In this edition of CyberCrimeStories, we look into a high-profile identity theft case that has shaken the sports world. Identity theft is one of the most financially and emotionally devastating crimes, and in this case, Earl Thomas, a Super Bowl champion and seven-time Pro Bowler, has fallen victim to a multi-million dollar scam.
The alleged perpetrator? His ex-wife’s boyfriend, Kevin J. Thompson. Let’s check out the details of this fraud and learn how to protect ourselves from similar attacks.
First time seeing this?
The Story:
Former NFL star Earl Thomas became the victim of a high-profile identity theft case in August 2020. The alleged mastermind behind the $1.9 million fraud, Kevin J. Thompson, who was Thomas’s ex-wife’s boyfriend, was arrested by the Jefferson Parish Sheriff’s Office in June 2023. Thompson faced multiple charges, including identity theft, forgery, money laundering, credit card fraud, computer fraud, and bank fraud.
This case underscores the vulnerability of even high-profile individuals to identity theft, especially in a digital age where personal information is increasingly exposed and exploited. Despite having significant resources, Thomas encountered considerable challenges in undoing the damage caused by the fraudsters and addressing the long-lasting consequences of having his identity stolen.
The Incident:
Thompson reportedly forged a driver’s license in Thomas’s name to create fraudulent bank accounts and transfer ownership of high-end vehicles, including a Rolls-Royce Cullinan. Thompson’s actions culminated in his arrest when he brazenly drove one of the stolen vehicles to a bank. This bold move, combined with suspicious activity noted by Thomas’s credit union in Texas, alerted authorities to the scam. The investigation has since widened, drawing in federal agencies due to the severity and intricacy of the allegations.
The Hack:
At the core of Thompson’s strategy was the exploitation of personal identification to falsify ownership and banking records. By forging a driver’s license and manipulating banking tools, Thompson was able to impersonate Thomas effectively, redirecting assets and funds undetected initially. The breach was sophisticated, involving multiple layers of fraud from false identification to the transfer and sale of stolen property.
The fraudulent activities were eventually detected, but only after considerable damage had been done. Thomas likely discovered the discrepancies upon reviewing his financial statements or receiving alerts from his financial institutions about suspicious activities.
What to Do in the Aftermath:
Victims of identity theft should take immediate action:
Report the identity theft to the Federal Trade Commission (FTC).
Notify affected creditors or banks.
Place fraud alerts and consider freezing your credit.
Review your credit reports for discrepancies.
Prevention Tips:
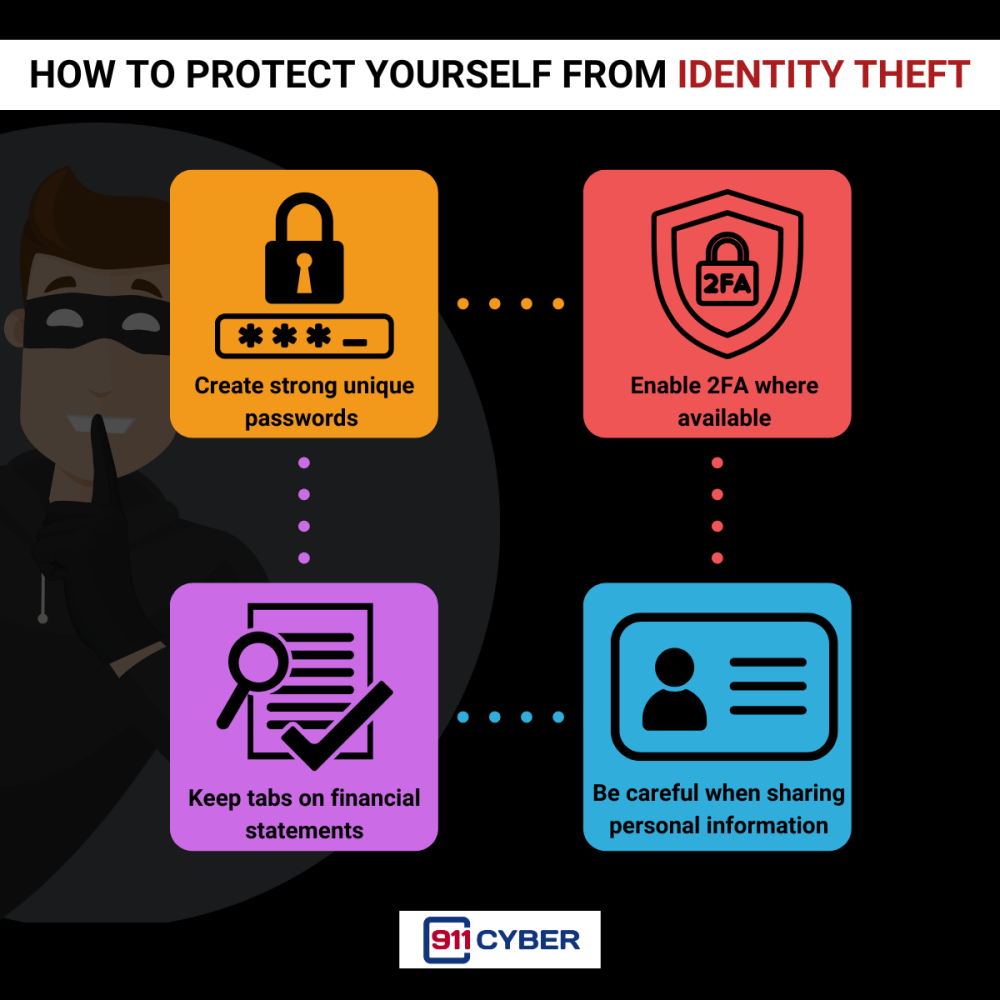
To protect yourself from similar situations:
Secure your personal information with strong, unique passwords for different accounts.
Enable two-factor authentication where available.
Regularly review your financial statements and credit reports.
Be cautious about how much personal information you share online.
Sign up for credit monitoring services to receive alerts about suspicious activity.
Tools for Prevention and Recovery:
IdentityForce - Monitors for suspicious activity on your personal accounts.
Credit Monitoring Services (e.g., Experian , TransUnion , or Equifax ) - Can alert you to potential financial identity theft.
FTC Complaint Assistant - A tool for reporting fraud and scams.
Report a Scam to 911Cyber - Can help you get immediate expert help
The ordeal faced by Earl Thomas is a reminder that no one is immune to cybercrime. By staying informed and vigilant, we can better protect ourselves and our sensitive information from such threats.
Some Useful Links:
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: