The Optus Data Breach (Australia, 2022)
In late September 2022, Australia woke up to a cybersecurity nightmare. Optus, the country’s second-largest telecommunications provider, announced a breach that exposed the personal information of nearly 10 million people. This represented close to 40 percent of Australia’s population.
It was not just another corporate incident. It was a national shockwave.
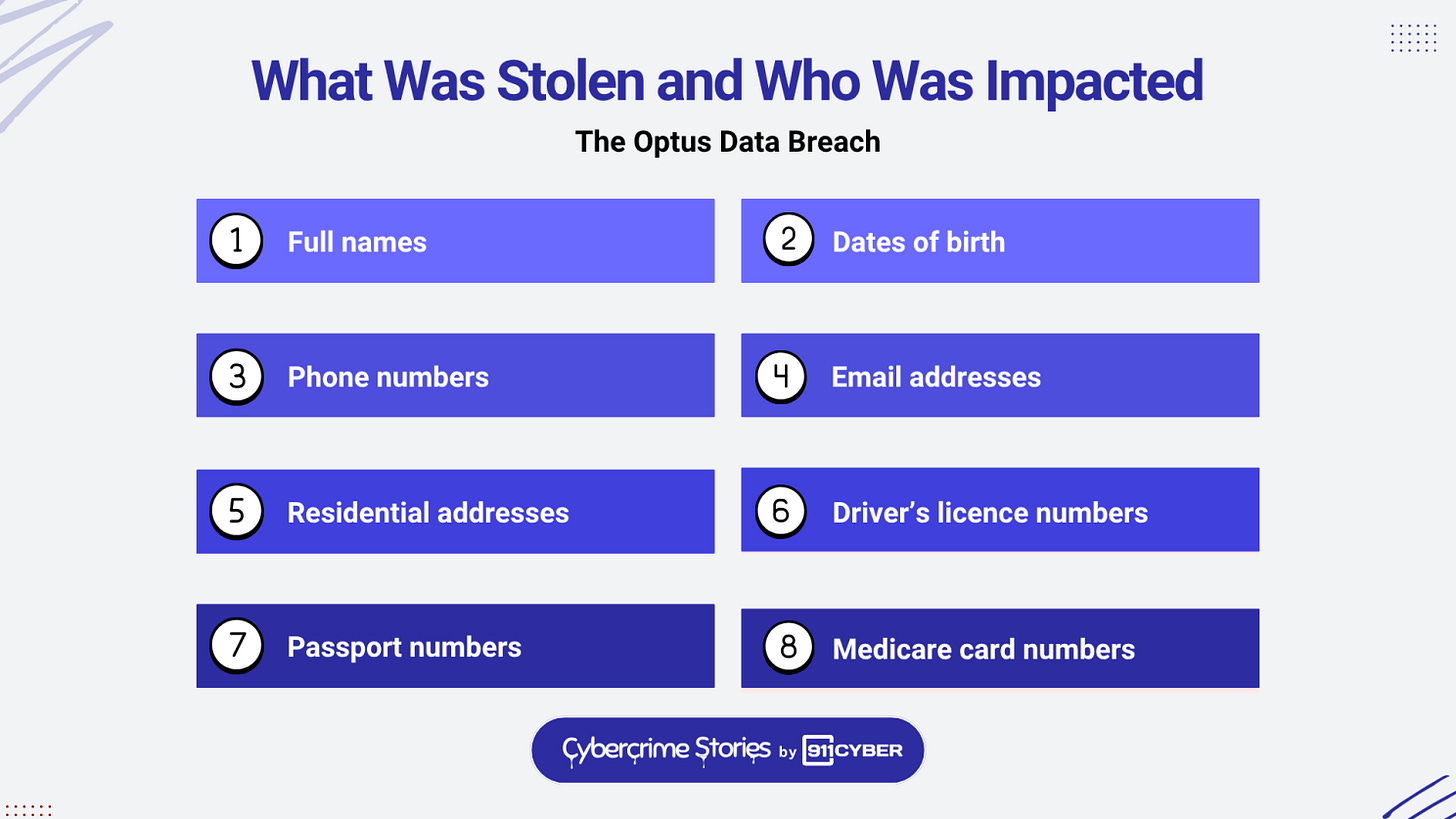
Driver’s licences, passport numbers, Medicare IDs, home addresses, mobile numbers, and other identifying details were suddenly in the hands of a criminal actor. A quiet API misconfiguration turned into one of the most disruptive privacy events in Australian history.
For weeks, the breach dominated headlines, fueled political anger, and ignited a sweeping overhaul of the country’s cybersecurity laws. Most importantly, it shattered the assumption that major companies always have strong security controls in place.
First time seeing this?
⚙️ How the Breach Happened
The initial public narrative described the Optus breach as a sophisticated attack. Investigators later discovered something very different and far more troubling.
An Exposed API Accessible to the Public
A customer data API was accessible on the open internet without authentication. No login, no API key, and no access control blocked external access. Anyone who discovered the URL could pull customer data directly from the system.
Sequential Customer IDs
The API allowed access by customer ID, and these IDs followed a simple numerical sequence. Once the attacker found a valid ID, they could enumerate millions of others by increasing the number.
Lack of Rate Limiting
There were no limits on the number of requests a client could make. As a result, the attacker harvested data rapidly without any automated systems detecting unusual activity.
The Attacker’s Own Statement
On an online forum, the alleged hacker stated that the API required no authentication and was fully open to the public.
What appeared at first to be an advanced intrusion was actually a basic security oversight that allowed mass scraping of sensitive information.
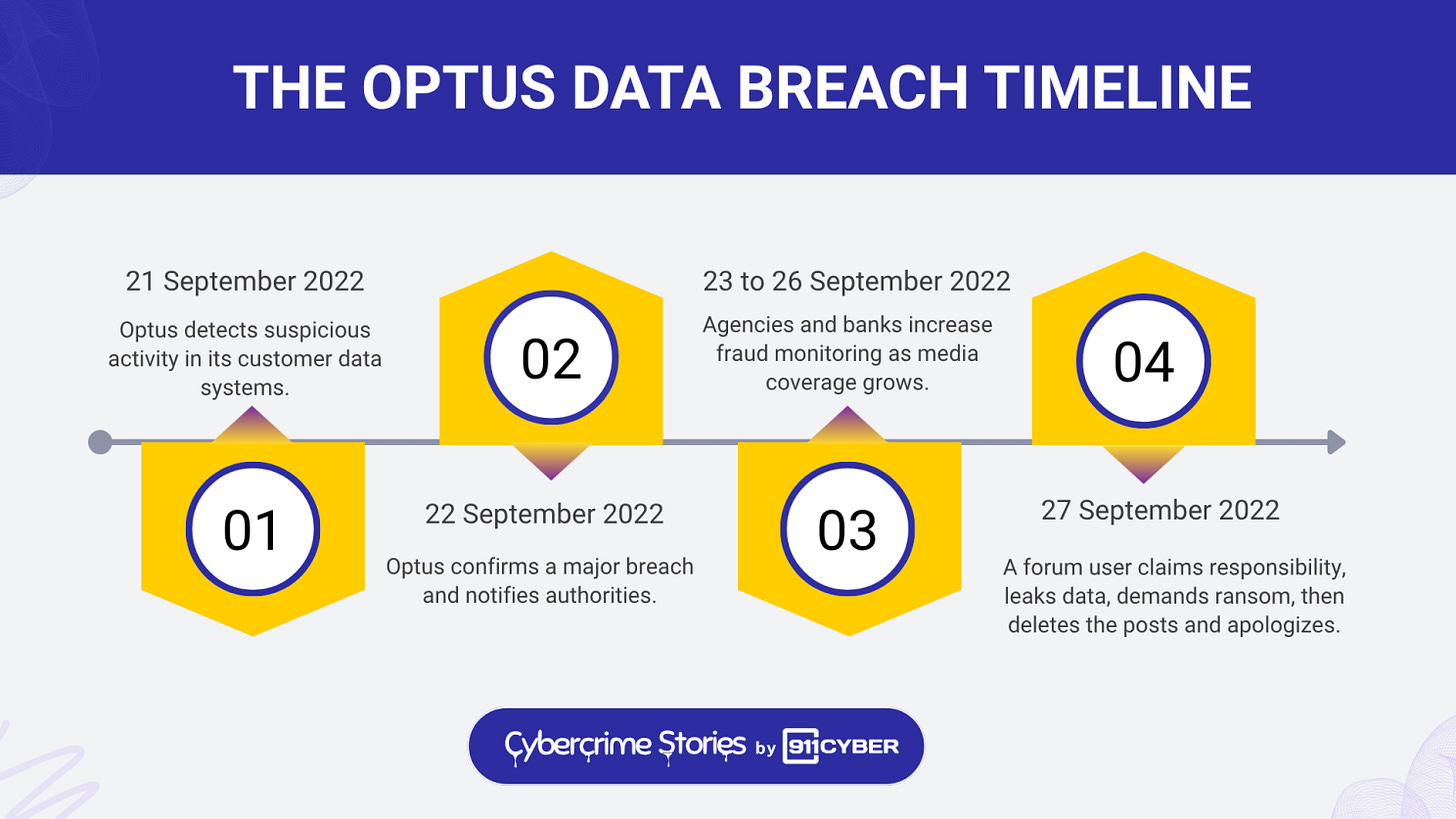
🗓️ Timeline of the Incident
🌍 What Was Stolen and Who Was Impacted
This group included approximately 150,000 passport numbers and roughly 50,000 Medicare card numbers. Hundreds of thousands of current licence numbers were also compromised. Many victims were former customers who did not know their data was still on file due to retention rules.
The scope of the breach meant that nearly 10 million Australians were put at risk of identity theft at the same time.
.
🧠 Unmasking the Attacker
The ransom component of the incident unfolded rapidly.
A BreachForums user posted a ransom note that included a sample of stolen customer data. They demanded 1 million US dollars and threatened to release large batches of records daily if Optus did not pay.
The user posted 10,000 records to prove they were serious. Hours later, the posts were deleted and replaced with an unexpected apology. The attacker stated that they would not sell the data.
Optus publicly confirmed that it had not paid any ransom. Analysts believe the attacker may have feared the speed and intensity of law enforcement attention.
Regardless of the apology, the leak had already occurred and copies were likely saved by others.
🏢 Optus Response
Optus mobilized hundreds of staff members into a crisis response center. The company engaged Deloitte to conduct a forensic investigation. It offered:
Twelve months of free Equifax credit monitoring
Reimbursement for identity document replacement
System-wide security reviews and enhancements
Despite these efforts, customer frustration grew. Many found the company’s communication unclear or delayed. Government officials criticized Optus for slow data sharing that complicated fraud prevention.
Public trust eroded quickly.
🎯 Government Reaction
Cyber Security Minister Clare O’Neil rejected the idea that the breach was sophisticated. She stated publicly that the incident reflected basic cybersecurity failures that should not occur within a major telecommunications provider.
The federal government enacted emergency regulations that allowed Optus to share compromised ID numbers with banks and government agencies. Banks increased monitoring, and state governments waived fees for licence replacement.
The Prime Minister also commented on the seriousness of the breach and emphasized the need for accountability.
The political and media environment turned the breach into a national reckoning on cybersecurity.
⚖️ Legal and Regulatory Fallout
Regulatory Investigations
The Office of the Australian Information Commissioner launched an extensive investigation into Optus’s data protection practices and data retention policies. The Australian Communications and Media Authority began a separate investigation into whether Optus had violated telecommunications security obligations.
Privacy Law Reform
In response to the breach and a similar incident involving Medibank a month later, the government rapidly amended the Privacy Act to increase penalties for serious privacy breaches. The maximum penalty rose to the greater of:
50 million Australian dollars
Three times any benefit obtained from misuse of data
Thirty percent of adjusted turnover
Class Action
Slater and Gordon filed a major class action involving more than 100,000 affected customers. The plaintiffs seek compensation for identity replacement costs, stress, and other damages.
The Deloitte Report Dispute
Optus initially attempted to withhold its Deloitte forensic report under claims of legal privilege. The Federal Court rejected this argument and ordered the report to be produced, strengthening the class action case.
OAIC Court Filing in 2025
The OAIC filed a civil lawsuit alleging a privacy violation for each affected person. If penalties were assessed individually, the total could reach unprecedented levels, although any final amount will likely be negotiated or capped.
🧩 Aftermath and Legacy: 2023 to 2025
The Optus breach set off long-term changes across corporate and government cybersecurity in Australia.
1. National Cybersecurity Reform
The government established the National Office for Cyber Security, drafted the Cyber Security Strategy 2023 to 2030, and began considering a separate Cyber Security Act. Companies that handle large-scale personal data are now expected to meet higher security standards.
2. Leadership Change at Optus
After intense scrutiny and a separate nationwide outage in 2023, Optus CEO Kelly Bayer Rosmarin resigned. The company’s parent firm, Singtel, promised significant investments in security and transparency.
3. Continued Investigations
While the primary attacker was never identified, authorities arrested a teenager in Sydney who attempted to extort breach victims using leaked data. This highlighted the secondary risks that follow a major exposure event.
4. A Cultural Shift in Corporate Australia
The breach accelerated board-level attention on cybersecurity. Companies across the country began adopting stronger data minimisation practices, more frequent audits, and routine incident response exercises.
Optus became a cautionary example referenced in boardrooms and government meetings throughout 2023 and beyond.
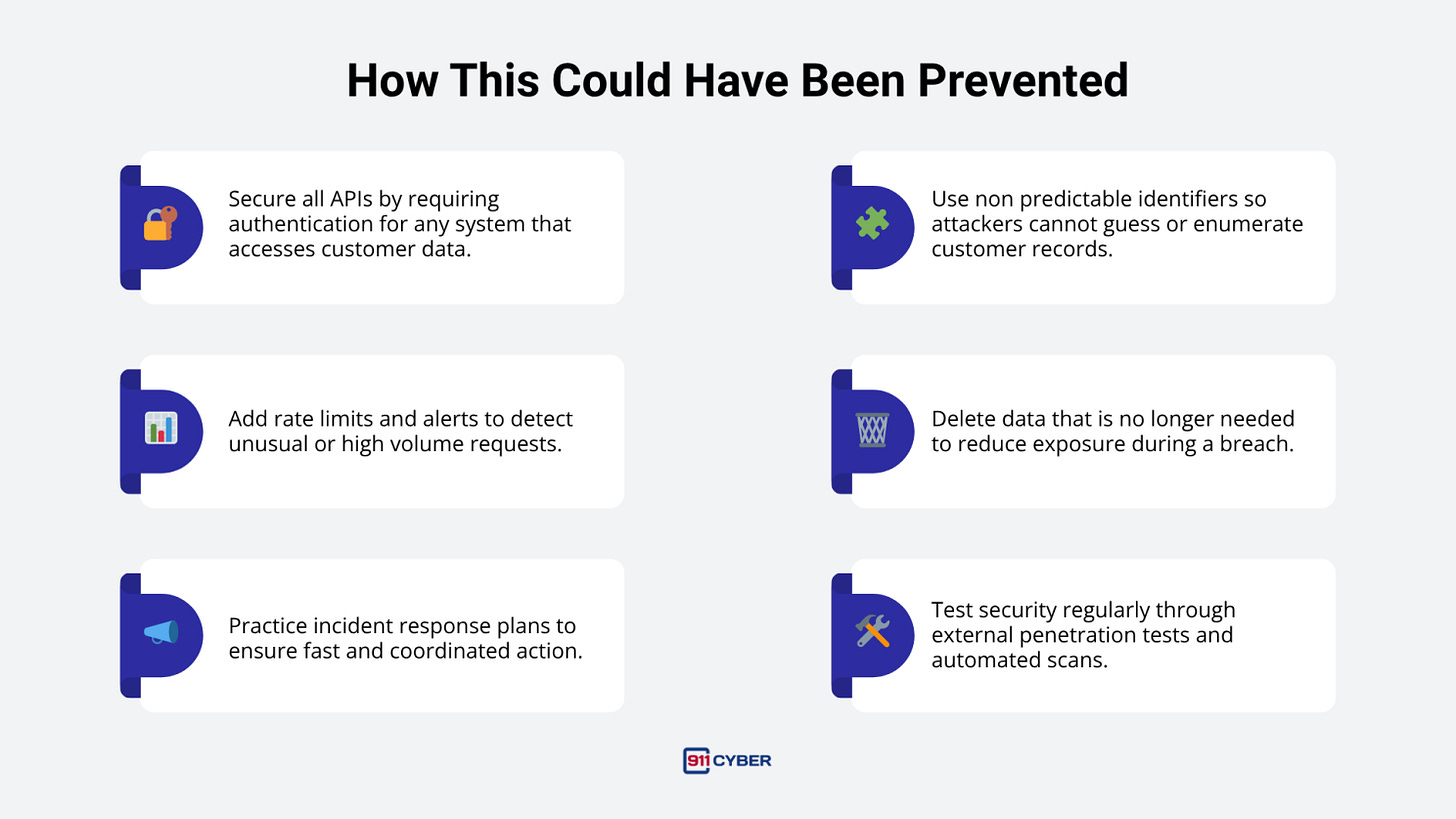
🛡️ How This Could Have Been Prevented
🕊️ Final Takeaway
The Optus breach was not a demonstration of elite cyber skill. It was a reminder that basic security practices are essential. One exposed API and one set of predictable customer IDs resulted in a national crisis.
Millions of Australians faced the stress of identity replacement, fraud monitoring, and loss of trust in a major service provider. The breach pushed lawmakers, regulators, and companies to make cybersecurity a priority. While the event was painful, it also sparked positive change.
Optus highlighted a simple truth, cybersecurity is a fundamental requirement for protecting citizens and maintaining trust in the digital age.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: