In late 2023, threat actors quietly accessed a cloud-based “data lake” used by Jollibee Foods Corporation (JFC) across multiple brands. The breach stayed invisible for months. It only surfaced publicly in June 2024 when a hacker posted on a cybercrime forum advertising what they claimed was a massive trove of Jollibee customer data.
By the time the public found out, the damage was already done. Millions of customers had their personal information exposed, and the data was being treated like a commodity.
First time seeing this?
🧾 What happened
Jollibee later confirmed the attackers did not need to take down websites or disrupt operations to succeed. This was a data theft operation.
The attackers gained unauthorized access to a cloud data storage platform that acted as a centralized data lake for JFC brands. Instead of attacking a public-facing app directly, they targeted the back-end repository where delivery and customer records were aggregated at scale.
This is what made the breach so severe. Once access to the data lake was obtained, the attacker’s “blast radius” expanded immediately across multiple brands and datasets.
🗓️ How the attackers likely got in
Early reporting and the broader pattern around similar breaches in the same period suggests a familiar entry point, stolen credentials.
Investigators and reporting tied the incident to a wider wave of credential-based attacks on cloud data environments, where passwords harvested by infostealer malware were used to log into accounts that lacked strong access controls, particularly multi-factor authentication.
If that was the case here, the attacker did not need to exploit a complex technical vulnerability. They simply needed valid access.
Once inside, the likely playbook was quiet bulk querying and exfiltration over time, designed to avoid triggering alarms. If meaningful database activity monitoring and anomaly detection were missing or poorly tuned, large-scale data theft could occur without immediate detection.
🗂️ What data was exposed
The breach affected an estimated 11 million individuals, making it one of the largest publicly reported data breaches in the Philippines.
Jollibee’s notification to regulators confirmed that sensitive personal information was exposed, including dates of birth and senior citizen ID numbers for some customers. These details alone significantly increase the risk of identity fraud, particularly for elderly individuals.
Independent reporting and analysis of alleged data samples suggest the compromised dataset was far more extensive. The stolen information reportedly included customers’ full names, home addresses, phone numbers, email addresses, as well as detailed delivery order histories and transaction records spanning multiple years.
Some reports also alleged the presence of credit card numbers and account passwords within the leaked data. Jollibee has not publicly confirmed whether full payment card details were included, and it remains unclear whether any financial data was tokenized, partially stored, or protected in line with payment security standards. Even without confirmed payment data, the exposure remains severe.
What makes this breach especially dangerous is the inclusion of order history and behavioral data. Knowing what a customer ordered, when it was delivered, and to which address enables highly convincing phishing and impersonation scams. A fraudulent message referencing a real past order is far more likely to be trusted, increasing the success rate of social engineering attacks.
In short, this was not just a leak of contact details. It was a detailed snapshot of customer identity and behavior, precisely the kind of data cybercriminals value most.
🚨 Who was behind it
The breach was widely attributed to a threat actor using the handle “Sp1d3r”.
In June 2024, the Sp1d3r account posted about the Jollibee dataset on a cybercrime forum, claiming possession of 32 million unique records totaling roughly 650 million entries, and listing the database for sale with an asking price reported around $40,000.
This actor was also linked in reporting to a broader pattern of cloud datastore compromises in 2023 to 2024, including other large, high-profile organizations. The consistent theme across those incidents was monetization: steal large datasets, then sell them, trade them, or use them as leverage.
There was no clear sign of political motive here. The intent looked commercial. Data as inventory.
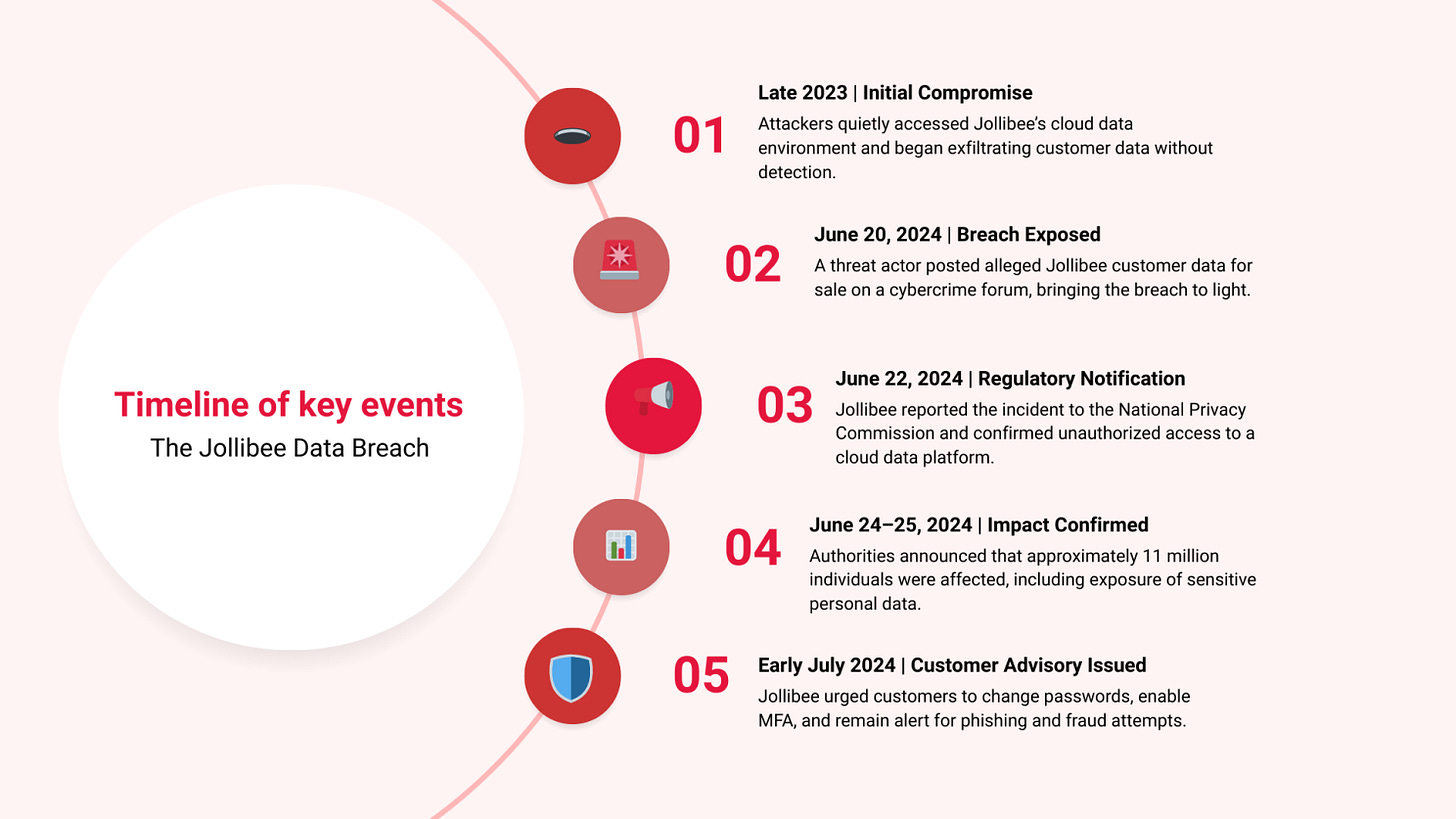
🗓️ Timeline of key events
🚨 Impact
This was not a ransomware incident. There were no public reports of systems being encrypted, stores shutting down, or services collapsing.
That is precisely why it is a modern case study.
Data theft attacks can be “silent” and still do enormous damage:
Phishing and impersonation: Names, addresses, phone numbers, and order details make scams highly believable.
Identity fraud: Birthdates and government-linked identifiers increase identity theft risk.
Account takeover: If passwords were included, or if victims reuse passwords, secondary compromise becomes possible.
Long-tail harm: Data does not expire. It can be resold repeatedly, repackaged, and used months later.
For the business, the cost is not just remediation. It is reputational damage, customer trust erosion, and regulatory scrutiny. The incident also forces hard questions about how long customer data is retained and who has access to centralized repositories.
🛡️ Jollibee’s response
Jollibee’s response focused on containment, coordination, and communication.
The company stated it activated incident response measures, enhanced security controls, and worked with law enforcement and external experts. It also emphasized that front-end ordering systems were not directly compromised and remained functional.
Publicly, Jollibee issued advisories that encouraged customers to:
Update passwords
Turn on multi-factor authentication
Be vigilant against scams
Monitor accounts and financial activity
Rely on official communications only
From a crisis communications standpoint, this response aimed to strike a balance: acknowledge the breach, demonstrate action, and reduce panic by clarifying that ordering platforms were still operating.
⚖️Regulatory and Industry Impact
The scale of the theft elevated the incident beyond the crypto sector.
Lawmakers framed the event as a national security issue, citing the role of crypto theft in funding sanctioned states. Regulators began questioning whether existing security and compliance requirements for exchanges were sufficient.
Across the industry, exchanges reassessed wallet architectures, third party dependencies, and signing workflows. Several introduced stricter withdrawal delays, independent transaction verification, and enhanced vendor oversight.
⚖️ Regulatory fallout
The case is governed primarily by the Philippines Data Privacy Act of 2012 and overseen by the National Privacy Commission.
The NPC acknowledged Jollibee’s notification and monitored the company’s investigation and remediation. Regulatory investigations can take time, but the key questions typically revolve around whether reasonable security safeguards were in place, and whether breach reporting and consumer notification obligations were met.
This incident also became part of a broader conversation about cloud security failures and credential-based intrusion campaigns affecting multiple organizations.
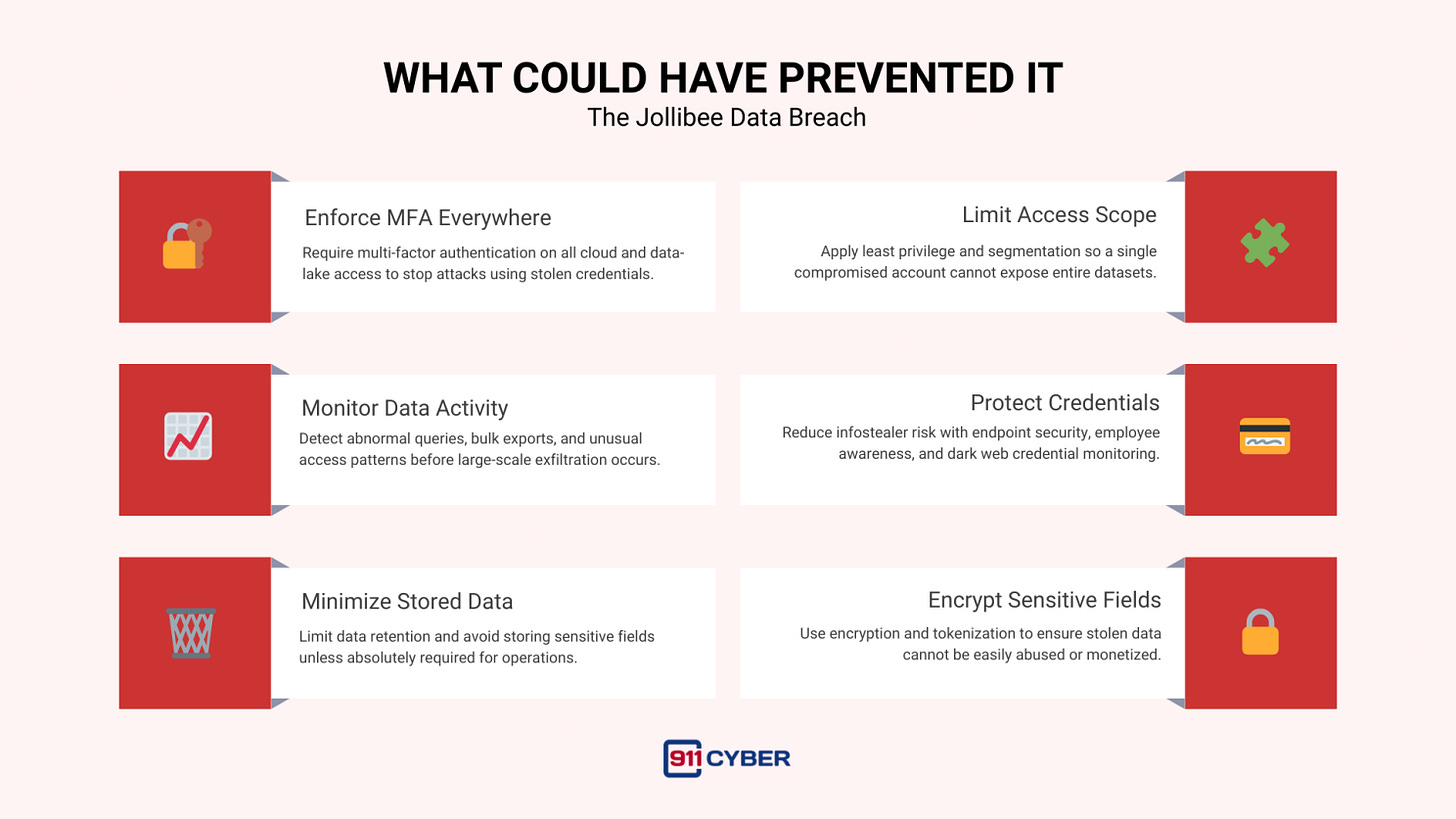
🧠 What could have prevented it
This breach reads like a checklist of cloud security fundamentals that cannot be optional:
The uncomfortable lesson is that many breaches are not “advanced.” They are operational failures at scale. The attacker’s hardest work is often finding valid credentials. After that, the organization’s own architecture determines how big the breach becomes.
✅ Closing
Jollibee did not lose customer trust because it was hacked. It lost trust because customer data was centralized, accessible, and valuable enough to be sold.
This incident is a warning to every consumer brand building digital-first loyalty and delivery ecosystems: when you become a data company, you become a target like one.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: