The Ryuk Ransomware Attack on Universal Health Services, 2020
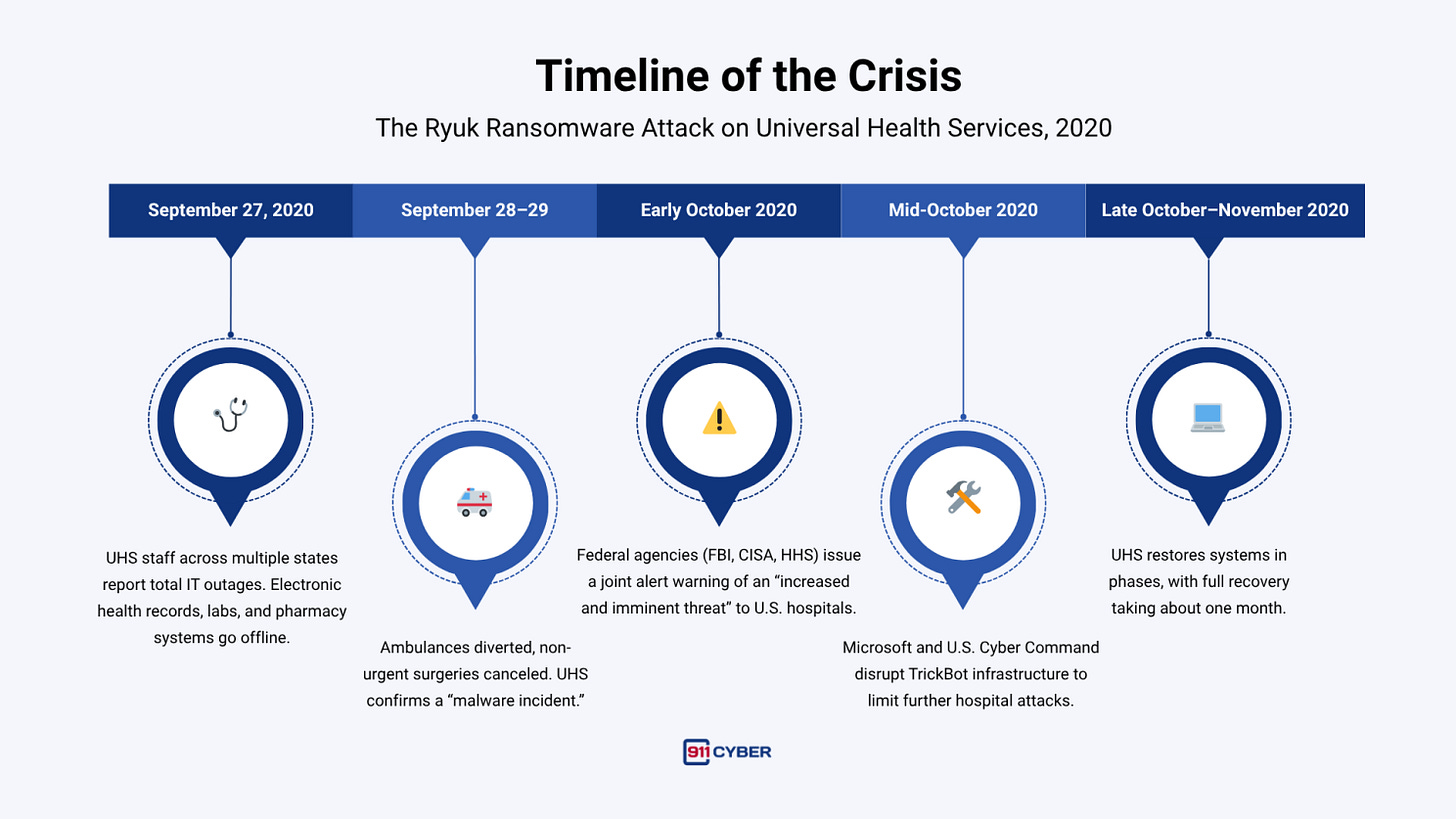
On the night of September 27, 2020, as doctors and nurses worked through the pandemic’s chaos, one of America’s largest hospital networks suddenly fell silent. Screens froze. Systems locked. Across more than 400 facilities, Universal Health Services (UHS) watched its digital backbone collapse.
Ambulances were rerouted, surgeries postponed, and clinicians returned to pen and paper to keep patients alive. The culprit was Ryuk ransomware, a ruthless cyber weapon that paralyzed a healthcare giant when lives depended most on uptime.
First time seeing this?
⚙️ How the Attack Happened
Investigators later traced the outage to Ryuk ransomware, deployed by a Russian-speaking cybercrime syndicate known as Wizard Spider. Their method was methodical. Attackers likely entered UHS’s network weeks earlier through phishing emails carrying TrickBot or BazarLoader malware, silently harvesting credentials and mapping systems before the strike.
Once Ryuk was unleashed, it executed with surgical precision—terminating over 200 processes, disabling antivirus tools, and encrypting data across servers and endpoints using AES-256 and RSA-4096 encryption.
Even computers that were asleep were awakened through Wake-on-LAN, ensuring no machine escaped encryption. Within hours, hundreds of hospitals were offline.
🗓️ Timeline of The Ryuk Ransomware Attack
🏥 Impact on Healthcare
The Ryuk attack wasn’t just a digital crisis—it was a public health emergency. Across UHS hospitals, clinicians reverted to manual workflows: handwritten prescriptions, physical lab orders, and phone-based coordination. Test results were delayed, and some patients were rerouted to other facilities.
While UHS avoided confirmed fatalities, the event exposed how cyberattacks can directly threaten patient safety. In one related case overseas, a ransomware attack forced a German hospital to divert a critical patient, who later died. UHS’s ordeal became a grim warning: when IT fails, patient care falters.
🎯 Who Was Behind It
The Ryuk operation was attributed to Wizard Spider, also known as UNC1878, a sophisticated Russian-speaking cybercrime group responsible for a wave of hospital attacks in 2020.The group had previously run TrickBot and later evolved into Conti, a successor ransomware that earned over $180 million in 2021.
While financially motivated, these gangs operate from Russia and nearby countries where they enjoy de facto immunity, as long as they attack foreign targets. By 2023, U.S. and UK authorities sanctioned seven individuals linked to the Ryuk and Conti networks, marking the first joint sanctions against ransomware operators.
💰 Financial and Legal Fallout
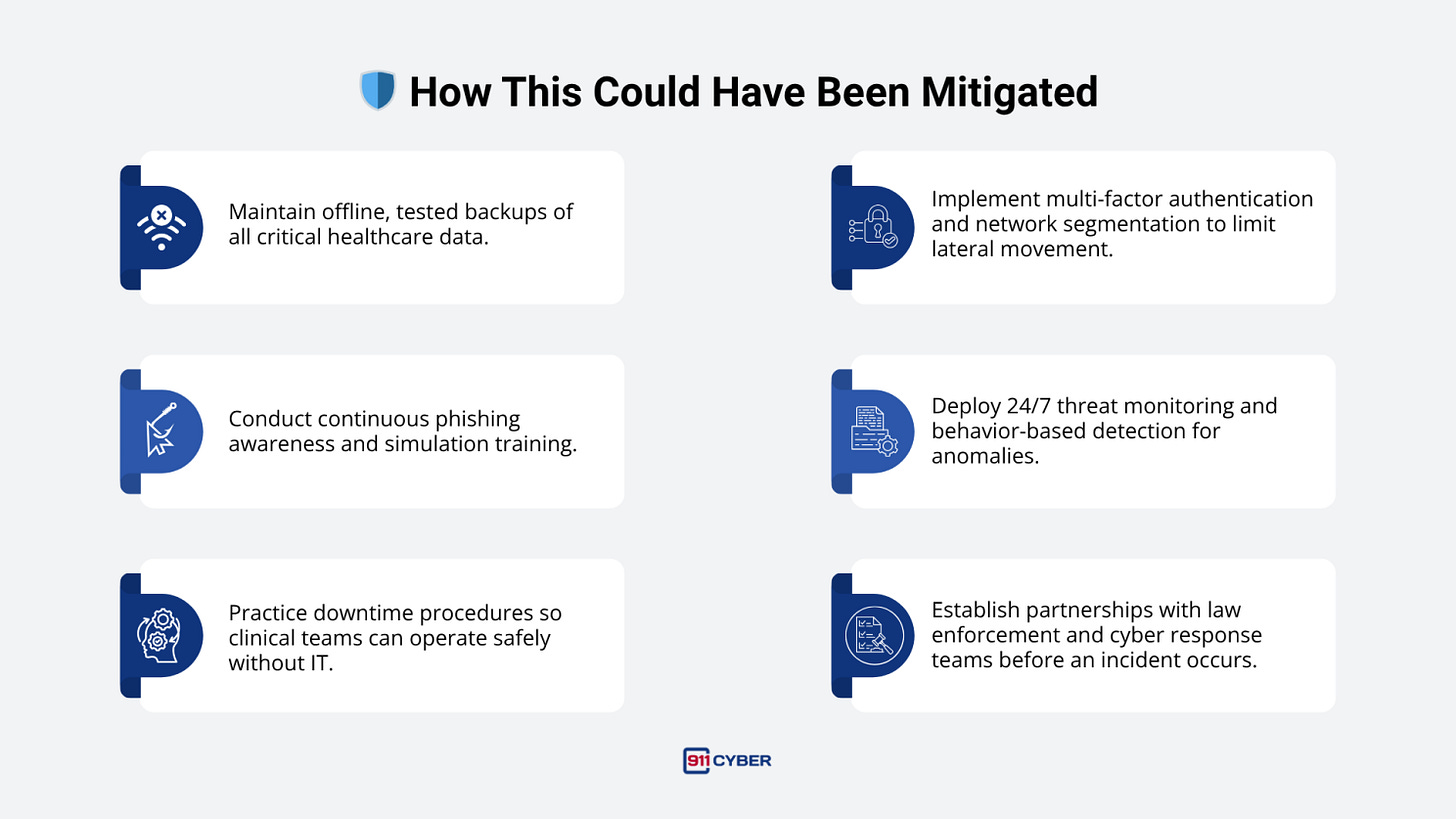
UHS reported $67 million in pre-tax losses from the attack, covering recovery costs, downtime, and lost revenue. Ambulance traffic and surgeries diverted to competitors reduced earnings, and IT restoration required “significant incremental labor.” UHS said it relied on backups rather than paying a ransom, a decision that spared it from potential sanctions violations.
Several patient lawsuits followed, including one alleging negligence after a canceled surgery caused loss of employment and health insurance. A federal judge allowed that case to proceed—one of the first to recognize patient harm from a cyberattack as a valid negligence claim.
🏛️ Industry and Government Response
The attack triggered an unprecedented mobilization across healthcare and government. Within weeks, the FBI, CISA, and HHS issued a national alert warning hospitals of imminent ransomware attacks using the same TrickBot infrastructure. At least 20 additional hospitals were hit in October 2020 alone.
Microsoft and U.S. Cyber Command launched coordinated efforts to dismantle TrickBot’s servers. The American Hospital Association called ransomware targeting hospitals “attacks on human life.” By 2021, the Ransomware Task Force and H-ISAC pushed for tougher reporting rules, insurance reforms, and sector-wide resilience training.
🧩 Updates Through 2025
2021–2023: Law enforcement arrested TrickBot developers, dismantled Emotet, and sanctioned Russian operators tied to Ryuk and Conti.
2022: The U.S. State Department offered a $10 million reward for information leading to Conti leaders.
2023: The U.S. and UK sanctioned seven Russian hackers; a Ukrainian affiliate was extradited to the U.S.
2024–2025: UHS has reported no further ransomware incidents and has strengthened its defenses. Industry-wide, hospitals adopted Zero Trust, offline backups, and mandatory downtime drills.
🛡️ How This Could Have Been Mitigated
🕊️ Final Takeaway
The Ryuk ransomware attack on UHS was more than a corporate breach. It was a moment when digital failure nearly translated into physical harm. A single phishing email cascaded into a month of disrupted care, $67 million in losses, and a national reckoning over hospital cybersecurity. From 2020 to 2025, the lesson remains urgent: cybersecurity is patient safety.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: