In February 2023, a major Irish university became the latest victim in a global wave of ransomware attacks. Munster Technological University (MTU), serving over 18,000 students across six campuses, was forced to close four campuses in Cork for an entire week after its IT systems were locked down by the Russian-linked BlackCat ransomware group. The attackers not only encrypted MTU’s systems but also leaked 6GB of internal data on the dark web when the university refused to pay a ransom.
In this edition of Cybercrime Stories, we break down the MTU breach, how it happened, what was stolen, and what the fallout means for higher education.
First time seeing this?
What is Munster Technological University?
MTU is a public technological university in Ireland, formed in January 2021 through the merger of Cork Institute of Technology and IT Tralee. With campuses in Cork and Kerry, it offers programs across business, science, engineering, and the arts. Its facilities include the MTU Cork School of Music and the National Maritime College of Ireland.
The Breach
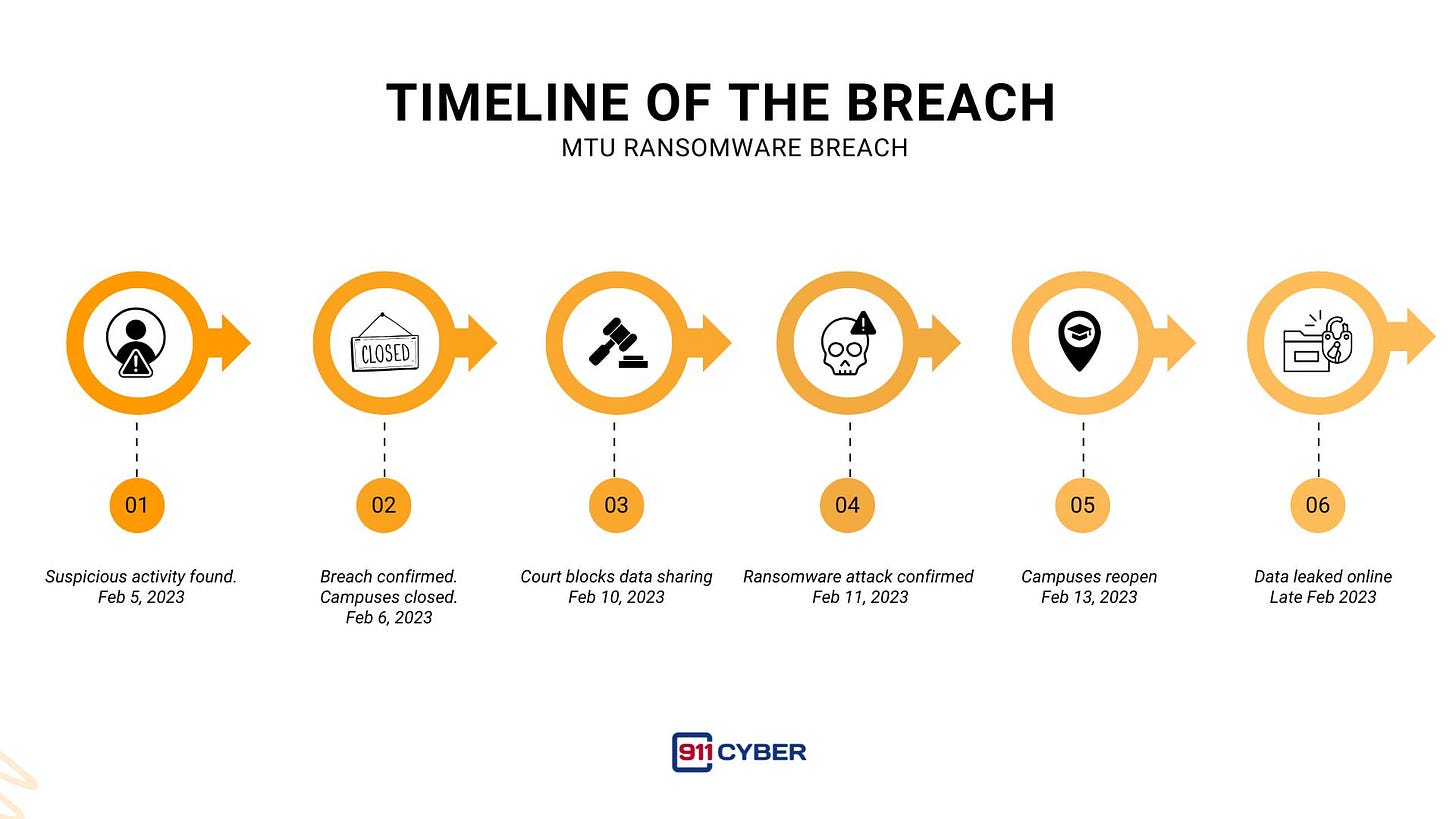
On February 5, 2023, MTU detected unusual IT activity. By the next day, the university declared a “significant IT breach,” shut down Cork campuses, and suspended classes. The Kerry campuses stayed open, running on separate systems.
The attackers were identified as the BlackCat/ALPHV ransomware group and they demanded a substantial but undisclosed ransom. MTU refused to pay. The gang responded by publishing over 6GB of stolen data on their dark web leak site.
How the Hack Happened
MTU has not confirmed the exact entry point. At the time, a critical VMware ESXi vulnerability was being widely exploited, making it a likely suspect. Other possibilities include:
Phishing emails that tricked a user into downloading malware
Compromised remote access via stolen or weak credentials
Once inside, BlackCat exfiltrated sensitive files before encrypting systems. This is a double extortion strategy designed to pressure victims into paying.
What Was Leaked?
The stolen data included:
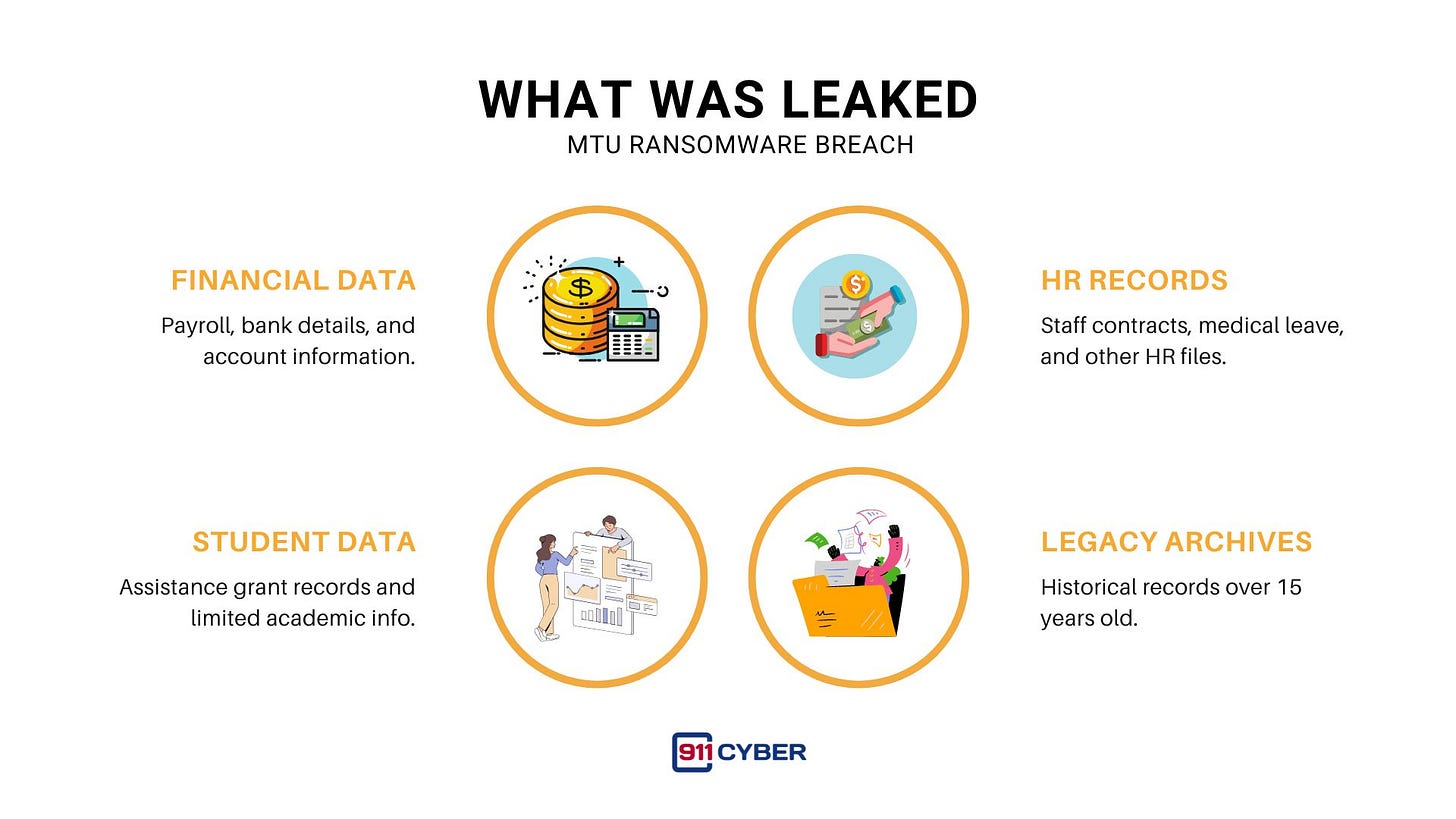
Employee payroll and bank details
Staff contracts, HR records, and medical leave files
Financial account information and internal audits
Some student-related data, such as assistance grant records
Notably, much of the data dated back 15+ years, exposing legacy archives from pre-merger institutions. While there was no immediate evidence of direct financial theft, the data could fuel phishing, fraud, or targeted scams.
The Fallout
Operational Disruption
Four Cork campuses closed for a week
All classes canceled from February 6–13, 2023
Phone and IT services offline during restoration
Data Exposure
Over 6GB of internal data leaked to the dark web
Long-term risk of targeted scams for staff and alumni
Legal Action
MTU secured a High Court injunction forbidding republication of stolen data
Gardaí Cyber Crime Bureau and Ireland’s NCSC launched investigations
The Data Protection Commission was notified under GDPR rules
Financial & Security Overhaul
Direct response costs reached €3.5 million
New measures included a 24/7 SOC-as-a-Service, SIEM deployment, MFA for all accounts, upgraded firewalls, and regular phishing simulations
A Chief Information Security Officer role was created
The Hackers
BlackCat/ALPHV is a Russia-linked ransomware-as-a-service operation known for technical sophistication and Rust-based malware. They are notorious for targeting universities, corporations, and government agencies worldwide, and for their aggressive data-leak strategy when ransom demands are rejected.
Lessons for Cybersecurity Leaders
Backups Save the Day: MTU restored systems from backups without paying ransom.
Legacy Data Is a Risk: Old archives can still be targeted and leaked.
Public Refusal Requires Resilience: Saying “no” to ransom demands must be backed by strong recovery and legal strategies.
Universities Are Prime Targets: Decentralized networks and large datasets make higher education vulnerable.
How Students and Staff Can Protect Themselves
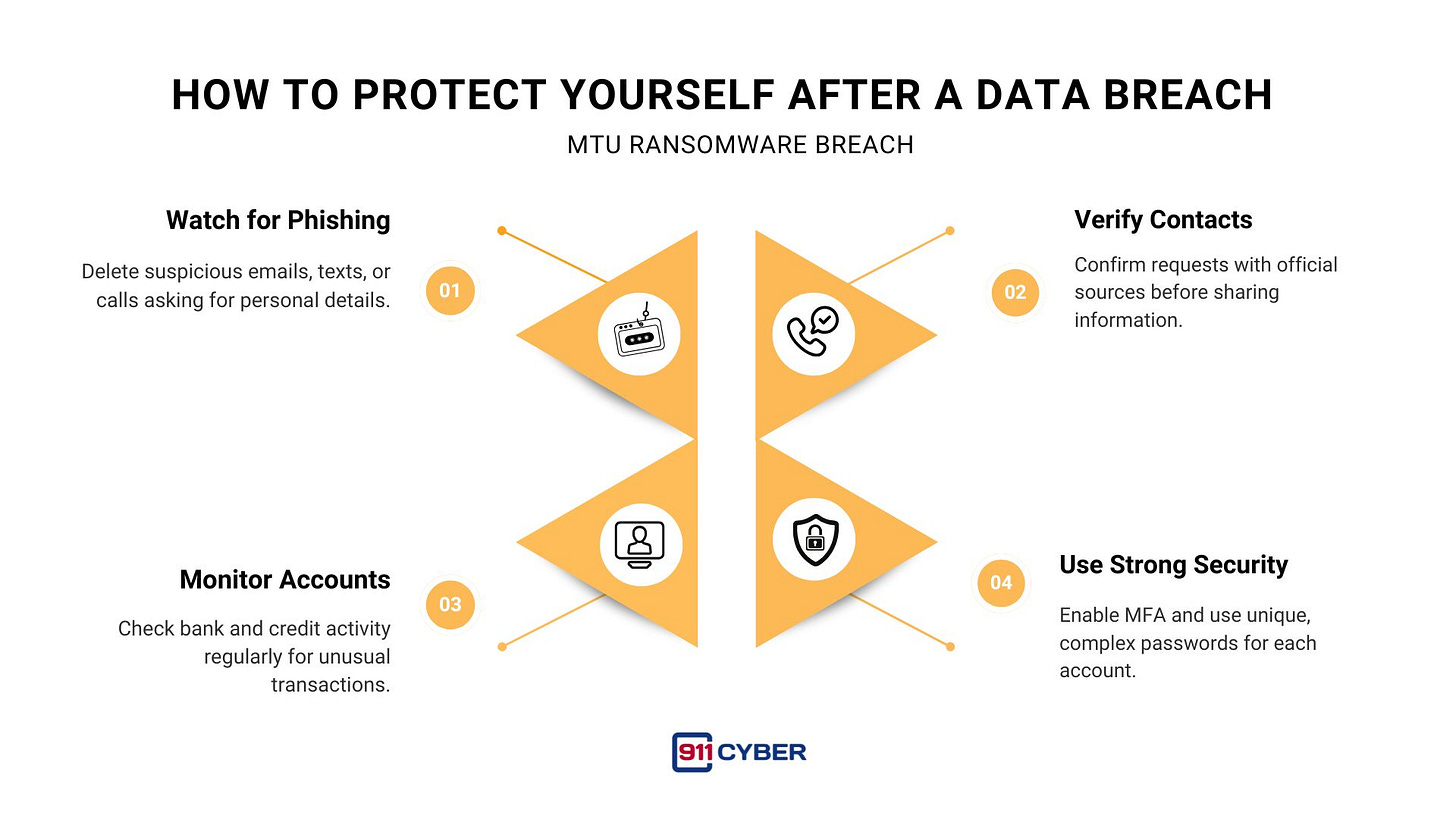
Be alert for phishing emails and scam calls claiming to be from MTU or banks.
Verify suspicious contact via official channels before sharing information.
Monitor bank accounts and credit reports for unusual activity.
Use strong, unique passwords and enable multi-factor authentication.
The Bigger Picture
By 2025, MTU had returned to normal operations, with no confirmed fraud tied to the stolen data. The case remains under investigation, but the attack has become a case study in Ireland’s higher education sector on how to respond to and recover from a severe ransomware breach.
MTU also turned the crisis into an opportunity when in 2024 it launched Cyber Innovate, a €7 million program to foster cybersecurity innovation, turning lessons learned from a devastating attack into fuel for building future digital resilience.
Final Takeaway
The MTU ransomware incident shows that universities must treat cybersecurity as critical infrastructure. Backups, legal readiness, and transparent communication can blunt the worst impacts of a breach. But with ransomware groups evolving constantly, the sector needs to stay one step ahead or risk another week of empty lecture halls.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: