Welcome to Cyber Hygiene, my weekly newsletter, where I share tips and actionable data to help everyone stay safe online.
🔍 What is Swatting?
Swatting is a serious crime where someone makes a false emergency call to send armed police to another person’s location. The caller often claims a violent situation, like a hostage crisis or active shooter, to trigger a high-risk response.
It began in online gaming circles but has spread far beyond. Today, swatting targets influencers, executives, journalists, schools, and ordinary people. The results can be traumatic, and in some cases, deadly.
What makes swatting so dangerous is how easy it is to pull off. With just a name or address found online, someone can turn digital information into a real-world threat.
⚠️ How Dangerous is Swatting?
Swatting is extremely dangerous because it creates real-life emergencies based on fake threats. These calls often claim there is a shooting, hostage situation, or bomb, leading to a heavily armed police response.
Innocent people have been hurt and even killed. In one well-known case, a man in Kansas was shot by police after a false report was made about his home.
Even without physical harm, the emotional toll can be serious. Victims often experience anxiety, fear, and lasting trauma, especially when children or elderly family members are involved.
Swatting also wastes public resources. A single incident can cost police departments thousands of dollars and takes attention away from real emergencies.
This threat is growing and now includes schools, workplaces, and public figures. The risks are high, and the impact is real.
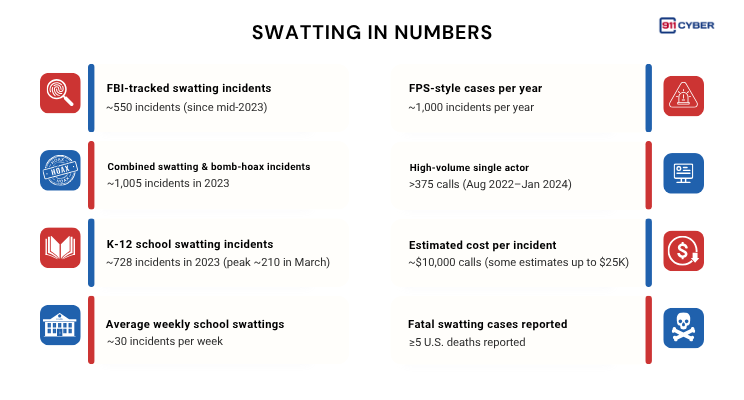
📊 Swatting in Numbers
🧠 Why It Happens
Swatting started in online gaming as a way to troll or embarrass opponents during live streams. Over time, it evolved into a dangerous form of revenge and intimidation.
Many attackers act out of anger, personal grudges, or political motives. They often feel protected by anonymity tools like VPNs and burner phones, making them bolder.
Swatting is also sometimes sold as a paid service, lowering the barrier for abuse. What may seem like a prank is actually a serious form of harassment meant to frighten and disrupt lives.
👁️ Who Is at Risk and Why?
🕵️ How Attackers Find Your Information
Public data broker websites like Spokeo, Whitepages, and FastPeopleSearch
Data leaks and breaches exposing personal details
WHOIS records from domain registrations linked to your name or business
IP addresses revealed during online gaming or video calls
Social media oversharing—photos, location tags, or personal posts revealing your address
Reverse lookup tools and people search engines
Stalking and doxxing forums where attackers share information
Phishing or social engineering attacks that trick you into revealing details
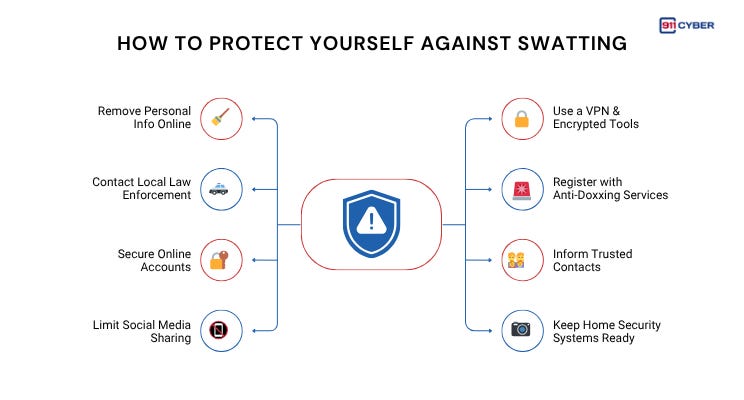
🛡️ How to Protect Yourself Against Swatting
🧰 What Resources Are Available to Help?
📚Books
Delete: The Virtue of Forgetting in the Digital Age by Viktor Mayer-Schönberger
Doxing (Cyber Threats) by Connor Stratton
🎙️ Podcasts
ShortHand: Swatting by Hanah Maguire and Suruthi Bala on RedHanded
“Swatting” Threats Disrupt Schools Across The US by K. Oanh Ha, David Gura, and Wes Kosova on Big Take
When Gamers Start Swatting: Violence for Hire Online by David Mauro on Cyber Crime Junkies
▶️ Videos
What is swatting? by TECHtalk, Computerworld
How To Protect Yourself Against Swatting and Doxing by Bruted
🛠️ Tools
DeleteMe : Opt-out from data brokers
Blur / Abine : Mask your email, phone, and address
MySudo by Anonyome Labs, Inc. : Create private identities for digital life
Have I Been Pwned : Check if your info has been leaked
🧠 Final Thoughts
Swatting is a chilling reminder that cyber threats don’t just stay online. They can invade your home, put lives at risk, and turn digital harassment into real-world trauma.
As AI tools become more powerful, they also make it easier for bad actors to find personal information, mimic identities, and automate the search for targets. This means the line between the digital and physical world is thinner than ever.
Modern CyberHygiene now goes beyond good passwords and antivirus software. It means thinking critically about what you share, staying alert to how your data might be used, and preparing for threats that evolve alongside technology.
Digital safety is personal safety, and it requires both awareness and action.