Many had strong technical security. The weakness was hiring and identity proofing, not firewalls.For most companies, “remote work” sounds like flexibility, talent from anywhere, and lower office costs. For North Korea, it became something else entirely, a quiet way to slip state backed operatives into Western networks, collect salaries in hard currency, and sometimes steal data and cryptocurrency on the side.
From roughly 2018 onward, North Korean IT specialists posing as ordinary developers and engineers began applying for remote jobs at companies in the United States, Europe, and Asia. They used stolen identities, polished resumes, and domestic helpers who ran “laptop farms” inside American homes.
On paper they were senior React developers in Texas, DevOps engineers in Poland, or blockchain experts in Canada. In reality they were working for the Lazarus Group and other units tied to North Korea’s intelligence services, with most of their pay seized by the regime to fund weapons programs.
By 2025, United States authorities had exposed parts of this scheme, arrested several facilitators, and seized millions of dollars. The case has become a landmark example of how nation states now exploit the remote work economy.
First time seeing this?
⚙️ How The Scheme Worked
At its core, the Lazarus remote worker operation was not technical wizardry. It was a long confidence trick that exploited hiring processes and weak identity checks.
Stolen or borrowed identities
North Korean operators rarely used their real names. They bought or stole identities of real people, often Americans. These identity packages included names, dates of birth, addresses, Social Security numbers, and scans of passports or driver licences. Some helpers even sold “fully ready” profiles that matched LinkedIn and freelance platforms.
Convincing fake professionals
Using those identities, operatives built resumes that looked very strong. It had years of experience, cloud and DevOps skills, crypto or fintech projects, and even glowing references. They were fluent enough in English to pass interviews and sometimes used AI tools to prepare coding test answers or scripts for technical questions.
Laptop farms
When a company hired one of these “remote employees” and shipped them a laptop, it rarely went to North Korea directly. The devices were sent to an address in the United States or another country, controlled by a local facilitator. That person connected dozens of employer laptops in racks at home, installed remote desktop software, and handed over access to the North Korean workers.
From the company’s point of view, the device lived at a domestic address and logged in from a normal broadband connection.
In reality, the real user might be sitting in China or Russia, connecting over VPN to a machine in Phoenix or Nashville.
Legitimate access, illegitimate purpose
Once hired, these workers performed real tasks. They wrote code, joined standups, fixed bugs, and collected paychecks. Most of the money was then routed through intermediaries and converted to cash or cryptocurrency that North Korea could access.
In some cases, the workers went further, copying proprietary code, stealing internal documents, or manipulating systems to steal crypto assets.
The clever twist? The initial access was not gained through exploits or phishing, but by being invited in as “staff.”
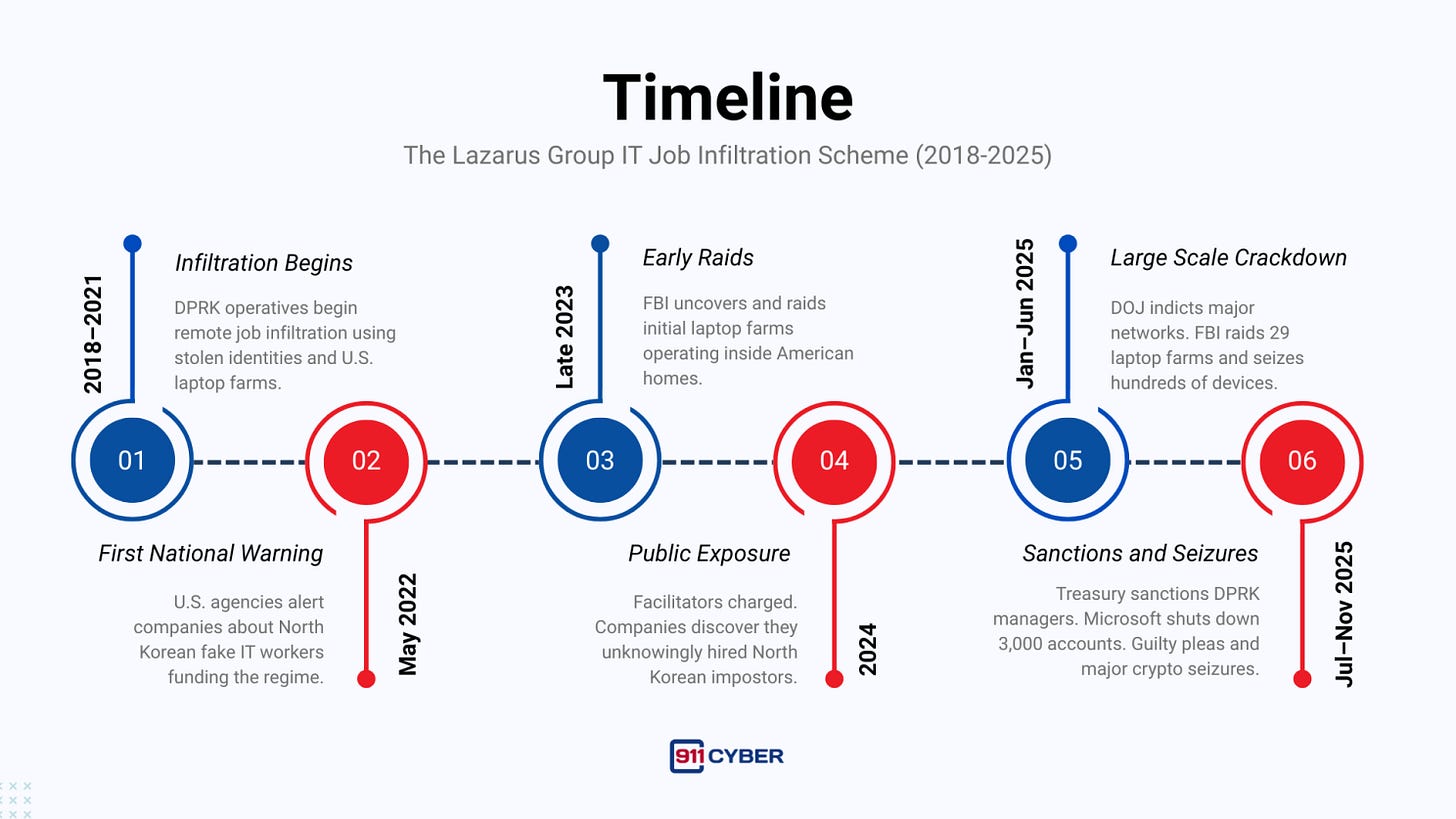
🗓️ Timeline: From Quiet Growth To Crackdown
🌍 What Was Stolen And Who Was Impacted
This was not a classic “data breach” with one victim and a single moment of compromise. Instead it created a long tail of harm.
Money and cryptocurrency
North Korean workers collected legitimate salaries from foreign companies. Estimates vary, but public cases alone add up to tens of millions of dollars. In parallel, a handful of insiders used their positions to steal cryptocurrency directly from their employers, diverting hundreds of thousands of dollars per incident.
Personal identities
To run these personas, the scheme abused identities of real people. Dozens of Americans had their names and Social Security numbers used on job applications, tax forms, and employment records without their knowledge. Some only discovered the problem when they received tax notices for income they had never earned.
Corporate access and intellectual property
The most serious impact was access to internal systems. These “employees” could see source code, architecture diagrams, and customer data. In at least one case, they reached export controlled defense information. Even when no active sabotage or theft was detected, the trust cost was high. Every company that discovered a North Korean impostor had to assume that anything accessed by that account might be compromised.
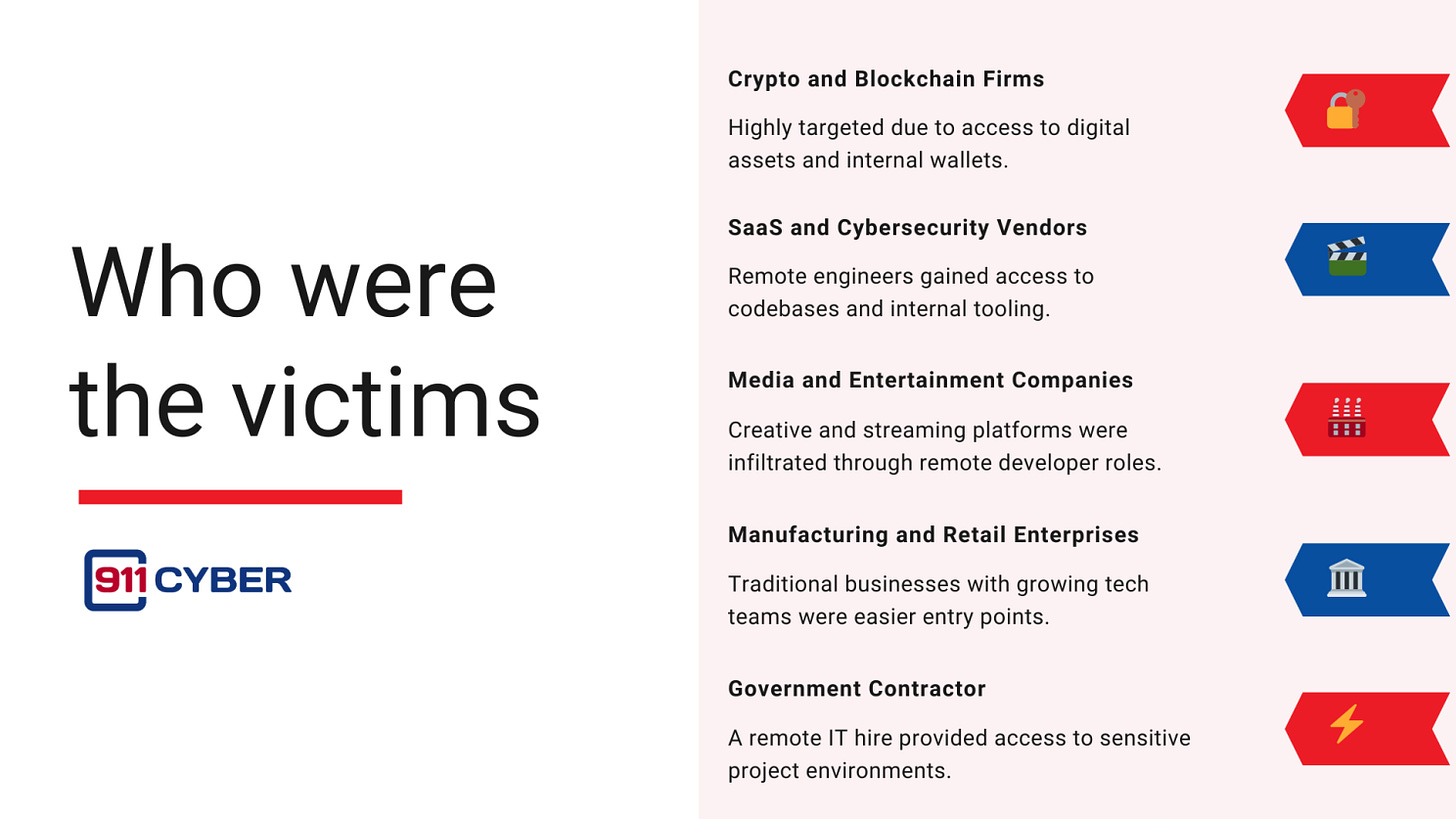
Who were the victims
Many had strong technical security. The weakness was hiring and identity proofing, not firewalls.Victim organisations ranged from small startups to large enterprises:
🧠 Unmasking The Attackers
The scheme began to unravel because people noticed things that did not add up.
Recruiters saw candidates with identical resumes under different names. Engineers noticed colleagues who always refused video, or whose accent did not match their claimed background. Some security teams flagged remote employees who never logged in from expected time zones, even though their HR records listed a United States address.
Law enforcement pulled on those threads. Search warrants on laptop farms revealed chat logs between facilitators and overseas handlers, spreadsheets listing “worker” identities and salaries, and shipping records for corporate hardware. Blockchain analysis linked stolen cryptocurrency to wallets already connected to Lazarus Group.
At the same time, large tech companies examined their own platforms. One provider took down thousands of email accounts used by North Korean IT workers and helped seize domains they operated for recruiting and file transfers.
Gradually, investigators could name the actors: specific North Korean units, managers who coordinated the work, and foreign brokers who sold identities or hosted devices. That evidence underpinned indictments and sanctions.
🏢 Company Responses
Once notified, most affected companies did three things:
Cut access immediately Accounts were disabled, VPN credentials revoked, and devices locked or wiped. Some firms invalidated SSH keys and API tokens that the impostor might have used.
Investigated the blast radius Security teams reviewed logs to see what the false employee accessed or downloaded. They looked for unusual code changes, data exports, or signs of lateral movement. In crypto and fintech companies this included tracing any on chain transfers that might be linked to the account.
Strengthened hiring processes Many organisations updated background checks for remote workers, added live identity verification, and introduced probationary monitoring for new technical staff. Some now require at least one in person or trusted third party identity check before granting access to sensitive systems.
🎯 Government Reaction
Governments treated this as more than fraud. It was seen as sanctions evasion and a national security risk.
Key elements of the response included:
Joint advisories from law enforcement and cyber agencies that described the tactics, listed red flags, and urged businesses to tighten remote hiring.
A specialised task force focused on North Korean revenue operations, combining cyber investigators, sanctions experts, and financial intelligence analysts.
Public press conferences that named North Korean units and explained that the workers’ incomes were used to support missile and weapons programs.
Engagement with allies, especially in South Korea and Europe, to share intelligence on identities, infrastructure, and front companies.
This multi agency approach signalled that the remote worker scheme was not viewed as a niche IT fraud, but part of North Korea’s broader strategy to survive sanctions.
⚖️ Legal And Regulatory Fallout
Legal consequences have already been significant and are still unfolding.
Criminal cases
Several United States based facilitators have pleaded guilty to wire fraud, identity theft, sanctions violations, and money laundering. Sentences include lengthy prison terms and forfeiture of profits. Cases against named North Korean operators are largely symbolic for now, but they restrict travel and make future arrests possible if those individuals leave friendly territory.
Sanctions
The United States Treasury has designated North Korean government departments, front companies, and individuals involved in managing the IT worker program. This freezes assets under United States jurisdiction and prohibits United States persons from dealing with them. Sanctions also cover some foreign partners who knowingly provided infrastructure or contracting services.
Financial seizures
Courts have ordered the seizure of salaries, bank balances, and cryptocurrency wallets linked to the scheme. Some recovered funds are earmarked for restitution to companies and crypto platforms that were victimised.
Regulators are now looking at whether additional rules are needed for government suppliers and critical infrastructure providers, for example stronger identity proofing for remote staff with access to sensitive systems.
🧩 Aftermath And Legacy
From 2018 to 2025, North Korea quietly turned remote work into a revenue engine. The exposure and takedown of this scheme leaves several lasting lessons.
Remote work is an attack surface Hiring processes and HR systems are now firmly inside the security perimeter. Boards and CISOs talk not only about patching servers, but about verifying who is on payroll.
Insider threat models must evolve Traditional insider risk programs focused on disgruntled staff or bribed employees. Organisations now have to consider the possibility that some insiders were never who they claimed to be.
Sanctions enforcement is moving into HR and gig platforms Financial and labour sanctions on North Korea are no longer only about shipping, banking, or arms. They now affect freelance portals, staffing agencies, and even small businesses that hire remote developers.
North Korea will adapt The scheme has been disrupted but likely not eradicated. We can expect variations targeting different regions or using more sophisticated deepfakes and cut outs. Awareness gained during this case will help defenders, but vigilance has to continue.
The Lazarus remote worker scheme has already become a case study in cyber policy circles. It shows how a state can blend cyber operations, fraud, and labour markets into one continuous campaign.
🛡️ How This Could Have Been Prevented
🕊️ Final Takeaway
The Lazarus remote worker scheme was not a story of zero day exploits. It was a story of trust placed in the wrong people.
By exploiting the convenience of remote work and the pressure to fill technical roles quickly, a sanctioned regime managed to sit inside hundreds of foreign companies, earn millions of dollars, and occasionally steal sensitive data, while pretending to be ordinary employees.
The investigation and crackdown showed that when law enforcement, intelligence agencies, and the private sector share information, even a long running scheme of this scale can be exposed and disrupted.
The lesson for everyone else is straightforward. Cybersecurity now starts long before the first login, it starts at the job application stage. Remote work is here to stay, so careful identity verification, thoughtful access control, and a healthy level of skepticism have to stay with it.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: