When cold storage and multisignature controls were not enough
Bybit is one of the world’s largest cryptocurrency exchanges. In February 2025, it became the victim of the largest crypto theft ever recorded, losing approximately 401,000 Ether valued at about $1.5 billion at the time.
What makes the Bybit incident historically significant is not only the amount stolen, but how it happened. The attackers did not brute force private keys or defeat cryptography. Instead, they compromised the human and software workflow that authorized legitimate transactions. The result was a perfect illusion. Authorized employees unknowingly approved the theft themselves.
This is the story of how the attack unfolded, why it worked, how the money moved, and what the incident teaches the entire crypto industry.
First time seeing this?
🧨How the Heist Happened
This was not a single exploit or a single failure. It was a multi stage operation combining social engineering, supply chain compromise, and transaction manipulation.
Initial Access Through Social Engineering
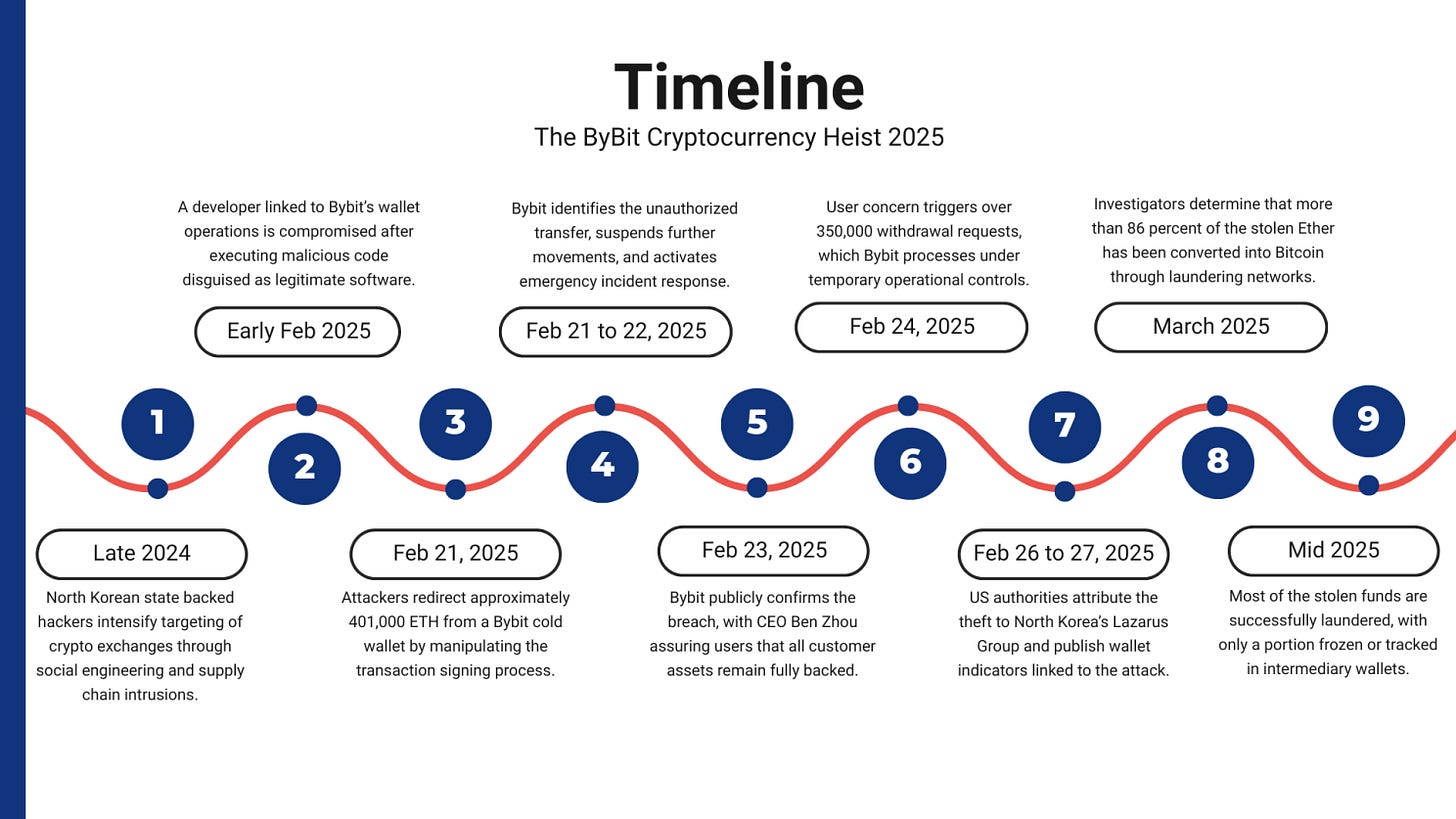
The attack began with the compromise of a developer connected to Bybit’s wallet infrastructure. The attackers posed as legitimate projects and convinced the developer to execute malicious code disguised as normal software. Once executed, the malware established persistent access while evading standard security controls.
This initial foothold was not inside Bybit’s cold wallet environment. It was inside a trusted workstation that sat upstream in the transaction signing and wallet management process.
Privilege Escalation and Internal Access
After gaining access to the developer environment, the attackers escalated privileges by abusing container configurations and trusted credentials. This gave them effective control over systems used to manage wallet operations.
From there, they conducted internal reconnaissance, accessed additional services, and leveraged trusted connections that were never designed to withstand a hostile insider level threat.
Compromise of the Signing Workflow
The most critical phase of the attack targeted the transaction signing process itself.
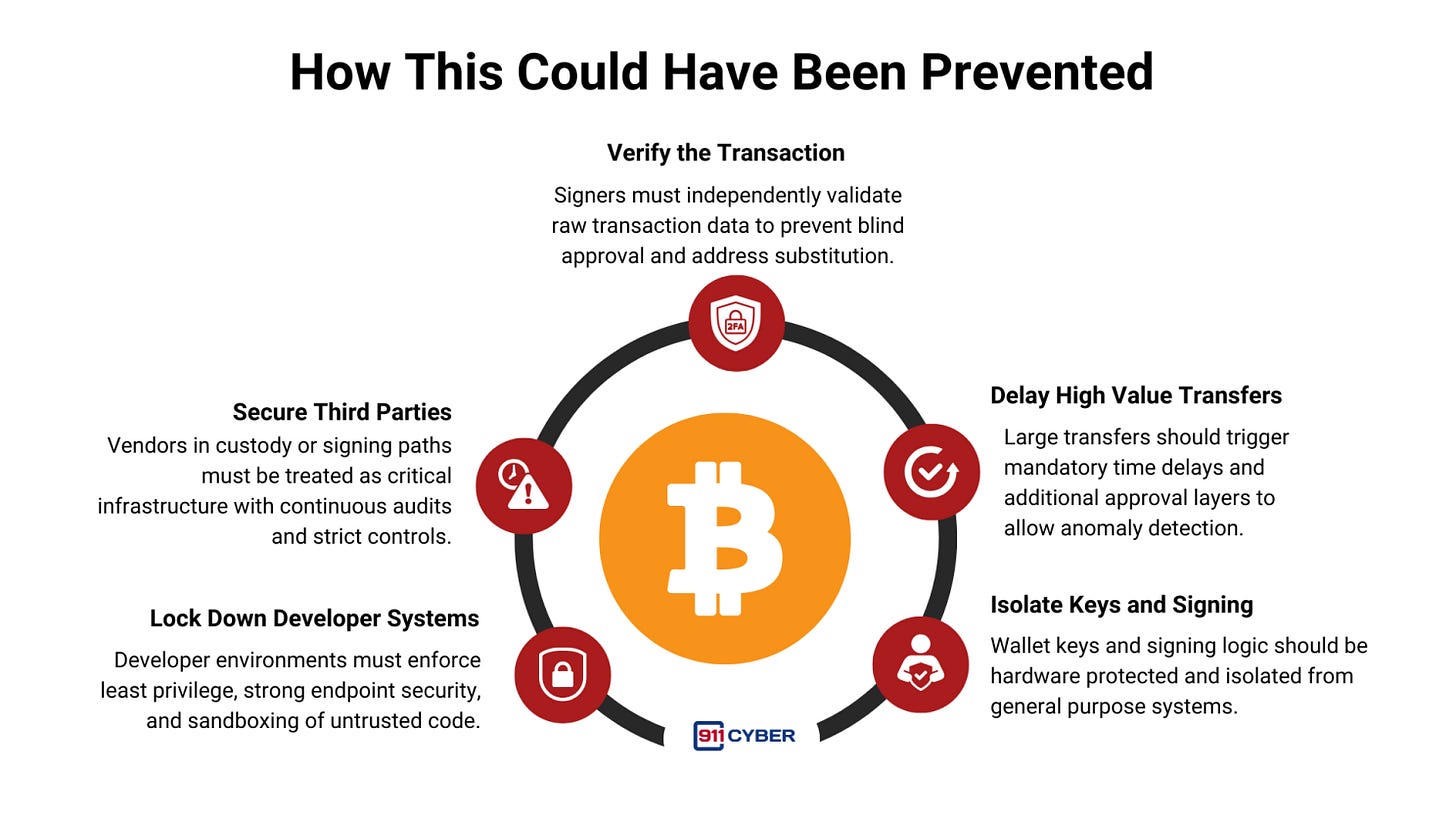
Bybit relied on a third party multisignature wallet platform to coordinate transfers from cold storage to operational wallets. After breaching this environment, the attackers injected malicious code into the transaction signing interface.
The injected code did not trigger alarms. It waited.
When a transaction met specific criteria, namely a large Ether transfer, the interface displayed the expected destination address to Bybit employees. Under the hood, however, the actual destination was silently replaced with an attacker controlled address.
This is the core failure point. The signers approved exactly what they believed they were seeing. The multisignature process worked as designed, but it validated a lie.
Execution of the Theft
On February 21, 2025, Bybit initiated what appeared to be a routine internal transfer from cold storage to a warm wallet. Approximately 401,000 ETH was approved through the normal multisignature process.
Within minutes, the funds were transferred directly to the attackers’ wallet.
The theft was only detected after the funds failed to arrive at the intended destination. By then, the transaction was final.
Covering Tracks
Immediately after the transfer, the attackers worked to erase evidence of their activity. Logs were altered, access paths were obscured, and legitimate tools were abused to blend malicious behavior into normal operations.
This delayed forensic reconstruction and bought the attackers critical time to begin laundering the funds.
🗓️Timeline
🧾What Was Stolen
The theft consisted primarily of Ethereum.
Approximately 401,000 ETH was stolen in a single coordinated event, making it the largest known cryptocurrency theft in history. The value at the time of the incident was estimated at $1.5 billion.
No evidence has surfaced that customer account balances were directly drained. The stolen assets came from exchange controlled wallets, and Bybit absorbed the financial loss.
🔄Following the Money
The laundering phase began almost immediately after the theft.
⚠️Rapid Dispersal
The attackers employed a flood the zone strategy, splitting the stolen assets across thousands of addresses and multiple blockchains. This overwhelmed monitoring systems and shortened the window for effective interdiction.
⚠️Conversion to Bitcoin
In line with previous North Korean operations, the majority of Ether was converted into Bitcoin. Bitcoin’s transaction model makes long term tracing more difficult once funds are sufficiently mixed and fragmented.
By late March 2025, more than 86 percent of the stolen Ether had been converted.
⚠️Mixing and Obfuscation
The attackers used a layered laundering strategy involving cross chain bridges, decentralized exchanges, CoinJoin services, and peer to peer brokers. Some funds were routed through obscure networks and refund mechanisms to deliberately break expected audit trails.
This laundering effort was unprecedented in both speed and scale.
💻Attribution to Lazarus Group
Attribution in the Bybit case was unusually clear.
US authorities confirmed that the theft was carried out by North Korea’s Lazarus Group, operating under the TraderTraitor campaign. The tactics matched prior Lazarus operations targeting crypto exchanges, including social engineering, supply chain compromise, and rapid asset conversion.
The laundering behavior, tooling, and operational discipline aligned closely with previous North Korean crypto thefts, which have been linked to funding the country’s nuclear and missile programs.
🛠️Bybit’s Response and User Impact
🔍 Solvency and Reassurance
Bybit immediately assured users that all customer assets were fully backed and that the company could absorb the loss. The exchange reportedly held approximately $20 billion in assets at the time.
This commitment prevented a full scale collapse in confidence.
🔍Withdrawal Surge
The disclosure triggered a massive withdrawal spike, with more than 350,000 requests submitted within a single day. Some users experienced delays, but withdrawals continued and no customers ultimately lost funds due to the theft.
🔍 Operational Controls
Bybit suspended affected wallet operations, rotated keys, audited infrastructure, and introduced additional transaction monitoring and approval safeguards. The exchange also warned users about phishing attempts and fake recovery schemes exploiting the incident.
🎣Secondary Effects and Scams
As with many major breaches, the aftermath saw a surge in phishing and impersonation attacks. Hundreds of fake domains and messages appeared, claiming to offer recovery assistance or compensation.
Some scams promoted fake Bybit related tokens or requested users’ private keys under the guise of verification. Bybit worked with security firms to take down malicious infrastructure and repeatedly warned users to rely only on official channels.
⚖️Regulatory and Industry Impact
The scale of the theft elevated the incident beyond the crypto sector.
Lawmakers framed the event as a national security issue, citing the role of crypto theft in funding sanctioned states. Regulators began questioning whether existing security and compliance requirements for exchanges were sufficient.
Across the industry, exchanges reassessed wallet architectures, third party dependencies, and signing workflows. Several introduced stricter withdrawal delays, independent transaction verification, and enhanced vendor oversight.
🧠How This Could Have Been Prevented
🕊️ Final Takeaway
The Bybit heist was not a failure of cryptography. It was a failure of trust in the approval process.
When attackers can control what authorized humans believe they are signing, even cold storage and multisignature safeguards can be defeated.
This incident delivered a hard lesson to the crypto industry. Security does not end at keys and wallets. It extends through every human decision, every interface, and every dependency involved in moving value.
The question every exchange must now ask is simple and uncomfortable. If our signing interface lied to us today, what would stop us from approving the theft ourselves?
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: