Gravy Analytics, a major U.S.-based location data broker, found itself at the center of a privacy storm in January 2025 after hackers infiltrated its systems and stole terabytes of highly sensitive location data. As a company that tracks over a billion devices daily, the breach revealed just how deeply personal geolocation data can be and how dangerous it becomes in the wrong hands.
First time seeing this?
The Incident
January 4, 2025: Gravy Analytics’ parent company Unacast discovered it had been breached after a hacker directly contacted the company and posted proof of a data heist on a Russian cybercrime forum.
January 5, 2025: A sample of the stolen data (1.4 GB) was posted publicly, along with a 24-hour extortion ultimatum threatening to release 17 TB of data unless demands were met.
Following Days: The company’s website went offline, and internal systems were locked down for containment.
The Hack
A stolen Amazon Web Services (AWS) access key was used to gain unauthorized access to Gravy’s S3 buckets, where location datasets were stored. The key likely belonged to a service or internal user account and allowed the attacker to move laterally and exfiltrate massive volumes of data without detection.
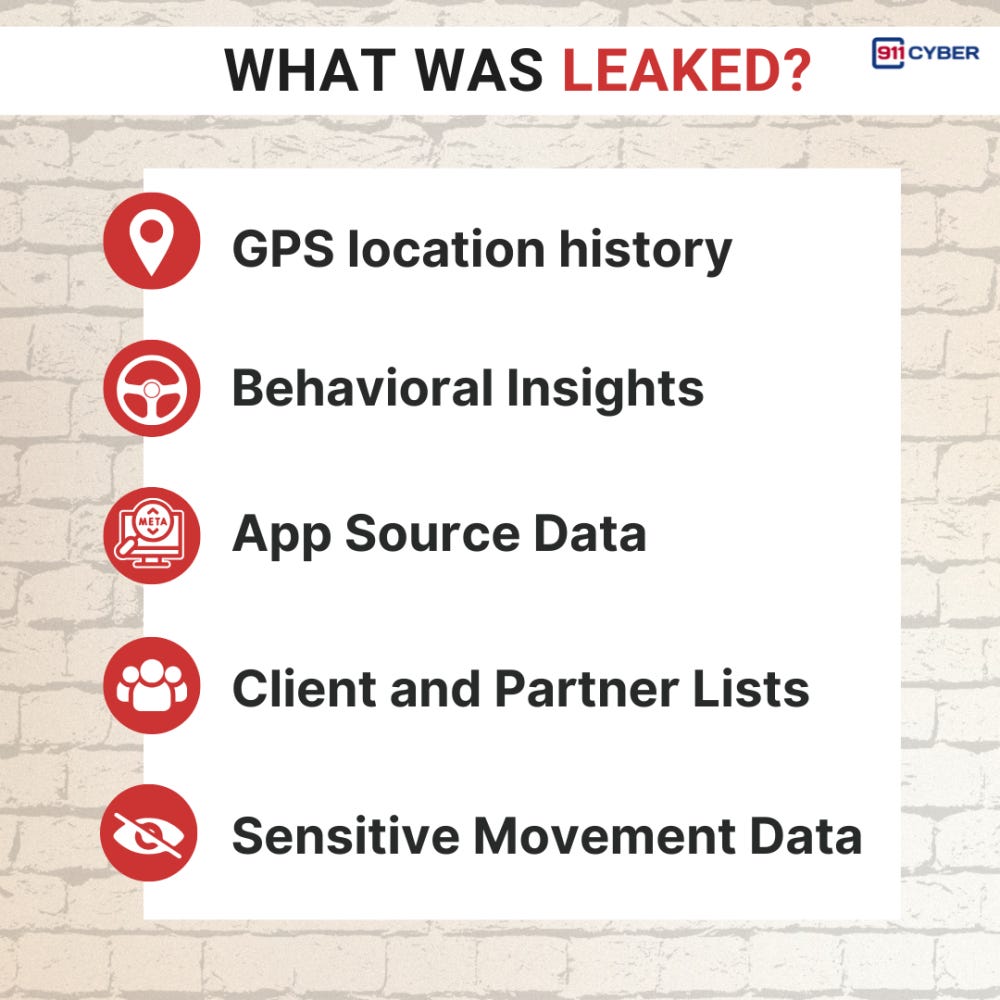
What Was Exposed:
Historical GPS Location Logs: Precise movement data from millions of devices.
Client and Partner Lists: Internal records of app partners and corporate clients.
Behavioral Tags and Analytics: Inferences like “LIKELY_DRIVING” tied to users’ movement habits.
App Source Traces: Data pulled from dating apps, fitness trackers, religious apps, pregnancy trackers, and more.
The Impact
Privacy Exposure: Sensitive movement history of millions of users globally (U.S., Europe, Russia, and beyond) was compromised however, the number for each region is still under investigation. The breach exposed how broadly apps were feeding data to Gravy, often without user awareness or consent.
Litigation: At least four lawsuits (as of February 2025) were filed in New Jersey, Virginia, and California, alleging negligence in data protection and seeking damages and regulatory reform.
Regulatory Fallout: Already under FTC scrutiny for selling sensitive data, Gravy/Venntel was hit with a ban on selling certain location information just weeks before the breach. Post-breach, investigations by the UK ICO and Norway’s DPA are ongoing.
The Response
Immediate Action:
Disabled compromised AWS credentials
Took down affected systems
Began forensic investigation with third-party experts
Regulatory Notification:
Filed GDPR notices within 72 hours
Notified European and U.S. regulators
Reached out to affected corporate clients and app partners
Security Overhaul:
Hardened cloud infrastructure
Enhanced credential management and monitoring
Working with law enforcement and cybersecurity firms for threat containment
Industry-Wide Wake-Up Call
The Gravy breach has reignited scrutiny of the location data brokerage industry. It exposed how easily pseudonymous data can be weaponized to infer identities, daily routines, and sensitive traits. The implications are vast for individuals, businesses, and national security.
Lessons Learned and Best Practices
Guard Cloud Credentials Like Gold: A single misused AWS key gave attackers access to 17 TB of data. Credential hygiene must be paramount.
Audit Third-Party Data Pipelines: Many app developers were unaware that their users’ data flowed to brokers like Gravy. Transparency is overdue.
Encrypt Everything, Always: Even pseudonymous data must be encrypted at rest and in transit to prevent misuse.
Regulatory Compliance Is Not Optional: GDPR, CCPA, and FTC mandates require proactive controls, not just reactive cleanups.
Demand Accountability in the Data Supply Chain: Companies must ensure partners uphold privacy standards to avoid secondhand exposure.
The Gravy Analytics breach revealed more than data, it laid bare the opaque ecosystem of digital tracking. This isn’t just a cybersecurity event, it’s a crisis of consent. For industries built on data, trust is the first thing at risk when breaches occur. And once lost, it’s hard to regain.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: