The SimonMed Imaging Ransomware Intrusion
SimonMed Imaging is not a household name, yet it plays a critical role in modern healthcare. As one of the largest outpatient radiology providers in the United States, it handles diagnostic scans, clinical reports, billing data, and the personal information that links patients to deeply private medical decisions.
In early 2025, that trust was tested.
A ransomware intrusion attributed to the Medusa cybercrime group did not shut down imaging centers or cancel appointments. Instead, it followed a more modern and often more damaging path. Data was stolen first. Systems stayed online. Extortion followed later.
What emerged was one of the largest healthcare data exposure events of 2025, ultimately affecting more than 1.27 million patients across multiple states, with Arizona at the center.
First time seeing this?
⚙️ How the Intrusion Happened
The attack did not begin with a noisy exploit or a visible outage. It began quietly through a third party.
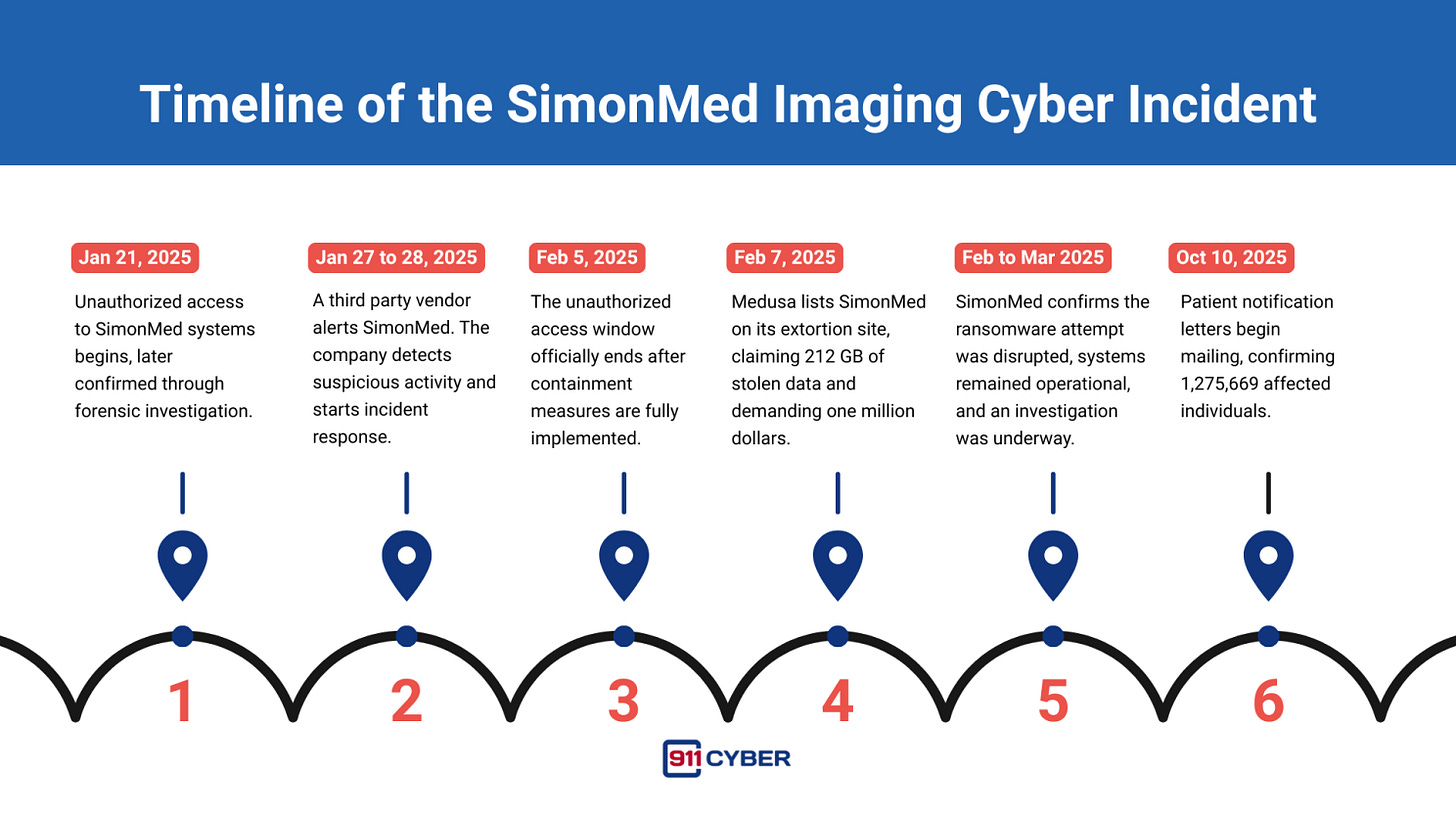
On January 27, 2025, one of SimonMed’s vendors notified the company that it was experiencing a security incident. The next day, SimonMed identified suspicious activity inside its own network. A later forensic investigation determined that unauthorized access had already been present since January 21 and continued until February 5.
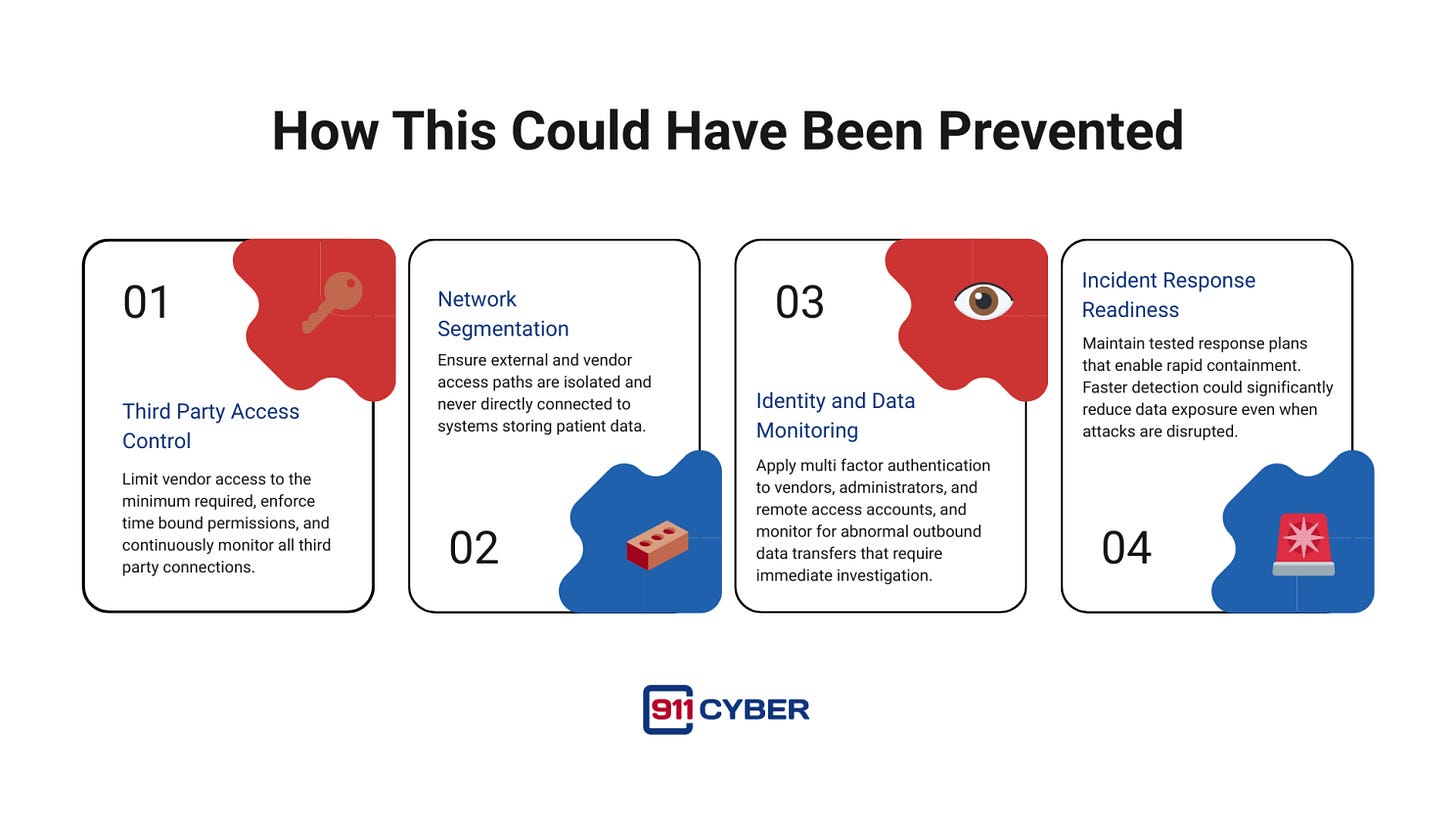
The attackers used a supply chain entry point. A trusted connection that likely had persistent access and broad permissions became the path inward. Once inside, the intruders moved laterally, accessed sensitive systems, and exfiltrated large volumes of data without triggering immediate alarms.
This reflects a shift in ransomware operations. Many groups no longer rush to encrypt systems. They steal data first, knowing that even if encryption fails, the stolen information itself can be weaponized.
SimonMed later stated that it interrupted the attack before any systems were encrypted and that operations continued without disruption. From a clinical standpoint, the damage was avoided. From a confidentiality standpoint, it was already done.
🗓️ Timeline
🌍 Who Was Impacted
SimonMed operates more than 170 imaging centers across approximately ten states. The breach impacted patients across this entire footprint, including a large concentration in Arizona, where the company is headquartered.
The affected population was confirmed at 1,275,669 individuals. These were not anonymous records. They were patients who trusted an imaging provider with some of their most sensitive medical and personal data.
🧠 What Data Was Exposed
The investigation and public disclosures indicate that the accessed data varied by individual but included highly sensitive categories:
Personal identifiers and contact information
Medical and diagnostic records tied to imaging services
Social Security numbers for some patients
Health insurance and billing related data
Financial account and payment related information in certain records
Samples published by the attackers as proof included scans of identity documents, spreadsheets with patient and billing details, medical reports, and raw radiology images.
Even without public release of the full dataset, the exposure of this information created long term risk for identity theft, medical fraud, and targeted scams.
🎯 Attribution
Attribution in this case is unusually clear. The Medusa ransomware group publicly claimed responsibility, listed SimonMed on its extortion site, published proof samples, and set a deadline with a specific ransom demand.
Medusa operates as a ransomware as a service group and is known for data theft followed by extortion. Healthcare organizations have been frequent targets due to the sensitivity of patient data and the reputational pressure associated with leaks.
The SimonMed intrusion fits this pattern closely.
🛠️ SimonMed’s Response
Once suspicious activity was confirmed, SimonMed initiated containment actions that included password resets, strengthened authentication, deployment of enhanced endpoint monitoring, and removal of direct third party access to internal systems.
These actions appear to have prevented system wide encryption and allowed clinical operations to continue.
However, preventing encryption does not undo data theft. The organization still faced regulatory obligations, patient notification requirements, and legal exposure.
In October 2025, SimonMed began notifying all affected individuals and offered credit monitoring and identity protection services.
⚖️ Legal and Regulatory Pressure
The breach triggered regulatory scrutiny under healthcare privacy rules and led to multiple patient lawsuits alleging failure to protect sensitive data.
As in many breach cases, courts examined whether exposure alone constitutes harm or whether plaintiffs must demonstrate concrete misuse. Some claims were dismissed while others continued, reflecting the uneven legal landscape around data breach litigation.
Regulatory investigations typically move slowly, and the long term outcome remains unresolved.
💰 Impact and Aftermath
For patients, the breach created lasting uncertainty. Medical data does not expire, and even years later, stolen records can resurface in fraud schemes or targeted scams.
For SimonMed, the incident brought significant costs tied to investigation, remediation, notification, legal defense, and reputational recovery.
For the healthcare sector, the case reinforced several uncomfortable truths:
Outpatient providers are just as attractive as hospitals
Third party access is often the weakest link
Staying operational does not mean escaping harm
🛡️ How This Could Have Been Prevented
🔐 Final Takeaway
This was not a story about systems going dark. It was a story about data becoming leverage.
SimonMed remained operational, but more than a million patients still lost control of their personal and medical information. The attackers did not need to disrupt care to cause harm. They only needed access, time, and data.
The lesson is direct. In healthcare, cybersecurity is not only about uptime. It is about trust, confidentiality, and controlling every pathway that leads to patient data.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: