📸 What Does a Picture Reveal About You?
The Illusion of “It’s Just a Photo”
A single image can expose far more than most people realize.
Your face reveals biometric markers.
Your background reveals location clues.
Your clothing and devices reveal socioeconomic signals.
Your companions reveal your social graph.
Your home interior reveals security posture.
Even without GPS metadata, architecture, vegetation, terrain, weather patterns, and signage can help infer location.
You may think you are sharing a memory.
In reality, you are sharing identifiers.
The illusion is believing that a photo is just a visual moment.
In the AI era, it is a data asset.
🏢 What Happens After You Upload It?
When you upload an image to a platform, you do not simply share it. You transfer control.
Most users assume:
The company will exist indefinitely
The privacy policy will remain stable
The data will stay contained
History shows otherwise.
Companies get acquired.
They pivot business models.
They go bankrupt.
They sell assets.
When a startup is acquired by a larger AI company such as OpenAI, datasets often become part of a broader ecosystem.
In bankruptcy cases, user databases can be treated as assets.
The platform you trusted today may not resemble the entity controlling your data tomorrow.
And your consent rarely travels with ownership changes in a meaningful way.
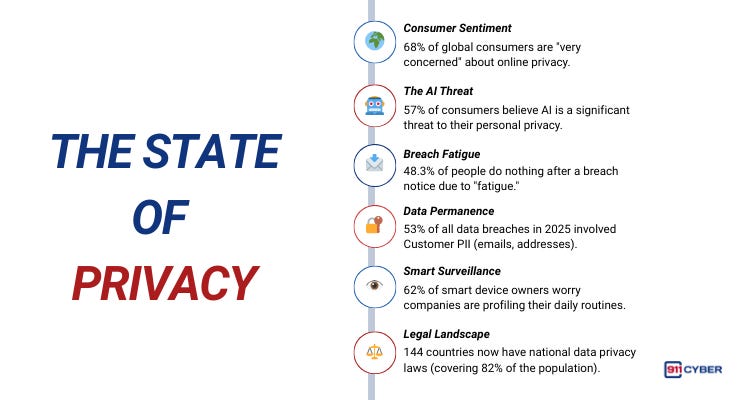
📊 The State of Privacy
🤖 What Are the New AI Capabilities?
AI Geolocation + Profiling = Compounding Risk
AI systems no longer rely solely on metadata.
Platforms such as GeoSpy demonstrate that location can be inferred from pixels alone.
Modern computer vision can:
Estimate geographic location
Identify recurring faces across platforms
Build behavioral patterns
Detect objects and valuables
Model your daily environment
Individually, a photo seems harmless.
Collectively, hundreds of uploads enable precision profiling.
Attackers no longer need to break into your systems.
They analyze what you voluntarily provided.
The risk compounds over time.
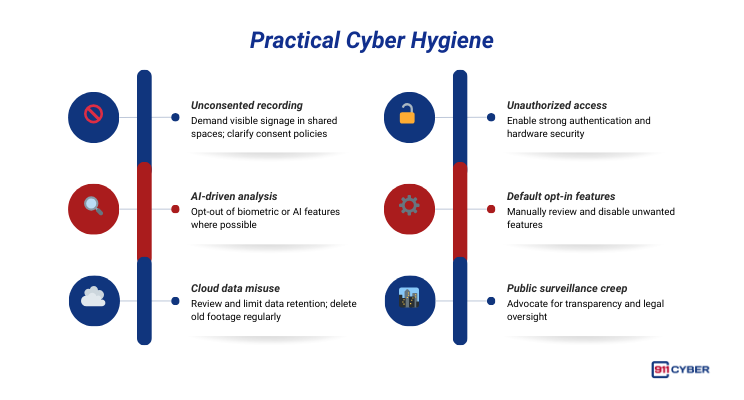
🛡️ What Can You Do About It?
🧰 What Resources Are Available to Help?
📚Books
You Are Not a Gadget by Jaron Lanier
AI Snake Oil by Arvind Narayanan & Sayash Kapoor
🎙️ Podcasts
About Face (Recognition) | How I Fix the Internet by Kashmir Hill
At face value: Facial recognition technologies and privacy on Info Matters Podcast by Cynthia Koo
Malicious Life Podcast: Should Law Enforcement Use Facial Recognition? Pt. 1 with Ted Claypoole, Yossi Naar and Ran Levi
▶️ Videos
🔒 Final Thoughts
The Internet doesn’t forget, and it doesn’t forgive.
We often blame platforms for invading our privacy, but the harder truth is that we volunteered the data. AI systems never stop learning, and the internet rarely deletes.
The question isn’t whether you trust today’s platform. The question is whether you trust every future version of it. Before you upload that next “harmless” photo, pause. Your privacy starts with you.