In July 2019, Capital One, one of the largest banks in the United States, uncovered a breach that exposed sensitive data from over 106 million people across the U.S. and Canada. The attacker didn’t use malware or ransomware. Instead, she exploited a simple cloud misconfiguration, a single firewall rule left open in the bank’s Amazon Web Services (AWS) environment. The incident became a defining case of how one overlooked cloud setting can unravel the security of a global financial institution.
First time seeing this?
⚙️ How the Breach Happened
The attacker, later identified as Paige A. Thompson, a former AWS engineer, scanned the internet for misconfigured cloud resources. She found an exposed web application firewall (WAF) belonging to Capital One and launched a Server-Side Request Forgery (SSRF) exploit.
This tricked the WAF into executing her commands, granting access to AWS metadata services and, crucially, to an over-privileged IAM role. With those temporary credentials, Thompson used AWS command-line tools to list and copy data from roughly 700 private S3 buckets, extracting about 30 GB of customer information.
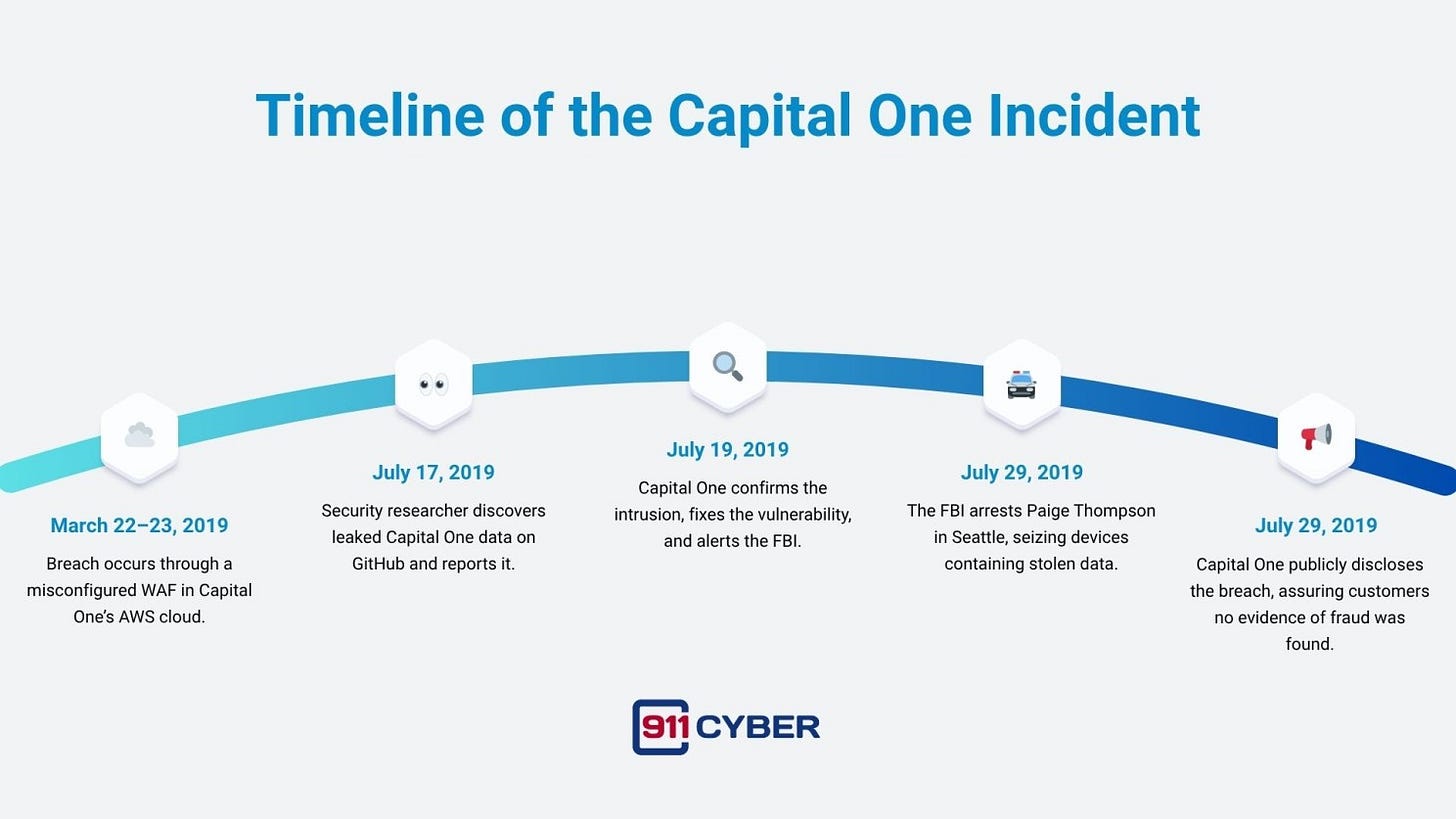
The vulnerability had been open since March 2019 and went unnoticed until a security researcher spotted snippets of Capital One’s data on GitHub and responsibly disclosed it in July 2019.
🗓️ Timeline of the Incident
💳 Who Was Impacted
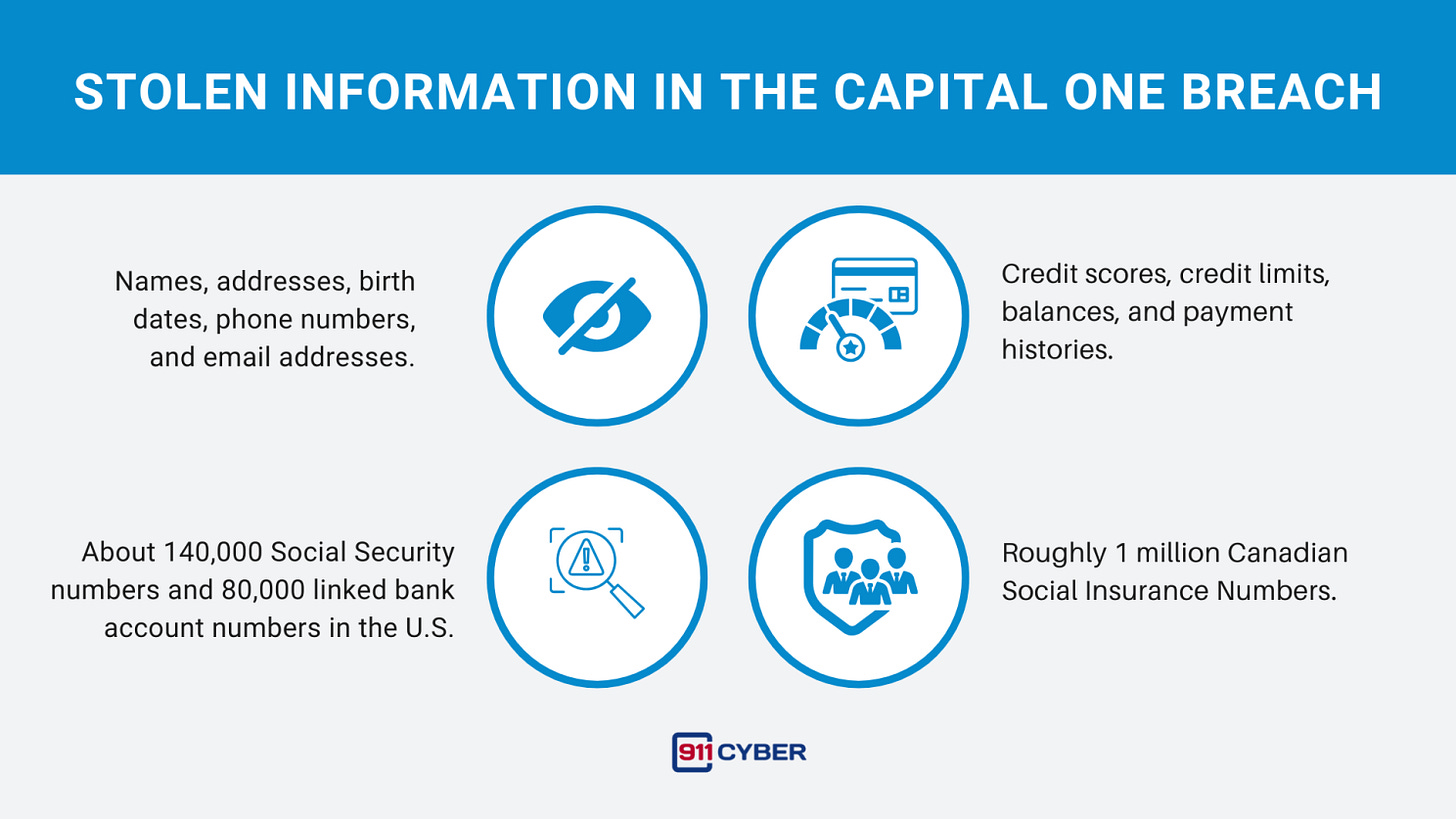
The breach compromised data from approximately 106 million individuals including 100 million in the U.S. and 6 million in Canada.
Thankfully, no credit card account numbers or login credentials were compromised. Still, this was among the largest data breaches ever recorded for a financial institution.
🎯 Attribution and Arrest
The hacker, Paige A. Thompson (alias “erratic”), acted alone. A former AWS employee, she exploited insider-level cloud knowledge to locate vulnerable systems across multiple organizations, not just Capital One. Her downfall was her own online bragging as she posted snippets of stolen data on GitHub under her real name.
The FBI swiftly tracked her down, and in July 2019, agents raided her home. Thompson was later convicted in 2022 of computer and wire fraud. By 2025, she remains under supervised release and owes $40 million in restitution. Her case underscores that even a single skilled insider can weaponize cloud knowledge for massive impact.
💰 Financial and Legal Fallout
Capital One’s total losses exceeded $270 million, including $80 million in regulatory fines and a $190 million class-action settlement with customers.
Regulators faulted Capital One for “ineffective risk management” during its cloud migration.
The Office of the Comptroller of the Currency (OCC) imposed the fine in August 2020, while the Federal Reserve mandated long-term cloud security audits.
The company pledged to invest an additional $100–150 million to strengthen security, launched continuous misconfiguration scanning, and expanded its cyber risk teams.
Capital One’s swift transparency and cooperation with law enforcement were credited with helping minimize secondary harm and preventing fraud from the stolen data.
🏛️ Industry Impact and Response
The breach reshaped cloud security practices across industries. It exposed weaknesses in the “shared responsibility model,” reminding companies that while cloud providers secure the infrastructure, customers must secure configurations and permissions. AWS responded by introducing IMDSv2, a new metadata service that requires authenticated sessions, blocking the SSRF technique used by Thompson.
By 2025, major organizations have adopted cloud security posture management (CSPM) tools that automatically detect misconfigurations, and many have shifted to secure-by-default cloud settings. The Capital One incident remains a benchmark case study in both cloud forensics and accountability.
🧩 Updates Through 2025
2022: Paige Thompson convicted on seven federal counts.
2023: Federal appeals court reviews her sentence for leniency but upholds probation.
2025: Capital One passes all regulatory audits and maintains a clean record.
Industry-wide, misconfiguration-related breaches have dropped due to automated security checks and better identity controls.
🛡️ How This Could Have Been Prevented
🕊️ Final Takeaway
The Capital One breach wasn’t the result of malware or nation-state espionage. It was a case of human error and over-privilege in the cloud. One misconfigured firewall, one exposed IAM role, and one motivated insider led to a $270 million disaster. The message is clear: in the cloud, every configuration is a potential gate to your kingdom. Secure it before someone else does.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: