In mid-2024, one of the cloud’s most trusted data platforms, Snowflake, became the silent epicenter of a massive cyberattack. Not due to a flaw in its architecture, but because of overlooked basics: stale passwords, absent MFA, and misconfigured accounts. Over 160 organizations across telecom, finance, entertainment, healthcare, and education had their most sensitive data siphoned off, terabytes at a time. And the attackers? Not nation-state actors, but a North American extortion crew that used stolen credentials to walk in the front door.
This edition of Cybercrime Stories dives deep into how a perfect storm of infostealers, credential reuse, and poor cloud hygiene led to the breach of a platform entrusted by the Fortune 500.
First time seeing this?
❄️ What is Snowflake?
Snowflake is a cloud-native data warehousing and analytics platform used to store and analyze large datasets across AWS, Azure, and Google Cloud. It serves as the data backbone for over 9,500 organizations, including AT&T, Santander Bank, and Ticketmaster, enabling everything from machine learning to business reporting. Snowflake operates on a shared responsibility model: while it secures the platform, customers are responsible for managing access controls, passwords, and multifactor authentication (MFA).
⚠️ The Incident
In April 2024, threat actor group UNC5537 (aka “Scattered Spider”) launched a sweeping credential-based attack campaign targeting Snowflake customer accounts. The attackers didn’t exploit Snowflake’s software. Instead, they used infostealer malware like Lumma and RedLine to harvest credentials from employee and contractor devices.
These credentials, some dating back to 2020, lacked MFA and had never been rotated. With valid logins in hand, the attackers accessed Snowflake-hosted databases undetected, stealing sensitive records and demanding ransoms. By the time the attack was uncovered, data from over 165 customers, including 560M Ticketmaster records and 110M AT&T call logs, had already been exfiltrated.
🛑 The Hack
Initial Access:
Attackers used infostealer malware to collect valid Snowflake login credentials. One major entry point was an infected EPAM Systems contractor laptop.
MFA Disabled:
All breached accounts lacked multi-factor authentication, relying solely on usernames and passwords.
Reused & Stale Passwords:
Many stolen credentials had been valid for years. Attackers used these to log into Snowflake accounts via web and CLI interfaces.
Tooling & Automation:
A custom tool, “Frostbite” (or “rapeflake”), was deployed to automate reconnaissance across compromised accounts, listing users, roles, tables, and IP addresses.
Exfiltration:
Data was extracted in bulk using SQL queries and legitimate clients like DBeaver. Entire schemas, often terabytes, were pulled.
Lack of Monitoring:
Most customers failed to detect the unusual login patterns, allowing exfiltration to go undetected for weeks.
No Platform Vulnerability:
Snowflake’s infrastructure was not exploited. This was a credential-based breach enabled by poor cloud configuration and hygiene.
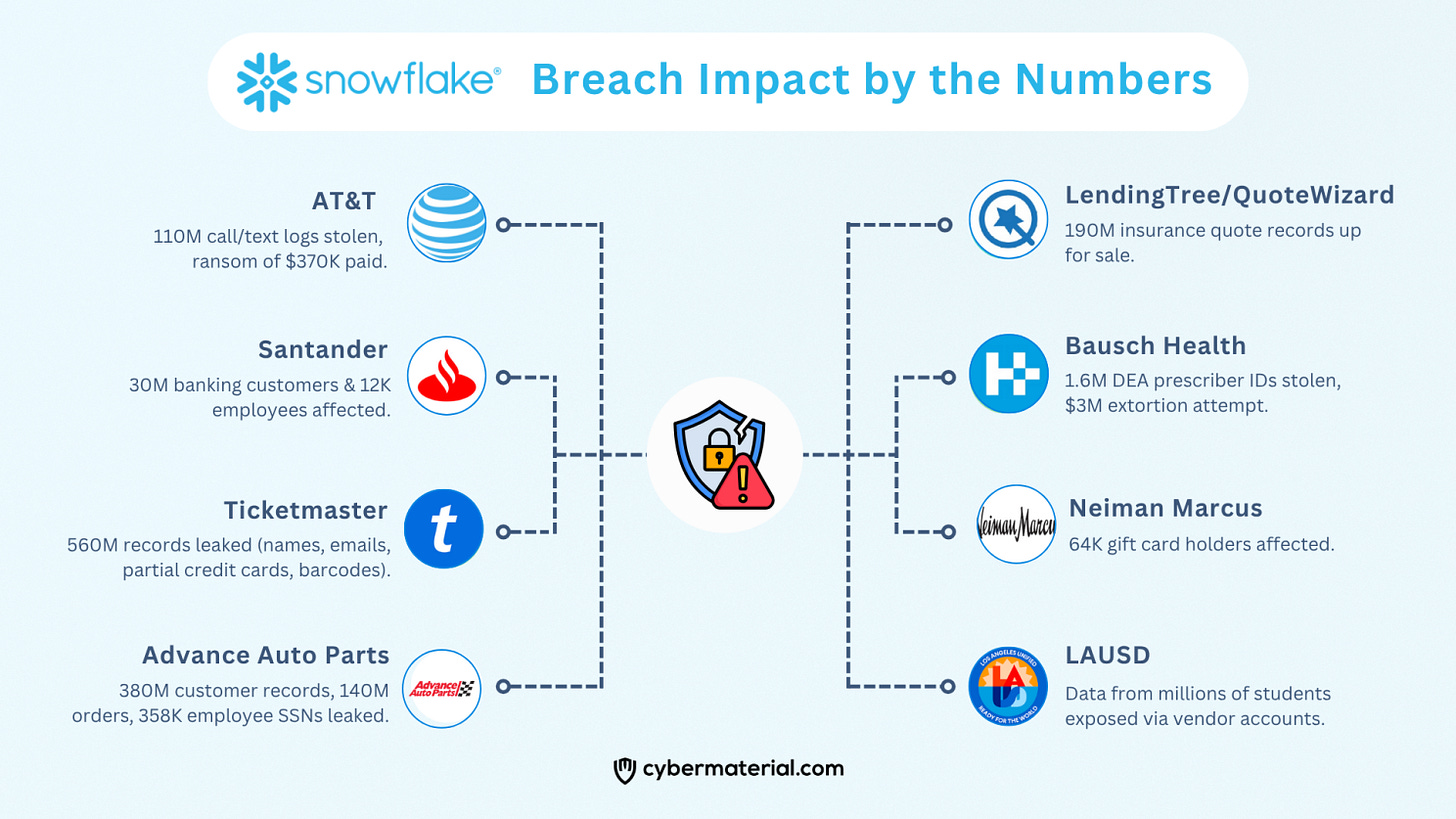
🛡️ The Impact
The breach hit a cross-section of industries, with staggering data volumes and sensitive content:
AT&T: 110M call/text logs stolen, ransom of $370K paid.
Ticketmaster: 560M records leaked (names, emails, partial credit cards, barcodes).
Santander: 30M banking customers & 12K employees affected.
Advance Auto Parts: 380M customer records, 140M orders, 358K employee SSNs leaked.
LendingTree/QuoteWizard: 190M insurance quote records up for sale.
Bausch Health: 1.6M DEA prescriber IDs stolen, $3M extortion attempt.
Neiman Marcus: 64K gift card holders affected.
LAUSD: Data from millions of students exposed via vendor accounts.
In total, over a billion individual records were compromised across sectors.
✅ The Response
Snowflake:
Enforced MFA on customer accounts by default.
Issued technical advisories with CrowdStrike and Mandiant.
Released detailed detection and mitigation guides.
Repeatedly stated that no platform-level vulnerability was involved.
Law Enforcement:
Connor Riley Moucka (Canada) and John Erin Binns (U.S./Turkey) were identified as core members of UNC5537.
Moucka arrested in Ontario (Oct 2024); extradition approved.
Binns remains in Turkish custody as of June 2025.
FBI and DOJ continue international investigations.
Regulatory and Legal Fallout:
Class actions were filed against Snowflake and its breached clients.
Snowflake’s “shared responsibility” model scrutinized by regulators.
CISA, DOJ, and security firms issued warnings on cloud account misconfiguration.
🔍What to Do to Protect Your Organization
If your organization uses Snowflake or similar platforms:
Enable MFA for all users, and make it mandatory.
Rotate all old credentials, especially those from pre-2023.
Audit account access and query logs immediately.
Implement IP restrictions and session alerts.
Harden vendor and contractor controls, especially endpoint security.
🔐 Takeaways for Businesses
The Snowflake breach underscores that in cloud computing, identity is the perimeter. The absence of MFA and reliance on old passwords made hundreds of enterprises vulnerable, despite Snowflake’s robust infrastructure. It’s a cautionary tale on cloud misconfiguration, weak IAM practices, and supply chain risks. Even top-tier platforms cannot defend against poor customer-side controls. Cloud security is a shared responsibility, this incident proves that neglecting your side of the bargain can cost you millions.
🌍 Takeaways for Individuals
Even if you’re not a Snowflake customer, your data may still be at risk if it’s held by companies that are. This breach demonstrates that your personal information is only as secure as the weakest link in the data chain. Be vigilant:
Regularly monitor your accounts for suspicious activity.
Use identity protection services if offered.
Push for better security standards at the companies you do business with.
Breaches don’t just affect companies; they cascade into the lives of millions. Cloud convenience must not come at the cost of basic security hygiene. The Snowflake saga proves that strong encryption can’t protect you if weak credentials open the vault.
Stay tuned as we uncover more real-life digital horrors on Cybercrime Stories.
Subscribe and Comment.
Copyright © 2026 911Cyber . All Rights Reserved.
Follow 911Cyber on: