In December 2020, the world discovered that an IT management tool had become the delivery vehicle for one of the most far-reaching cyber-espionage operations in history. The Orion platform by SolarWinds, used by thousands of government and enterprise networks, was secretly weaponized.
Attackers slipped a malicious backdoor into a routine software update, turning a supply chain into an espionage highway. At least nine U.S. federal agencies and hundreds of global companies were infiltrated, marking a defining moment in modern cyberwarfare.
First time seeing this?
⚙️ How the SolarWinds Hack Worked
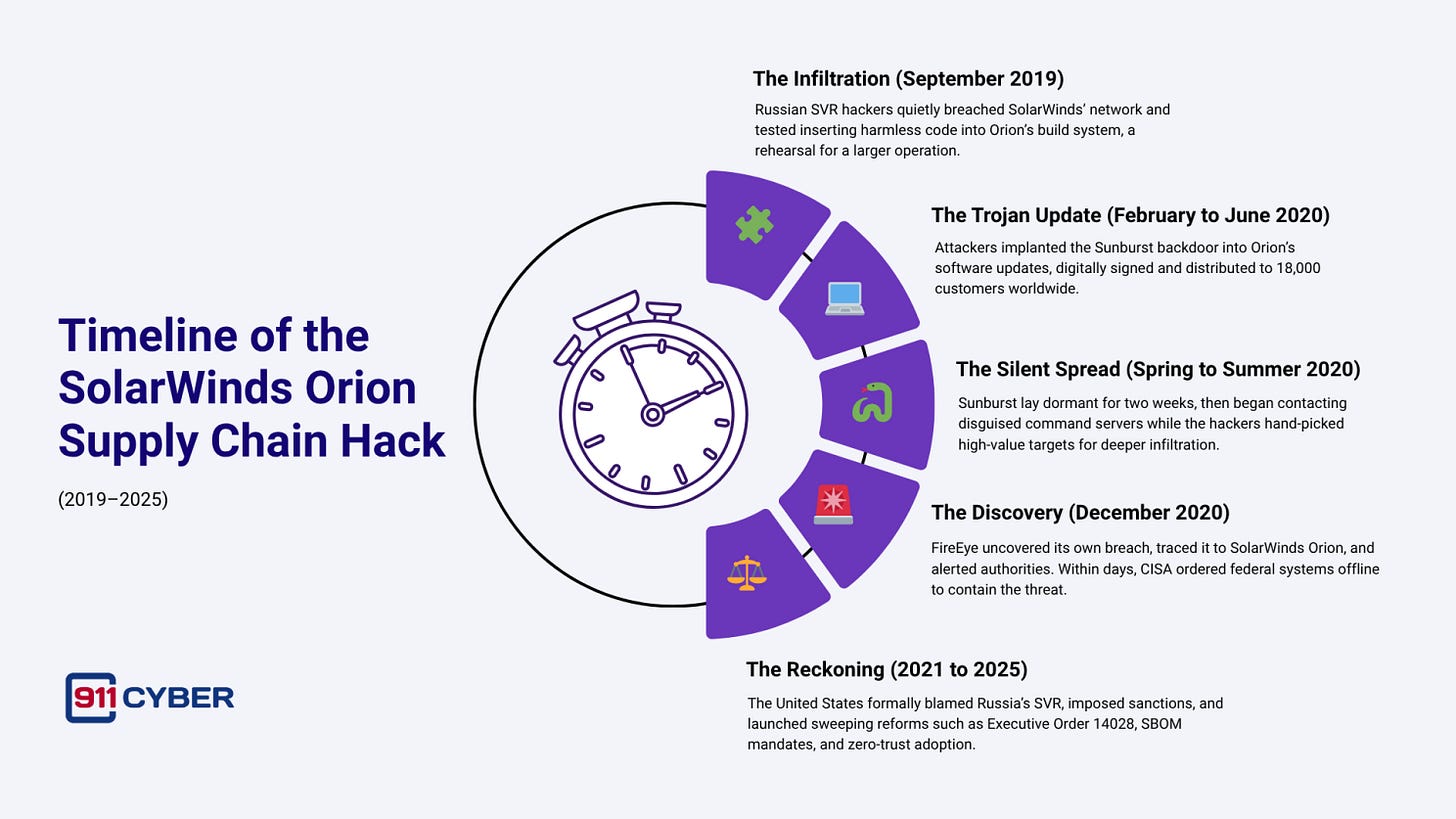
The attackers, later identified as Russia’s foreign intelligence service (SVR), breached SolarWinds’ development environment in 2019. They inserted malicious code, later called Sunburst, into Orion’s software updates between February and June 2020. When customers installed these updates, the malware quietly opened a backdoor that blended with normal network traffic.
After two weeks of dormancy, Sunburst began communicating with command servers disguised as legitimate SolarWinds traffic. From there, the attackers hand-picked high-value targets and deployed second-stage tools like Teardrop, which loaded penetration frameworks such as Cobalt Strike. Inside victim networks, they moved laterally, forged authentication tokens, accessed cloud systems, and exfiltrated sensitive data, often remaining undetected for months.
🗓️ Timeline of the SolarWinds Orion Supply Chain Hack
🌍 The Global Fallout
The infection touched an estimated 18,000 organizations. The attackers focused on a select few, including:
U.S. Federal Agencies: Treasury, Commerce, State, Defense, Homeland Security, Energy, Health and Human Services, and the Justice Department.
Technology Giants: Microsoft, Cisco, Intel, VMware, NVIDIA, and FireEye.
International Targets: UK government offices, NATO institutions, the European Parliament, and firms such as SAP and Telefonica.
In the Justice Department alone, about 3,000 Office 365 email accounts were compromised. Microsoft later revealed that attackers viewed portions of its source code repositories. The breach eroded trust across industries, exposing how a single supplier’s compromise could endanger global networks.
🧠 The Lessons
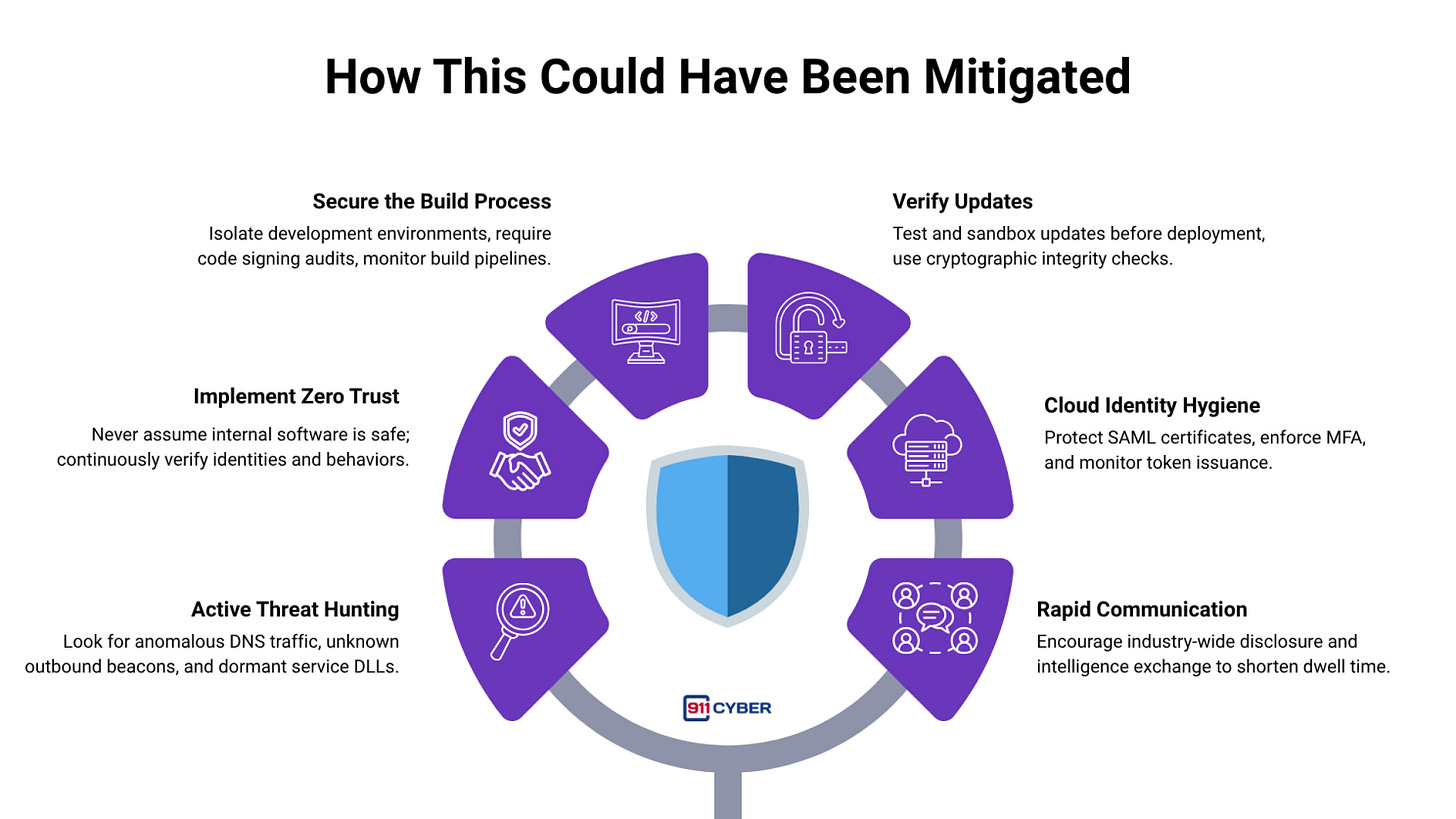
SolarWinds showed how attackers can weaponize the software update process itself. The backdoor used legitimate digital signatures, making detection nearly impossible with traditional defenses. It also throttled communications, mimicked real traffic, and only activated selectively to evade scrutiny.
The discovery came not from automated tools but from human intuition: FireEye’s analysts noticed an unusual login pattern inside their own network, a small anomaly that unraveled a global espionage campaign.
🚨 The Response
Immediate shutdown of Orion servers across agencies and enterprises.
CISA ordered federal systems offline and initiated forensics across all connected environments.
Microsoft, FireEye, and partners sinkholed the command-and-control domain to neutralize active infections.
Thousands of organizations rebuilt systems, rotated credentials, and audited all network connections.
Analysts warned that complete eradication could take years due to deep persistence mechanisms.
🎯 Attribution
In April 2021, the White House formally attributed the SolarWinds operation to Russia’s SVR (APT29, Cozy Bear). Analysts estimated the campaign involved at least 1,000 engineers and months of preparation.
The operation was espionage, not sabotage: its motive was intelligence collection. Russia denied involvement, but the consensus among Western governments and security experts remains firm that SVR conducted the operation.
⚖️ Legal Actions
Regulatory Action: In 2023, the U.S. SEC charged SolarWinds and its CISO with misleading investors about known security weaknesses before the breach.
Sanctions: The U.S. imposed sanctions on Russia, expelling diplomats and targeting companies linked to SVR operations.
Litigation: Investors filed class-action suits against SolarWinds for negligence and nondisclosure of vulnerabilities.
Policy Reform: The attack spurred Executive Order 14028, mandating Software Bills of Materials (SBOMs), secure coding practices, and multi-factor authentication for federal software suppliers.
🧩 Aftermath 2021–2025
Supply Chain Reforms: Global awareness of software supply chain risk led to new standards, NIST guidelines, and open-source security initiatives.
Zero Trust Adoption: Organizations accelerated zero-trust architecture to prevent trusted software from automatically accessing critical systems.
Threat Intelligence Sharing: The Joint Cyber Defense Collaborative (JCDC) and global CERT alliances improved rapid sharing of indicators and response coordination.
Transparency Norms: Mandatory incident reporting within 72 hours for critical sectors became law in 2022.
Ongoing Accountability: As of 2025, SolarWinds continues to face litigation and reputational rebuilding.
🛡️ How This Could Have Been Mitigated
🕊️ Final Takeaway
The SolarWinds hack was a Trojan hidden in plain sight. A single compromised update rippled through governments, corporations, and global infrastructure, proving that trust is both the greatest asset and the greatest vulnerability in cybersecurity.
It reshaped how nations and industries secure their code, validate their vendors, and disclose their risks. The lesson endures: even a routine update can become the doorway to an espionage campaign. Vigilance, transparency, and secure-by-design development remain the only true defenses against the next SolarWinds.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: