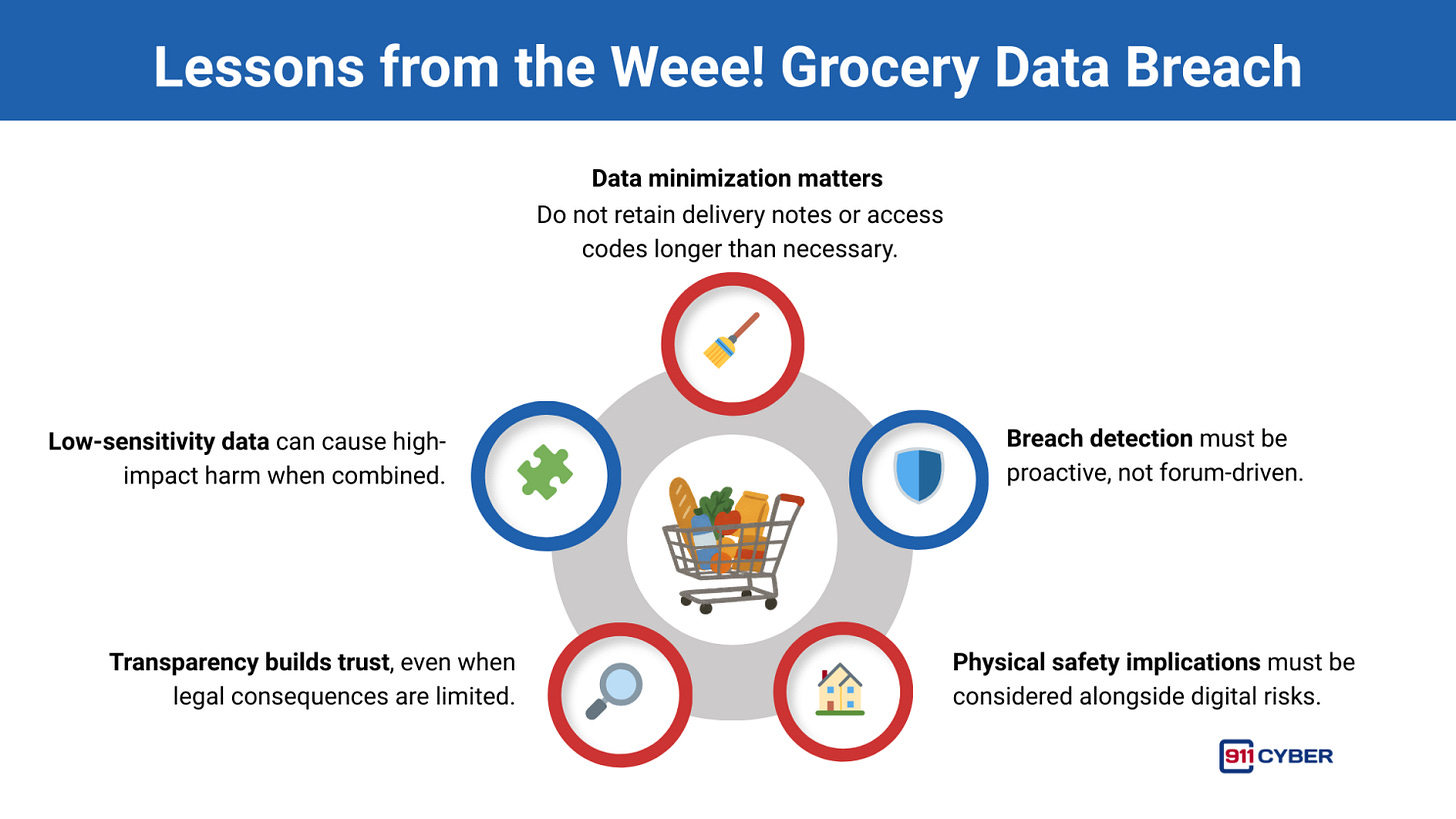
This incident demonstrated that even without financial data, operational records can pose serious privacy and safety risks.
🕳️ How the Breach Unfolded
This was not a sudden, internally detected security incident. Instead, it followed a familiar and troubling pattern in modern cybercrime.
What remains unknown is the precise technical entry point. Weee! never publicly disclosed how attackers accessed its systems. Analysts have speculated about phishing, stolen credentials, or an application vulnerability, but no confirmation was provided. What is clear is that Weee! learned of the breach only after the data was made public.
🕵️ Threat Actor Behavior
The Weee! breach was carried out by a hacker operating under the alias “IntelBroker,” a prolific data thief active throughout 2022 and 2023.
IntelBroker used cybercrime forums to sell or trade stolen data, often boasting about the scale of breaches and the value of the datasets. In the Weee! case, the hacker advertised:
Over 11.3 million order records
More than 1.1 million unique customer email addresses
Detailed delivery instructions, including access codes
Weee! was just one victim among dozens. IntelBroker claimed responsibility for attacks against major technology firms, automotive companies, cybersecurity vendors, and even law-enforcement databases. While some claims were exaggerated, investigators later confirmed that many were legitimate.
In early 2025, law enforcement identified and arrested a 25-year-old British national in France, alleged to be the individual behind the IntelBroker persona. Authorities linked him to over 40 corporate breaches, more than $2 million in illicit profits, and approximately $25 million in victim damages. By mid-2025, his arrest and the takedown of the forum he helped administer effectively ended the campaign.
🗂️ What Data Was Exposed
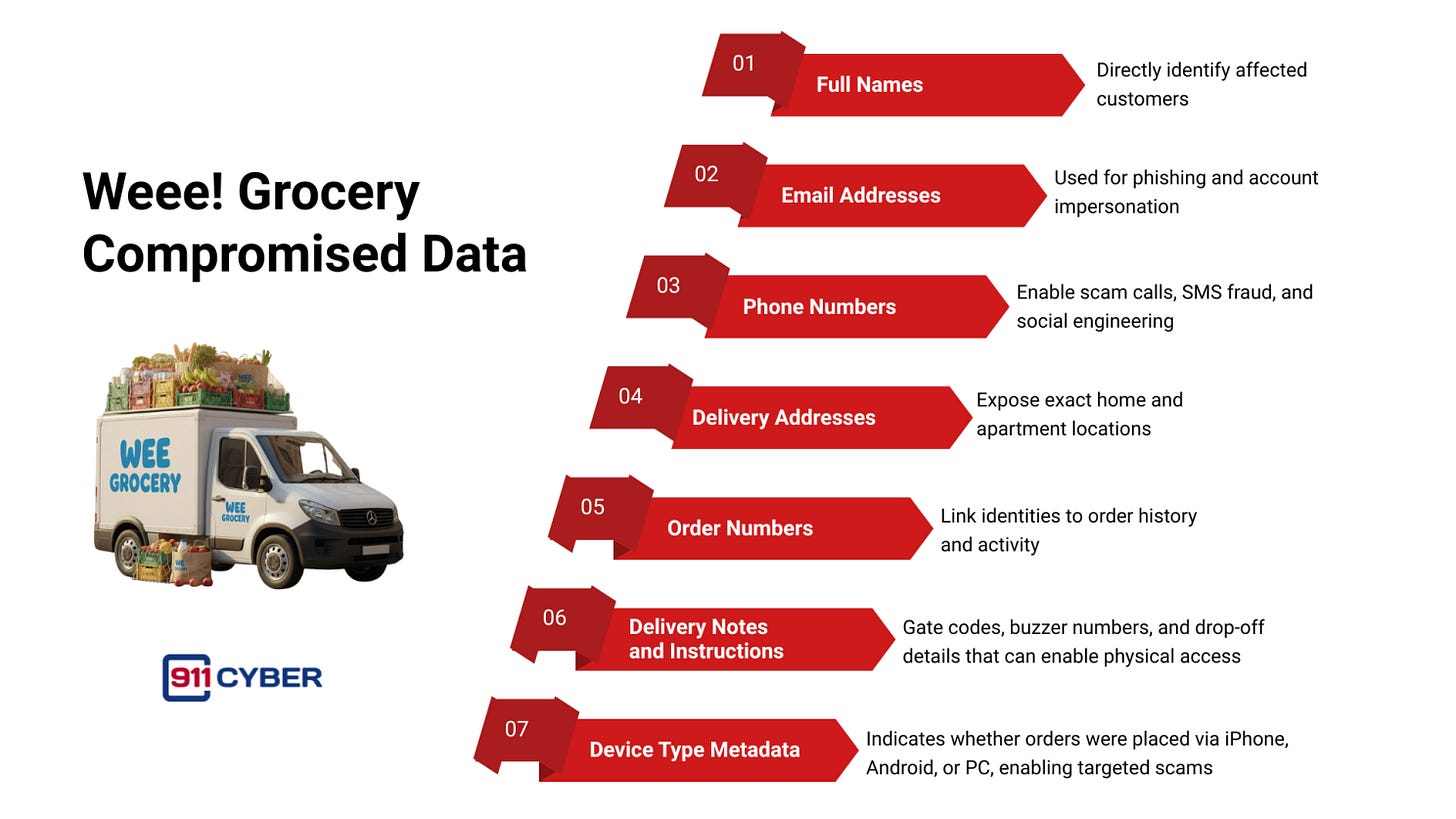
The leaked Weee! dataset was broad in scope and uniquely dangerous because it bridged digital and physical privacy.
The breach covered a one-year order window, resulting in multiple records per customer for frequent users. While grocery item lists were not included, order frequency and location data still revealed behavioral patterns.
By not storing payment data internally, Weee! limited the financial impact of the breach. However, the exposure of access instructions introduced risks far beyond digital fraud.
🚨 Impact on Users
The breach affected approximately 1.1 million customers, with consequences ranging from nuisance to potential physical harm.
Privacy and Fraud Risks
Stolen contact information enabled targeted phishing, scam calls, and SMS fraud. Some users reported an increase in spam messages shortly after the breach, including scams tailored to specific communities Weee! serves.
Physical Safety Concerns
The exposure of gate codes and delivery notes raised alarms among security experts. In possession of a name, address, and access instructions, a malicious actor could theoretically gain physical entry to residential buildings. While no confirmed break-ins were publicly linked to the breach, many users changed access codes and adjusted delivery habits out of caution.
Psychological and Community Impact
Weee! serves immigrant and niche food communities that rely on trust and repeat deliveries. Learning that personal routines and home access details were leaked caused anxiety and eroded confidence, even among users who did not experience direct financial loss.
🛡️ Weee!’s Response
Weee! moved quickly once the breach became public.
Public disclosure was issued within a day of discovering the leak.
Customer notifications were sent to affected users, outlining what data was exposed.
The company emphasized that no payment information was compromised.
A security review and system hardening effort was launched.
Law enforcement was notified, and Weee! cooperated with investigators.
Weee! did not offer credit monitoring services, likely due to the absence of financial data, but partnered with Have I Been Pwned to improve user awareness.
⚖️ Legal and Regulatory Fallout
Several customers filed a class-action lawsuit in 2023, alleging negligence and harm from the exposure of their personal data.
In February 2024, a U.S. federal judge dismissed the case for lack of standing. The court ruled that:
The exposed data was “less sensitive” than financial or identity credentials.
Spam messages and anxiety did not constitute sufficient legal injury.
Claimed financial losses could not be definitively linked to the breach.
No U.S. regulatory fines or enforcement actions were announced against Weee!. The case highlighted a persistent legal gap, large-scale exposure of personal data without immediate financial loss often results in limited accountability.
🔄 Updates as of 2026
The stolen Weee! data continues to circulate in aggregated breach databases.
No additional Weee! breaches have been publicly reported since 2023.
The arrest of the IntelBroker hacker in 2025 marked a rare but meaningful law-enforcement success.
Weee! remains operational and has expanded its offerings, though the breach remains a cautionary reference in cybersecurity discussions.
🧠 Lessons for Every Consumer Platform
The Weee! breach reinforces several critical lessons:
✅ Final Takeaway
The Weee! breach shows that even non-financial data can cause serious harm. Names, addresses, phone numbers, and delivery instructions were enough to create long-term privacy and physical safety risks for more than a million users.
The incident also highlights a dangerous gap where companies may face limited legal consequences when breaches do not involve payment data, even though the impact on users is real and lasting.
The core lesson is simple and urgent. All personal data must be treated as high-risk data. Once it is exposed, it cannot be taken back, and the consequences fall on users long after the breach fades from public view.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: